What Makes PAS Modernization Different From Every Other Legacy Program
North American carriers are spending $10.5B on core IT modernization between 2024 and 2026 [2]. The results, in McKinsey’s assessment, have been “mixed, with many carriers not fully realizing expected returns” [1].
That gap between investment and outcome is a decision problem, and it starts with what kind of system a PAS actually is.
What is a policy administration system? A policy administration system (PAS) is the core software platform that manages the full lifecycle of every insurance policy a carrier writes: quoting, binding, issuance, endorsements, renewals, cancellations, billing integration, and claims handoff. Every in-force policy, every day, runs through it, with no tolerance for behavioral deviation or unplanned downtime.
A PAS is not a generic enterprise application. Rating logic that determines premium is embedded in it. State-specific filing rules, bureau rate integrations, underwriting exceptions, and DOI compliance requirements are encoded in it, often over decades, often without documentation.
When a PAS behaves incorrectly after modification, the consequences extend beyond a software defect to regulatory exposure, actuarial liability, and direct financial impact on the book of business.
What is PAS comprehension? PAS comprehension is the practice of fully mapping a legacy policy administration system’s embedded business rules, state filing logic, rating algorithms, and integration dependencies before any modernization path is committed. It is the prerequisite step that determines whether replacement or modernize-in-place is the lower-risk choice for a specific carrier. It is also the step that most failed programs skipped.
On legacy PAS, launching a new product line takes 18 to 24 months on average. Carriers absorb 70 to 80% of their IT budgets in maintenance overhead just to keep these systems running (Celent). Insurance legacy system modernization is consequently one of the highest-stakes programs an IT organization can undertake.
This article serves three carrier populations:
- Pre-decision carriers still on legacy PAS, evaluating replacement vs. modernize-in-place against a vendor market that almost universally recommends replacement
- Mid-replacement carriers years into a commercial platform program, over budget, running both systems simultaneously, reassessing whether to continue or pivot
- Carriers with deeply customized PAS environments containing irreplaceable embedded logic for whom commercial replacement is structurally problematic, regardless of what the platform vendor’s implementation estimate says
The market produces content almost exclusively for the first group. This article gives all three a decision framework grounded in evidence.
PAS Modernization Options in 2026: Replacement, Modernize-in-Place, and Hybrid
The replace-vs.-modernize decision is routinely framed as a question of ambition: carriers that want modern capabilities replace; carriers that lack the appetite modernize. That framing is commercially motivated and operationally wrong.
The correct framing is carrier-profile fit: which path aligns with the system’s actual characteristics, its embedded logic density, and the carrier’s tolerance for the specific risk profile each path carries.
- Replacement is rip-and-replace with a commercial platform: Guidewire, Duck Creek, Majesco, BriteCore, among others. The carrier migrates its book of business, reconfigures its products, and decommissions the legacy PAS. The platform provides standard functionality out of the box; customization is applied on top.
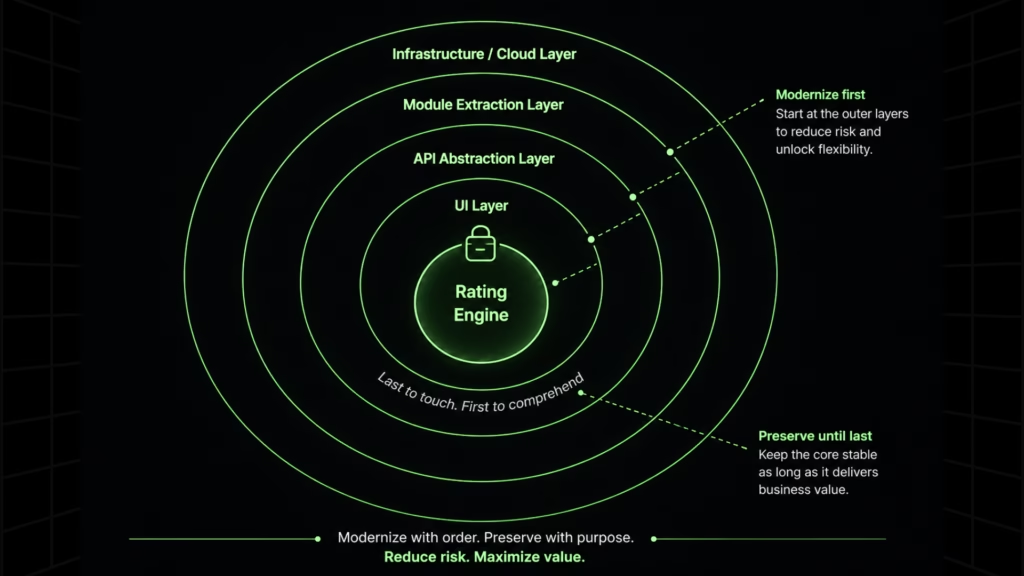
- Modernize-in-place is the incremental improvement of the existing PAS: API-wrapping legacy modules, modernizing the UI layer, extracting discrete functions into services, migrating infrastructure to cloud, while preserving the rating engine, state filing logic, and embedded product configurations that define the system’s actual value. Incremental modernization is the only approach that lets carriers improve capability while policies are in force.
