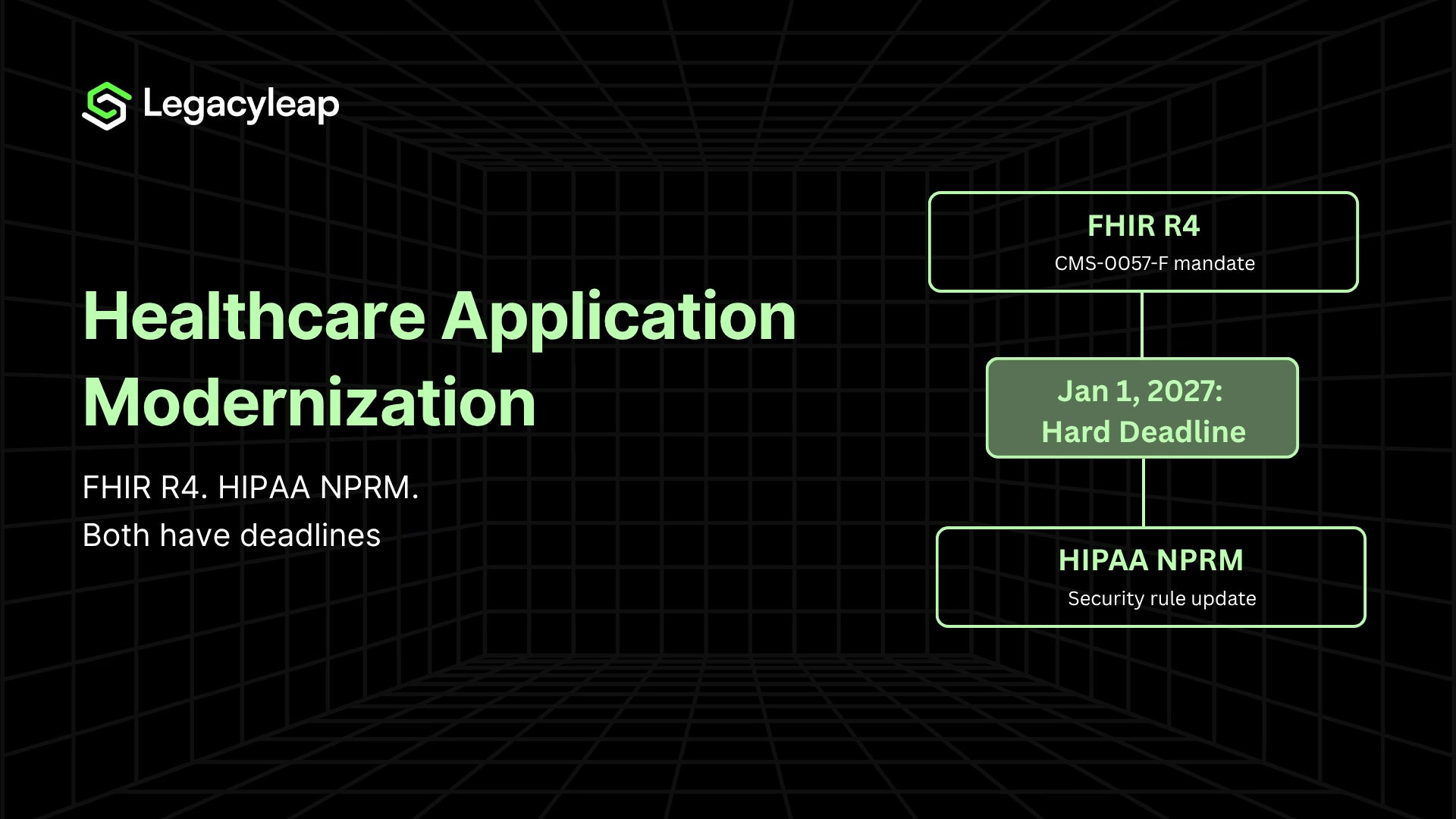
Healthcare Application Modernization: What’s Forcing the Decision Now
If your clinical software runs on Struts, JSP, or Java EE, two compliance deadlines are now architectural requirements.
The January 1, 2027, FHIR R4 mandate requires system capabilities your legacy stack cannot meet without structural change. The 2026 HIPAA Security Rule NPRM removes encryption’s addressable status entirely. And the average PHI breach now costs $10.93M [1].
Healthcare application modernization is no longer a budget-cycle conversation. It is a program with a hard end date.
