Cyber Insurance Requirements for Legacy Systems: Why Underwriters Are Now Measuring Applications, Not Controls
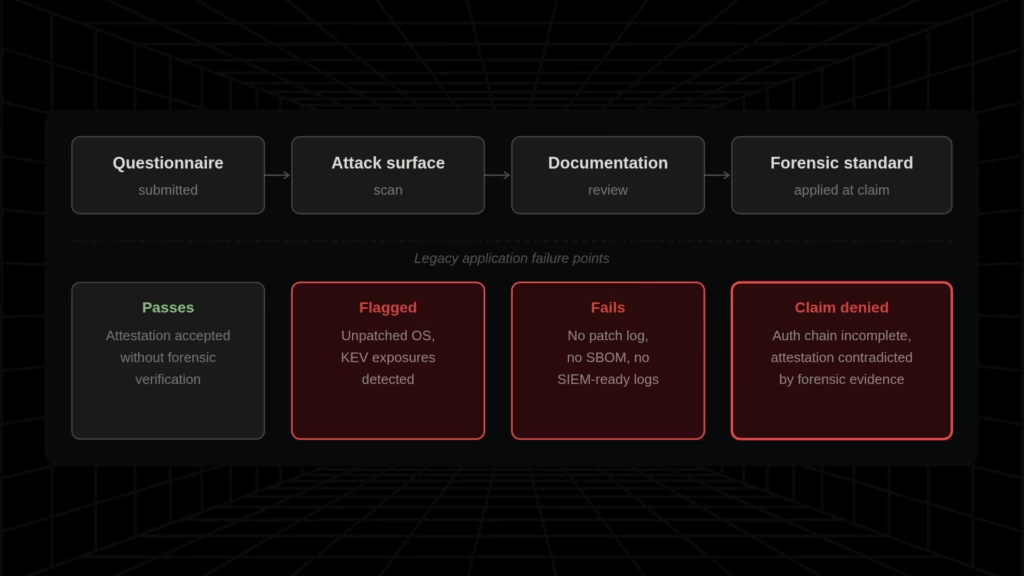
The cyber insurance market has undergone a structural reset. What was once a documentation exercise (attest to your controls, sign the application, renew) is now a forensic standard. The shift happened because claims did. Carriers absorbed losses that forced a complete rebuild of underwriting methodology, and the question changed.
It is no longer “Do you have controls?” It is “Can you prove they were enforced at the time of the incident?” These are not the same question, and the gap between them is where legacy applications create uninsured exposure.
S&P Global Ratings projects annual cyber insurance premiums will grow at 15–20% through 2026 [1], driven in part by a 126% increase in ransomware incidents in Q1 2025. Carriers are tightening underwriting standards to recover margins, and legacy applications are explicitly in scope.
The case that defines the proof standard is Travelers v. ICS (2022) [2]. International Control Services attested that MFA was enforced across all administrative access. After a ransomware attack, forensic investigators found a single server without MFA enabled, one overlooked login path in a large estate.
Travelers denied the entire claim. Millions in recovery costs fell to ICS without coverage, not because their controls were broadly absent, but because one unprotected entry point contradicted the attestation.
Running end-of-life software without a documented remediation plan carries the same risk: it does not create a coverage gap but voids the basis for the claim at the time of the incident.
The claim data confirms the pattern at scale. According to Coalition’s 2024 Cyber Claims Report [3], 82% of denied claims involved missing or incomplete MFA implementation. According to analysis attributed to Deloitte, 21% of cyber insurance claims were denied or partially denied in 2025, up from 15% in 2023, with 34% of those denials attributed to failure to maintain attested controls.
What Are the Cyber Insurance Requirements for 2026?
Carriers in 2026 require documented proof across eight control categories. Legacy applications structurally fail at least five of them.