- Hybrid replaces commodity modules (billing, document management, digital front-end) while preserving and modernizing the core PAS that contains irreplaceable logic.
PAS Replacement vs. Modernization: Path Comparison
| Approach | Timeline | Cost Range | Risk Profile | Best-Fit Carrier |
| Commercial Platform Replacement | 3 to 5 years | $10M to $100M+ | Highest: scope expansion, dual-system trap, data migration | Standard product portfolios where embedded logic is replicable in the platform without custom development |
| Modernize-in-Place | 12 to 24 months for meaningful first-phase delivery | Significantly lower; no platform licensing | Moderate: comprehension prerequisites must be met; parity validation is non-negotiable | Carriers with 20 to 40 years of custom rating rules, state-specific filing logic, and bureau integrations no commercial platform covers |
| Hybrid | 18 to 36 months | Moderate | Moderate: boundary definition between replaced and preserved modules is the critical risk | Carriers needing digital front-end capabilities without destabilizing the core rating engine |
BCG documents the upper end of the replacement risk range with two named cases: a Central European insurer whose program ran for eight years and produced a write-off exceeding $500M; a Southern European insurer whose claims platforming program completed 500% over budget [2].
Both trace to the same root cause: the programs began without sufficient understanding of what the legacy system contained. Neither could complete cutover because the new system could not replicate what the legacy system contained, leaving the carrier running both platforms indefinitely.
Practitioners call this the dual-system trap, and it is the most consistent way PAS replacement programs destroy the ROI case that justified them.
The financial framework for the alternative path comes from the Tokio Marine Group CIO, writing in Carrier Management (March 2026): $300M for full system replacement versus a modernization program delivering 80% of the benefit at 10 to 20% of the cost, with business value years earlier [3].
Top PAS Vendors in 2026: Where Guidewire, Duck Creek, Majesco, and BriteCore Fall Short for Custom Logic Carriers
Four vendors dominate the commercial platform market. Understanding what each is built for, and where each reaches its limits is necessary before any replacement evaluation begins.
- Guidewire is the market leader for large P&C carriers, with deep functionality across PolicyCenter, BillingCenter, and ClaimCenter. It targets carriers with complex, multi-line operations and the implementation budget to match. Standard configuration covers most commercial lines and personal lines products for carriers with relatively standardized portfolios.
- Duck Creek serves mid-to-large P&C carriers with a configurable, cloud-native architecture. Its strength is speed-to-market for carriers whose product logic fits within the platform’s configuration model. It is widely used for carriers launching new products on standard forms.
- Majesco focuses on mid-market carriers, MGAs, and specialty insurers, with a lower implementation cost profile than Guidewire or Duck Creek. Its cloud-first architecture makes it attractive for carriers modernizing infrastructure alongside core systems.
- BriteCore targets smaller carriers and mutuals with a SaaS model and lower entry cost. It suits carriers with straightforward product portfolios and limited custom rating logic.
The Shared Limitation
Each of these platforms is built around the same assumption: that a carrier’s product logic can be expressed through the platform’s configuration model. For carriers with standard commercial lines and personal lines portfolios, that assumption holds reasonably well.
For carriers whose PAS contains 20 to 40 years of accumulated state-specific rating rules, bureau rate deviation logic, carrier-specific underwriting exceptions, and product configurations built across multiple DOI filings, it does not.