This article is written for healthcare ISVs that build and sell clinical software, not hospital IT departments managing internal infrastructure. The constraints are structurally different: ISV teams carry product-level HIPAA liability, 24/7 customer SLA obligations, and the requirement to ship features while executing a modernization program in parallel.
Most content in this space addresses hospital IT. This does not.
What follows covers the full cost of inaction, the specific architectural requirements each deadline imposes, the approach comparison ISV decision-makers need, and the execution model that gives these programs a viable path to completion.
What Are Legacy Clinical Systems?
Legacy clinical systems are healthcare software applications built on technology stacks that predate modern security, interoperability, and cloud standards, and cannot be updated to meet current requirements without architectural change.
For healthcare ISVs, these typically include:
- EHR platforms, hospital information systems, and laboratory information systems
- Billing and claims processing engines
- Prior authorization workflows
- Any application built on Struts 1.x/2.x, JSP, Java EE, or HL7 v2 interfaces
For an ISV carrying product-level HIPAA accountability, these stacks create compounding risk. Every year they run without modernization, the security gap widens, the compliance exposure grows, and the cost of eventual transformation increases.
What Are the Risks of Not Upgrading Legacy Healthcare Software?
For healthcare ISVs, the risks of running legacy clinical software are not theoretical. They are active cost lines accumulating simultaneously across security, compliance, and operational categories.
Deferring modernization does not hold these costs steady. It increases them.
- PHI breach exposure. The average PHI breach costs $10.93M [1], the highest of any industry. Legacy Struts and JSP applications typically lack TLS 1.3 and AES-256 encryption, gaps that IBM X-Force 2024 explicitly identifies as ransomware entry points [2]. For an ISV whose customers depend on the system for clinical operations, a breach creates customer loss and product-level reputational damage alongside the financial liability.
- HIPAA non-compliance penalties. HIPAA civil monetary penalties run up to $1.9M per violation category per year. Once the HIPAA Security Rule NPRM requirements take effect, legacy ISV systems that cannot meet mandatory encryption or MFA requirements carry explicit audit exposure. For ISVs carrying Business Associate Agreement obligations with their customers, that exposure is bilateral.
- HL7 bridge maintenance overhead. ISV teams running 50-200+ active HL7 v2 interfaces spend an estimated $100K-$200K annually in developer time maintaining bridges that cannot be updated to expose FHIR APIs. This cost scales with interface count and grows as customer demand for FHIR-based integrations accelerates. Every month of deferral extends a maintenance line that the January 2027 deadline will force into a rebuild regardless. For more on tightly coupled clinical systems and what untangling them requires, see our technical breakdown.
- Talent cost and knowledge concentration risk. Based on Legacyleap’s primary talent market data, hiring Java EE and Struts specialists takes over 120 days, at a 40% premium above comparable modern stack rates. The larger risk is concentration: in most ISV environments, full functional understanding of the system sits with one or two engineers. When they leave, the cost of reconstructing that comprehension increases by an order of magnitude, because system documentation has not kept pace with system behavior.
- Compressed product velocity and competitive exposure. An ISV on a legacy clinical platform runs two competing budget lines simultaneously: maintaining the legacy system and building the features customers expect. When maintenance consumes the majority of engineering capacity, feature delivery slows. Customers on modern competitor platforms get functionality that the ISV’s roadmap cannot match on the same timeline. This is a market position problem, not just a budget math problem. For a fuller analysis of how compounding technical debt in legacy clinical applications erodes product velocity, see our cost model.
What Are the 2026 HIPAA Security Rule Changes?
The HIPAA Security Rule NPRM, published in December 2024, proposes the most significant changes to the Security Rule since its original publication. For healthcare ISVs on legacy stacks, these are not incremental compliance adjustments. They are architectural requirements.
Four Requirements That Directly Affect Legacy Clinical Systems
| Requirement | What Changes | Legacy System Impact |
| Mandatory encryption | Encryption moves from “addressable” to mandatory across all PHI storage and transmission [4] | Struts/JSP applications lacking TLS 1.3 or AES-256 require architectural change, not a policy update |
| Mandatory MFA | Required across all access paths to PHI | Legacy single-factor access control cannot meet this through configuration alone |
| 72-hour incident reporting | Breach notification timelines tighten materially | ISV teams need detection and reporting infrastructure to meet this SLA |
| 15-day vulnerability remediation | Known CVEs must be remediated within 15 days | Struts 1.x (EOL since 2013) has no active patch support — this requirement is architecturally unachievable without migration |
The Hidden Cost of Running Legacy and Modern Systems in Parallel
During a phased migration, both systems are live simultaneously. That means two separate HIPAA compliance postures for the full duration of the program.