- MFA enforcement with authentication logs per account and system: Legacy applications cannot natively produce application-layer MFA event records; gateway proxy logs do not satisfy a forensic examiner reviewing the full authentication chain
- Patch event logs mapped to CISA KEV publication dates within a 14-day SLA: Applications that cannot be patched produce no patch event log; the SLA is permanently unmet
- EDR deployment report with endpoint coverage percentages: Legacy applications on EOL operating systems may fall outside EDR visibility at the application layer
- Software inventory or SBOM-equivalent with component versions and patch status: Legacy codebases with undocumented dependencies cannot verify patch posture is complete
- Structured audit logs compatible with SIEM ingestion: Proprietary flat-file formats are not ingestible and leave no forensic audit trail
- Incident response plan with tabletop results dated within 12 months: Legacy applications with undocumented business logic make recovery simulation unreliable
- Network segmentation evidence: Tightly coupled architectures structurally resist the segmentation carriers now require
- Immutable or air-gapped backup verification: Legacy data formats and proprietary schemas complicate modern backup compatibility
How Legacy Systems Affect Cyber Insurance: The Three Application-Layer Problems Security Overlays Cannot Fix
Every article ranking on this topic addresses infrastructure controls: deploy MFA, maintain EDR, segment networks, and keep patches current. That advice stops at the perimeter.
It does not address what happens when the application behind those controls cannot be patched, cannot natively authenticate, and cannot produce a log trail that a SIEM can read. Security overlays do not change what the application is.
Problem 1: Unpatchability – When the Codebase Is the Vulnerability
Legacy applications built on VB6, Classic ASP, Web Forms, Java EE, EJB, and Struts cannot receive security patches through conventional means. The codebase itself is the patch target, as no vendor is releasing a security update, no dependency to upgrade, and no configuration change that closes a CVE in the application logic.
EDR monitors behavioral anomalies around these applications. It cannot remediate a vulnerability inside them.
The CISA Known Exploited Vulnerabilities (KEV) catalog documents the operational consequences [4]. In 2025 alone, 245 new vulnerabilities were added, bringing the total to 1,484 confirmed exploited vulnerabilities.
The composition matters:
- CVE-2007-0671, an 18-year-old Excel RCE.
- CVE-2014-6278, Shellshock.
- CVE-2015-7755, Juniper ScreenOS.
- CVE-2017-1000353, Jenkins.
These are decade-old CVEs being actively weaponized today, with 24 of the 2025 KEV additions tied directly to ransomware group exploitation.
The insurance consequence is contractual. Multiple carriers now align patch SLA requirements to CISA KEV timelines: 14 days for actively exploited CVEs, 30 days for critical patches.
An application that structurally cannot be patched will never satisfy this in any timeframe. Breaches exploiting a KEV-listed vulnerability within the remediation window are explicitly excluded from coverage in an increasing number of policies.
Problem 2: MFA Incompatibility – An Architectural Condition, Not a Configuration Gap
Legacy applications were built before SAML, OAuth2, and OIDC existed. They cannot natively support modern MFA protocols without code modification or an external proxy.
The common response is an identity proxy or ZTNA gateway layered in front of the application. This works until a forensic examiner looks at the full authentication chain after a breach. If the underlying service port remains reachable, or if a legacy integration path exists that bypasses the gateway, the application reverts to unprotected access.
According to Marsh McLennan’s 2025 Cyber Insurance Market Report [5], 99% of cyber insurance applications now include specific MFA implementation questions, and the question has shifted from “do you have MFA?” to “how is it implemented and on which systems?”
A proxy that leaves the application’s service port accessible does not satisfy that question. At portfolio scale (50, 100, 200 legacy applications), no proxy configuration resolves this structurally.
Problem 3: Auditability Gaps – Applications That Cannot Produce Carrier-Acceptable Evidence
Underwriters now require continuous log evidence as the documentation baseline: patch event logs demonstrating CVE remediation timelines, authentication logs showing MFA enforcement per account and system, EDR telemetry showing endpoint coverage percentages, and IR plans with tabletop results dated within the prior 12 months.
Legacy applications frequently produce logs in proprietary flat-file formats SIEM platforms cannot ingest. Some produce no structured audit trail at all.