Replicating that logic through platform configuration is not a scoping exercise. It is custom development, and it begins accumulating the moment the implementation team encounters a business rule the platform’s configuration model cannot express natively.
| Vendor | Primary Market | Configuration Strength | Where Custom Logic Breaks Down |
| Guidewire | Large P&C carriers | Deep multi-line functionality | State-specific rating deviations and bureau integrations require Gosu scripting at scale |
| Duck Creek | Mid-to-large P&C | Cloud-native configurability | Carrier-specific underwriting exception logic exceeds the configuration boundary quickly |
| Majesco | Mid-market, MGAs, specialty | Faster implementation | Custom actuarial algorithms require platform extensions that add cost and timeline |
| BriteCore | Small carriers, mutuals | Low-cost SaaS entry | Limited capacity for complex multi-state rating logic or bureau rate integrations |
Carriers evaluating these platforms on implementation cost and timeline are asking the right question about the wrong variable. The question that determines program success is how much of the legacy PAS’s embedded logic falls outside the platform’s native configuration scope. Carriers who do not answer that question before signing contracts are the ones who fund the BCG case studies [2].
Carriers whose PAS contains irreplaceable custom logic are not, in practice, in the replacement market. They are in the modernize-in-place market, whether the vendor landscape has told them so or not.
Before committing to a platform that cannot replicate your custom logic, get a system-level view of what your PAS actually contains. Request your $0 Assessment.
The Rating Engine Problem: Why It Is the Hardest Component to Modernize or Replicate
The rating engine is the component every PAS modernization program eventually collides with, and the one almost none of them adequately prepare for.
A carrier’s rating engine is not a module that can be replaced with a comparable alternative. It is an accumulation. State-specific actuarial algorithms calibrated to individual DOI filings. Bureau rate integrations (ISO, NCCI, AAIS) with carrier-specific deviation logic layered on top, reflecting historical rate filings, approved deviations, and market-specific underwriting decisions.
Product configurations across multiple lines of business that encode decades of actuarial judgment, exception handling, and regulatory negotiation. No two rating engines are alike, and most have not been fully documented since the engineers who built them were on staff.
Why Commercial Platforms Cannot Replicate It
The configuration models of every major commercial PAS platform are built around the assumption of standardized rating logic: bureau rates plus a defined set of carrier modifications.
For carriers whose rating engine reflects 30 years of state-specific deviation from those standards, the platform’s configuration boundary is reached quickly.
What follows is custom development:
- Gosu scripts in Guidewire,
- Custom extensions in Duck Creek,
- Platform-specific workarounds in Majesco.
Each adds implementation cost, extends timeline, and creates a new layer of undocumented logic on top of the platform the carrier just paid to standardize on.
The carriers who discover this mid-program are the ones who did not map their rating engine before selecting a platform. By the time the scope of custom development becomes clear, contracts are signed and the program is committed.
Why the Rating Engine Must Be Comprehended First and Touched Last
Two principles apply to every PAS modernization program that involves the rating engine.
First, it must be fully comprehended before any path is committed. A complete catalog of every rating algorithm, table, factor, and rule across all products, states, and lines of business is the prerequisite condition for responsible path selection, not a deliverable that comes out of the program.
Carriers who treat this catalog as the program’s output rather than its input discover mid-transformation that the scope they estimated bears no relationship to the system they actually have.
Second, the rating engine should be the last component touched, not the first. API abstraction, UI modernization, and module extraction can all proceed while the rating engine remains in place.
Preserving it while modernizing around it is the approach that maintains regulatory continuity and avoids the parity validation failures that trigger DOI inquiry. The rating engine is modernized only once the rest of the program has produced the dependency map, the business rule catalog, and the validated parity baseline it requires.
Why PAS Modernization Programs Fail Before Transformation Begins
The BCG failure cases share a root cause the financial post-mortems rarely name directly: the programs began transformation before the system was understood. This is not a project management failure. It is a structural deficit, and it is the most consistent reason PAS modernization programs fail, regardless of path.
In legacy PAS environments, critical business rules exist in one of two places: in code nobody has read in a decade, or in the heads of engineers approaching retirement.
KPMG Canada (March 2026) documents the pattern: aging employees are maintaining older, disconnected systems with limited documentation and dwindling expertise [4]. When those engineers leave, the institutional knowledge leaves with them.
PAS is among the most tightly coupled software in any enterprise, with rating, billing, claims, and state filing deeply interdependent. Undocumented logic in one module has behavioral consequences across others. Those consequences surface mid-transformation, when reopening the closed scope is the only option.
The compounding technical debt that makes legacy PAS maintenance costs self-reinforcing is the visible problem. The comprehension debt underneath it is the accumulated gap between what the system does and what anyone can articulate about it. That gap is what ends programs.
Why PAS Implementations Fail: Six Failure Modes
- Undocumented rating and underwriting logic discovered mid-program. Scope expands when the modernization team encounters business rules that exist only in code. Timelines slip. Budgets reforecast.
- Scope explosion in commercial platform customization. When embedded logic cannot be replicated through standard configuration, custom development begins and the platform’s speed-to-market advantage disappears.
- Data migration paralysis, particularly for closed books of business. Carriers endure legacy maintenance costs for years rather than face migrating policy history no current team member fully understands.
- Regulatory continuity gaps at cutover. Any disruption to bureau rate table integrity, state-specific rating factor records, or DOI-required audit trails during cutover triggers regulatory exposure, not a software defect.
- Loss of institutional knowledge when senior PAS developers depart. The system’s de facto documentation retires with them.
- Dual-system operating costs that erode ROI before the new system is live. Carriers absorbing the cost of two systems simultaneously have already surrendered the financial case that justified the program.
Before any path is committed, a genuine PAS comprehension exercise must produce: a dependency and module map, a business rule catalog across all products and states, a state filing logic inventory, an integration registry, and a risk-weighted modernization readiness view. Without these, both paths carry materially higher risk than the program plan acknowledges.
The comprehension gap is solvable before transformation begins. See how Legacyleap’s Assessment and Documentation Agents produce the dependency map, business rule catalog, and state filing logic inventory your program requires before any path commitment.
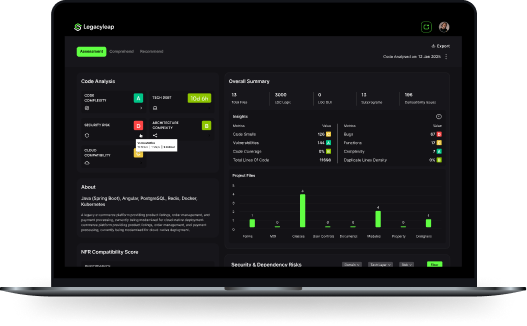
How Legacyleap Makes the Modernize-in-Place Path Executable at Enterprise Scale
Legacyleap operationalizes the comprehension-before-transformation principle as a governed, multi-agent platform. It requires full source code and dependency visibility before any transformation begins: not file-level code suggestions, but system-level comprehension at the scale a legacy PAS requires.
Assessment Agent
Most carriers begin PAS transformation without knowing where their undocumented rating rules live, which modules are safe to touch, or what the state filing logic actually contains.
The Assessment Agent produces this map before any transformation decision is made: module boundaries, dependency graph, embedded business rule locations, state filing integrations, rating engine logic, and risk indicators weighted by complexity and change impact.
The output is what the replace-vs.-modernize decision requires.
For carriers considering replacement, it surfaces the scope of custom logic that replacement would require replicating and reframes the financial comparison accordingly.
For carriers already on the modernize-in-place path, it sequences the program before engineering begins.
Documentation Agent
When a senior PAS developer retires, the institutional knowledge of how the system actually works retires with them.
The Documentation Agent reconstructs this knowledge from the source code itself:
- Rating algorithms,
- Product configurations,
- Underwriting exception logic,
- State-specific filing rules, and
- DOI compliance requirements,
…without depending on engineers who are still employed.
This directly addresses the retirement risk KPMG Canada documents [4]. It produces a structured, auditable business rule inventory from the code itself: the artifact regulators, actuaries, and program sponsors require before any transformation begins.
It also establishes the boundary logic for the platform-vs.-services decision at the center of every PAS modernization program: which logic must be preserved, which can be reconfigured, and which is safe to replace.
Modernization Agent
The Modernization Agent applies diff-based, human-reviewed code transformations. No AI-generated change can be merged, deployed, or executed without engineer review and approval at defined checkpoints. All transformations are reversible. The carrier retains engineering control at every step.