An application that cannot generate carrier-acceptable evidence fails the proof standard regardless of how well the surrounding controls function. And the gap is invisible until the underwriter asks for the documentation, or a forensic team looks for the log trail after a breach.
According to research attributed to Corvus Insurance, 73% of insurers now conduct external attack surface scans during underwriting. Stated posture and actual technical posture are no longer separable.
The Three Application-Layer Conditions and Their Insurance Consequences
| Condition | What Security Overlays Do | Insurance Consequence |
| Unpatchability | EDR monitors behavior around the application; cannot close a CVE inside the codebase | Breach exploiting a KEV-listed CVE within the carrier’s patch SLA window is explicitly excluded from coverage |
| MFA Incompatibility | Identity proxy enforces MFA at the gateway; underlying service port may remain accessible | Forensic investigation examines the full authentication chain — a proxy bypass or legacy path that reverts to unprotected access contradicts the attestation |
| Auditability Gaps | SIEM aggregates logs from sources that produce them; cannot ingest proprietary flat-file formats | Application fails the carrier’s proof standard even if all surrounding controls are functioning — no log evidence means no coverage defense |
End-of-Life Software and Cyber Insurance Exclusions: The October 2026 Deadline That Closes the Compensating Controls Window
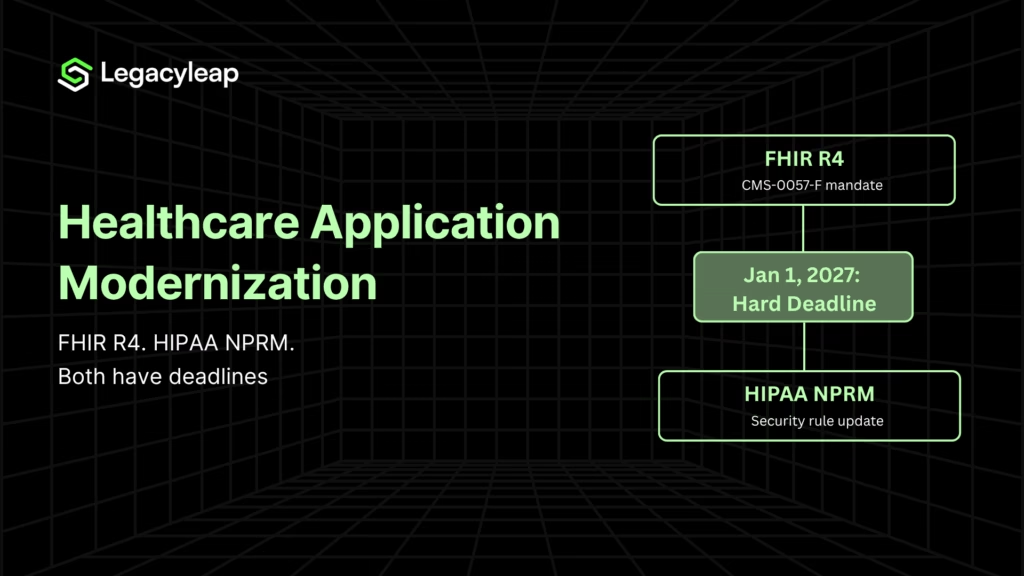
On October 13, 2026, Microsoft ends Extended Security Update support for Windows Server 2012 and Windows Server 2012 R2 [6]. This is ESU Year 3, the final paid extension Microsoft offers.
After this date, no patches will be issued for this platform under any arrangement. Any CVE discovered after October 13, 2026, will remain permanently unpatched on Windows Server 2012. This is a permanent condition.
The significance is the application-OS dependency lock. A substantial portion of enterprise legacy applications running on VB6, Web Forms, Classic ASP, and certain Java configurations were built for, and remain dependent on, Windows Server 2012 infrastructure.
Upgrading the OS breaks the application. Applying aggressive security hardening can break the application.
Three options remain:
- Run EOL indefinitely and accept the insurance consequences,
- Apply controls and risk disrupting mission-critical workflows, or
- Modernize the application off the platform entirely.