Supported legacy stacks span the full range carriers typically run: .NET environments (VB6, Web Forms, WCF, Classic ASP, ADO.NET, MVC) and Java environments (Java EE, EJB, JSP/Servlets, Struts, AngularJS). Modernization targets include .NET 6+/8, ASP.NET Core, Spring Boot, REST/gRPC, Angular, and React.
QA Agent
Regulators, actuaries, and boards require proof that the modernized system produces identical rating outputs, billing calculations, and regulatory filing results before authorizing cutover. The QA Agent delivers this proof as an automated validation layer, not a manual testing exercise conducted at the end of the program.
The industry practitioner benchmark is a ±1% rate tolerance test across all products, states, and lines of business. Most carriers fail to establish this baseline before committing to a path. The QA Agent produces the audit trail that satisfies DOI requirements and the parity evidence that satisfies actuarial sign-off, before any go-live decision is made.
The $0 Modernization Assessment
The $0 Modernization Assessment is the entry point for carriers at any stage of the replace-vs.-modernize evaluation. It produces the dependency map, business rule inventory, state filing logic summary, risk indicators, and modernization readiness view before any path commitment.
For pre-decision carriers, it makes the decision evidence-based. For mid-replacement carriers, it establishes what the in-place path requires from the current state. For carriers with deeply customized environments, it quantifies the custom logic density that replacement proposals rarely account for accurately.
The output connects directly to the application modernization ROI framework for justifying long-term PAS investment: parity validation and comprehension are not overhead. They are what make the modernized system deployable without regulatory exposure.
State Filing Compliance and Data Migration: The Two Risks That End PAS Programs
Insurance is state-regulated. PAS modernization must maintain unbroken compliance with state filing requirements throughout the entire program lifecycle, not just at cutover.
Bureau rates, forms, and rules filed with state DOIs must remain intact and auditable at every stage. NAIC Model Law compliance and state-specific DOI rules are continuous requirements.
State regulators require complete, time-stamped audit trails of every rating change, with “as-of” reconstruction capability: the ability to reproduce the premium calculated for a specific policy on a specific date under the rules then in effect.
Any disruption to bureau rate table integrity or DOI-required audit trails during modernization is not a software defect. It is a regulatory compliance breach that triggers DOI inquiry, potential market conduct examination, and financial exposure that extends well beyond the modernization program’s budget.
The Documentation Agent’s business rule catalog and the QA Agent’s parity validation output are the mechanisms that keep this requirement met through every transformation step.
Data Migration: The Closed Book Problem
Legacy PAS databases contain decades of policy history, and migration requires zero-loss data preservation. The migration risk practitioners consistently identify as most paralyzing is not active policy data. It is the closed books of business.
Terminated policies still require records access for regulatory examination, litigation, reinsurance audits, and actuarial analysis. Carriers consistently absorb legacy maintenance costs for years rather than face the migration of policy history they cannot afford to lose or corrupt.
The data characteristics that compound this risk are specific to PAS environments:
- Undocumented data structures from system versions that predate current team tenure
- Non-standard free-text clauses inserted by underwriters over years, without schema enforcement
- Legacy policies that predate compliance standards now built into the target system, each requiring exception handling
- Multi-system policy history where older records were migrated from prior legacy systems and carry forward earlier data quality issues
Version-controlled migration with rollback options and phased cutover by line of business or state are baseline requirements for any credible PAS modernization program.
PAS Modernization in 2026: The Cost of Delay
KPMG’s 2025 Insurance CEO Outlook documents that 73% of insurance CEOs name AI as a top investment priority with return expectations within one to three years, and that employee retirement is their top labor concern [5].
Those two data points describe the same problem from opposite ends: the competitive pressure to deploy AI-driven capabilities is accelerating while the institutional knowledge required to modify the systems those capabilities must integrate with safely is retiring.
Legacy PAS architecture cannot support the data fluidity, governance, and orchestration that AI integration requires. Modernization is the prerequisite for every AI and digital initiative on the carrier’s strategic plan, not a parallel program.
Carriers delaying PAS modernization are compounding the gap between their AI investment intentions and their infrastructure’s ability to deliver on them.