How Long Compensating Controls Work and When They Stop
A documented compensating controls narrative, such as ZTNA wrapper, MFA proxy, network segmentation, active monitoring, written remediation plan, can sustain a renewal conversation for one, possibly two cycles. Carriers accept a remediation roadmap as evidence of intent. That tolerance has a ceiling.
Compensating controls stop working when:
- The same controls appear in a second renewal, with no measurable progress on the underlying application
- The ESU deadline passes, and the platform accumulates CVEs that will never be patched, making the remediation plan structurally impossible to execute
- A breach occurs, and forensic investigation establishes the application was running on a known, unpatched, EOL platform, at which point the compensating controls narrative becomes evidence of known, unmitigated risk
According to research attributed to VulnCheck, 29% of known exploited vulnerabilities in 2025 were weaponized on or before the day their CVE was published. For applications that cannot be patched, the window between disclosure and exploitation is not a risk to manage but a permanent exposure.
EOL Platform Summary: Cyber Insurance Implications
| Platform | EOL / ESU Expiry | Patch Availability After Date | Insurance Consequence |
| Windows Server 2012 / 2012 R2 (ESU Year 3) | October 13, 2026 | None — permanent | Premium surcharge, ransomware exclusions, or carrier declination without a migration plan |
| VB6 / Classic ASP runtime | No active support | None | Carrier patch SLA requirements structurally unmet; compound KEV exposure post-Oct 2026 |
| Java EE / EJB / Struts (unsupported versions) | Varies — many versions EOL | Partial or none | Recurring CVEs with no remediation path; direct conflict with carrier KEV SLA requirements |
If any of the three failure modes in this article describe applications in your portfolio, the dependency map and CVE inventory produced by a $0 Modernization Assessment is the document your broker needs before your next renewal conversation. It produces a concrete output: module inventory, risk indicators, KEV exposure mapping, and the modernization blueprint that forms the foundation of any credible carrier disclosure. No discovery call required to receive it.
Cyber Insurance Questionnaire 2026: What the Proof Packet Requires and Where Legacy Applications Cannot Produce It
The carrier questionnaire has become a technical audit. Each question now has a follow-up: not just “do you have MFA?” but “on which systems, implemented how, and can you show us the authentication logs?”
Legacy applications fail this standard because they cannot generate the evidence the question requires.
A carrier’s documentation baseline in 2026 typically includes:
- MFA enforcement evidence: authentication logs showing MFA active per account and system, with coverage percentages. A gateway-level proxy log does not substitute for application-layer enforcement evidence when a forensic examiner examines the full authentication chain.
- Patch event logs: timestamped CVE remediation records mapped to CISA KEV publication dates. An application that cannot be patched produces no patch event log as there are no patch events.
- EDR deployment reports: endpoint coverage percentages with gap analysis. An application on an EOL OS may fall outside EDR visibility at the application layer.
- Incident response plan with tabletop results: dated within the prior 12 months. Legacy applications with undocumented business logic make precise tabletop exercises difficult. Recovery cannot be confidently simulated for a system whose dependencies are unknown.
- Software inventory / SBOM-equivalent: documentation of software components, versions, and patch status. According to research attributed to HeroDevs, 46% of CISA’s Known Exploited Vulnerabilities catalog is linked to end-of-service software. An undocumented legacy codebase may be carrying KEV-listed exposures its owners cannot account for.
Cyber Insurance Proof Packet: Legacy Application Failure Modes
| Carrier Requirement | What a Modern Application Produces | What a Legacy Application Produces |
| MFA enforcement evidence | Authentication logs with MFA event records per account; coverage report from identity provider | Gateway-level MFA log only; no native application authentication record; service port accessibility unverified |
| Patch event logs vs. KEV timelines | Timestamped patch records tied to CVE publication dates; 14-day KEV SLA demonstrable | No patch event log. Carrier SLA permanently unmet. Post-Oct 2026, new CVEs accumulate with no remediation path |
| Software inventory / SBOM | Dependency manifest with component versions, patch status, known CVE mapping | No dependency documentation; carrier cannot verify patch posture is complete |
| Structured audit logs (SIEM-compatible) | Structured log output forwarded to SIEM; events captured in queryable format | Proprietary flat-file or local disk logging; SIEM cannot ingest; audit trail unavailable for forensic review |
How Legacy Application Modernization Reduces Cyber Insurance Risk and What Underwriters Reward
The market offers two partial responses.
- Security vendors provide MFA proxies, ZTNA wrappers, EDR, and SIEM tooling. Each addresses the perimeter.
- Brokers prepare proof packets and disclosure narratives. These address the evidence requirements, not the structural conditions that make the evidence impossible to produce natively.
Neither resolves unpatchability, native MFA incompatibility, or the absence of structured audit logs.
Legacyleap operates at the application layer inside the application, not around it.
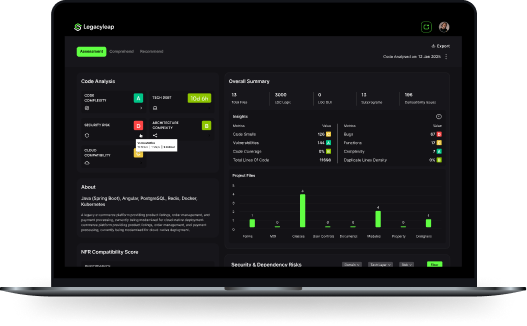
The Assessment Agent: Producing the Software Inventory Carriers Are Now Requiring
The first question a carrier questionnaire asks about a legacy application is what is in it and what is its patch posture. If the answer requires a developer to manually trace undocumented dependencies, the patch posture assessment is incomplete by definition.
The Assessment Agent produces a dependency graph with module boundaries, third-party component versions, integration points, and CVE mapping against identified components. The output is the SBOM-equivalent that carrier questionnaires now explicitly require, produced for a codebase that has never had one.
This is how an organization arrives at the software inventory a carrier’s technical auditor wants to see, rather than a disclosure narrative that assumes completeness without demonstrating it.
The Modernization Agent: The Auditable Transformation That Satisfies the Proof Standard
The Modernization Agent resolves all three structural conditions underwriters measure. The modernized application can be patched on CISA KEV timelines.
It natively enforces modern authentication through SAML, OAuth2, or OIDC, producing application-layer MFA event records rather than gateway-level proxy logs. It generates structured audit output that SIEM platforms ingest directly.
Every transformation is human-reviewed before acceptance and traceable to a specific module and decision. This is what distinguishes a governed modernization from an undocumented rewrite, and it is the posture a carrier’s proof standard rewards.
The QA Agent validates behavior parity through automated regression testing, producing evidence that the transformation was controlled and did not introduce new risk. The result is an application that satisfies all three underwriting conditions natively, without proxies, overlays, or compensating control narratives.
The Timing Argument and Premium Leverage
The October 2026 deadline is fixed. It has not yet closed. AI-assisted modernization compresses delivery timelines substantially.
Projects that historically required 18 months or more have been completed in significantly shorter windows with structured automation. Organizations that begin in the current quarter have a realistic path to completing a meaningful scope before the ESU expiry closes the compensating controls narrative.
The financial case extends beyond avoiding denial. A phased modernization program generates documented, quarterly progress. Each modernized application is a verifiable reduction in portfolio-level exposure.
Practitioners in technical communities have reported premium discounts for demonstrating year-over-year security improvement. Insurance cost reduction is a Horizon 1 ROI, measurable at the next renewal cycle, before any longer-horizon engineering benefit materializes.
For a fuller treatment, see our application modernization ROI: three-horizon framework and incremental modernization.
Does Modernizing Legacy Systems Lower Cyber Insurance Premiums? Conclusion and Next Steps
Compensating controls address the perimeter. Modernization addresses the application.
Underwriters in 2026 are measuring the application for its patch posture, its authentication architecture, its audit log output, and its platform lifecycle status. October 2026 closes the compensating controls window.