Two paths are defensible in 2026.
- If your product portfolio is not heavily customized, your state filing logic is replicable through standard configuration, and your embedded underwriting rules fall within the platform’s configuration scope, evaluate replacement with the BCG failure case evidence in front of you [2]. The risks are documented and manageable with proper comprehension and governance infrastructure in place before the program begins.
- If your PAS contains irreplaceable embedded logic: state-specific rating rules built over 20 to 40 years, bureau rate integrations with carrier-specific deviation layers, product configurations no implementation team has fully documented, the modernize-in-place path is the more defensible, faster-ROI, and lower-risk choice. The Tokio Marine CIO benchmark is the right financial frame: 80% of the benefit at 10 to 20% of the cost, with business value years earlier [3].
In either case, the decision begins with understanding what the system contains.
How long does PAS modernization take? Replacement: 3 to 5 years, with documented cases extending to 8 years when scope expands mid-program. Modernize-in-place with proper comprehension infrastructure: meaningful first-phase delivery within 12 to 24 months.
Request a $0 Assessment to produce the dependency map, business rule catalog, state filing logic inventory, and modernization readiness view the replace-vs.-modernize decision requires, before any path commitment.
Book a Demo to see how Legacyleap produces your dependency map, business rule catalog, and state filing logic inventory in a live walkthrough with engineers who understand insurance PAS environments.
FAQs
In a modernize-in-place program, in-force policies remain on the existing PAS throughout the transformation. Modernization proceeds incrementally (API abstraction, UI layer, module extraction) without migrating active policy records until parity validation is complete and a controlled cutover is authorized. This is one of the core advantages of the in-place path over replacement: the book of business is never at risk during the transformation itself.
The dual-system trap occurs when a replacement program cannot complete cutover because the new platform cannot replicate the embedded logic the legacy PAS contains. Both systems continue running simultaneously. The carrier absorbs the cost of two platforms while neither fully serves the book of business. The original ROI never materializes. The BCG cases documenting an $500M+ write-off and a 500% over-budget claims program are both examples of this pattern.
Yes, with the right architecture. The prerequisite is that the AI operates at the system level, parsing the full source codebase to reconstruct business rules from code rather than from documentation that does not exist. File-level AI tools that generate code suggestions cannot do this. A platform like Legacyleap uses a Documentation Agent specifically to extract and catalog undocumented rating algorithms, state filing logic, and underwriting exception rules from legacy source code before any transformation begins.
The industry benchmark is a ±1% rate tolerance test across all products, states, and lines of business. This requires running identical inputs through both the legacy and modernized systems and comparing outputs systematically, not spot-checking. The QA Agent automates this validation process, producing a complete parity report and audit trail that satisfies DOI requirements and actuarial sign-off standards. Manual testing at the scale a multi-state, multi-line PAS requires is not a credible substitute.
The first step is an honest assessment of why the program is stalled. In most cases, the root cause is undocumented logic in the legacy PAS that the platform cannot replicate through standard configuration, which means the program is accumulating custom development scope that was not in the original estimate. Carriers in this position have three options: continue and absorb the expanding cost; negotiate a reduced scope that accepts functional loss; or pivot to a modernize-in-place approach that preserves the embedded logic the platform could not replicate. The $0 Modernization Assessment was designed specifically for carriers at this decision point. It maps what the legacy system contains and establishes what a modernize-in-place path would require from the current state.
References
[1] McKinsey & Company (May 2025). P&C Core Systems Modernization.https://www.mckinsey.com/industries/financial-services/our-insights/property-and-casualty-insurance-core-systems-modernization
[2] BCG, Boston Consulting Group (2024). North American Insurance Core IT Modernization.https://www.bcg.com/publications/2024/modernizing-insurance-core-it-systems
[3] Tokio Marine Group CIO, Carrier Management (March 2026).https://www.carriermanagement.com/features/2026/03/tokio-marine-cio-modernization
[4] KPMG Canada (March 2026). Modernizing Legacy Systems for Insurers.https://kpmg.com/ca/en/home/insights/2026/03/modernizing-legacy-systems-insurers.html
[5] KPMG (January 2026). 2025 Insurance CEO Outlook.https://kpmg.com/xx/en/our-insights/ai-and-technology/2025-insurance-ceo-outlook.html