The renewal conversation has already made the modernization decision. Now, it is whether to begin before the deadline that produces the conditions it is warning against.
A $0 Modernization Assessment produces the dependency map, module inventory, risk indicators, and modernization blueprint that form the foundation of any credible carrier disclosure or renewal narrative, whether the organization is ready to act now or building the internal business case for the next budget cycle.
Book a $0 Modernization Assessment.
For organizations that want to see how the platform maps and modernizes the specific applications their renewal flagged:
FAQs
There is no published rate card separating legacy from modern infrastructure directly, but the pricing signals are visible at renewal. Enterprises disclosing EOL platforms, undocumented patch postures, or MFA gaps face premium surcharges, ransomware-specific exclusions, or sublimit reductions. S&P Global projects a 15–20% market-wide premium growth rate for 2026 [6]. For portfolios with concentrated legacy exposure, the effective increase, once surcharges and exclusions are factored in, can materially exceed that baseline.
Carriers accept a documented controls narrative, such as ZTNA wrapper, MFA proxy, network segmentation, EDR coverage, written remediation roadmap, for one, sometimes two renewal cycles, provided the roadmap shows measurable progress between renewals. After October 13, 2026, a remediation roadmap for applications dependent on Windows Server 2012 becomes structurally unexecutable. Compensating controls are a bridge strategy. The bridge ends in October 2026.
A Software Bill of Materials is a structured inventory of an application’s components, libraries, and dependencies, with version and vulnerability status. Underwriters require it because patch posture attestation is only credible if the organization knows what it is patching. According to research attributed to HeroDevs, 46% of CISA’s Known Exploited Vulnerabilities catalog is linked to end-of-service software, and an undocumented codebase cannot account for what it is carrying.
A denial occurs post-breach when the carrier determines the claim does not meet coverage conditions, typically because attested controls were not enforced. An exclusion removes a category of risk from coverage before any claim is filed. For legacy software incidents, both apply: exclusions may cover breaches exploiting known, unpatched vulnerabilities; denials follow when forensic review finds attested controls were not actually in place. Travelers v. ICS is a denial, attestation contradicted by evidence.
After October 13, 2026, Windows Server 2012 receives no further patches. Every CVE published after that date accumulates permanently with no remediation path. Carriers renewing accounts with applications on this platform face a straightforward calculation: unpatched CVEs will compound indefinitely. Likely responses include premium surcharges, ransomware exclusions tied to the EOL platform, sublimit reductions, or declination. A documented, progressing modernization program is the primary mechanism for negotiating terms.
Timeline depends on application complexity and scope. AI-assisted modernization with structured agent automation has compressed projects that historically required 18 months into substantially shorter windows. For renewal purposes, full completion is not the threshold. Demonstrable, documented progress is. A dependency map, SBOM-equivalent, and one or two QA-validated modules changes the carrier conversation from unmitigated risk to a measurable, progressing remediation. Starting before October 2026 is what creates that evidence trail.
References
[1] S&P Global Ratings, Cyber Insurance Market Outlook 2026 —https://www.spglobal.com/ratings/en/regulatory/article/cyber-insurance-market-outlook-2026-resilient-earnings-tougher-competition-pockets-of-growth-s101658506
[2] Travelers v. International Control Services (2022) — documented across legal and industry sources including Insurance Journal and Coveware incident reporting.
[3] Coalition 2024 Cyber Claims Report —https://www.coalitioninc.com/reports/cyber-claims-report-2024
[4] CISA Known Exploited Vulnerabilities Catalog —https://www.cisa.gov/known-exploited-vulnerabilities-catalog
[5] Marsh McLennan 2025 Cyber Insurance Market Report —https://www.marshmclennan.com/insights/publications/2025/cyber-insurance-market-report.html
[6] Microsoft Lifecycle Documentation, Windows Server 2012 / 2012 R2 —https://learn.microsoft.com/en-us/lifecycle/products/windows-server-2012