In practice, this translates to:
- Two audit trail configurations
- Two access control layers
- Two encryption compliance postures
- Two sets of Business Associate Agreement obligations
If a phased program runs 12-18 months, this dual-compliance overhead runs for 12-18 months, with full governance, documentation, and audit readiness requirements applying to both environments throughout.
ISV teams that plan migrations around feature parity milestones without budgeting this as a distinct cost line consistently hit it as an unbudgeted surprise at governance review.
What Does the January 2027 FHIR R4 Mandate Require?
Under CMS-0057-F, healthcare applications must expose FHIR R4 APIs for three specific workflows by January 1, 2027 [3]:
- Prior authorization processing
- Payer-to-payer data exchange
- Provider access
The mandate carries performance requirements alongside the API requirements. Urgent prior authorization requests must be resolved within 72 hours. Standard requests within 7 calendar days. System response time is now a compliance requirement, not an operational target.
For healthcare ISVs on HL7 v2-only interfaces, this is a hard compliance cliff. There is no configuration path from HL7 v2 to FHIR R4, only a rebuild path.
On the FHIR wrapper approach:
Wrapping an HL7 v2 interface with a FHIR API layer is faster than a full architectural rebuild and viable as a near-term bridge. But it should be chosen deliberately. The legacy security gaps underneath the wrapper remain.
The maintenance surface expands as the ISV now maintains both the wrapper and the HL7 layer it sits on. Every month the wrapper defers the rebuild, the audit exposure from the unpatched legacy system continues to accumulate. The wrapper buys time. It does not buy compliance.
On HTI-5 certification reform:
Approximately 70% of ONC certification criteria are changing, reoriented around FHIR-based APIs. For ISVs whose products require ONC certification, this is a product-level compliance requirement, independent of their customers’ infrastructure.
An ISV that meets the January 2027 data exchange deadline but misses HTI-5 product certification faces a second compliance gap on a separate timeline.
Rehosting, Refactoring, or Rearchitecting: Which Approach Fits Clinical Systems?
Each approach carries distinct compliance, timeline, and clinical risk trade-offs. The table is organized so the recommended path is visible without reading every row.
| Approach | What It Does | Healthcare-Specific Trade-off | Suitability |
| Rehosting (Lift and Shift) | Moves the application to new infrastructure without changing code | Relocates HL7 brittleness and legacy encryption gaps intact. No path to FHIR R4. Moves the HIPAA audit exposure to a new address. | Not recommended for clinical applications with compliance obligations |
| API Encapsulation | Wraps legacy endpoints in a modern API layer | Viable near-term FHIR bridge. Does not resolve underlying security debt. Expands maintenance surface without removing the one underneath. | Acceptable as a time-bounded bridge; not a durable solution |
| Refactoring (In-Place) | Restructures code without changing external behavior | Significant risk when clinical rules and billing logic live in undocumented JSP/Struts code. Divergence may be latent for months before surfacing in an audit or billing discrepancy. | Viable only when preceded by full system comprehension |
| Rearchitecting | Redesigns system architecture while preserving core logic | High governance overhead. Requires complete behavioral documentation before execution. Scope management is critical in 24/7 clinical environments. | Appropriate for ISVs targeting FHIR-native architecture; requires disciplined phasing |
| Phased Modernization (Strangler Fig) | Incrementally replaces modules while legacy system runs in parallel | Manageable compliance posture when dual-system governance is planned explicitly. Allows parity validation per module before cutover. Recommended for most healthcare ISVs. | The right default for clinical systems on 24/7 SLAs |
Rearchitecting and phased modernization are not alternatives. For most ISVs, phased modernization is the execution model and rearchitecting is what happens module by module within it.
Why Lift-and-Shift Is the Wrong Choice for Clinical Applications
Lift-and-shift moves fast and carries low perceived execution risk. For clinical applications, that perception is wrong.
Moving a Struts application with HL7 v2 interfaces to a cloud environment does not change the encryption architecture. Instead, it relocates the HIPAA audit exposure. It creates no path to FHIR R4 compliance. The CVE exposure from EOL frameworks travels with it.
The debt is not resolved. It is relocated.
Why Refactoring Without Prior Comprehension Is Dangerous in Healthcare
In a financial system, behavioral divergence surfaces quickly through reconciliation failures. In a clinical system, divergence can be latent for months. Clinical rules, billing logic, and care protocol triggers encoded in 15-year-old Struts action classes exist as behavior, not documentation.
When that behavior changes silently in a refactored system, the divergence may not surface until an audit, a billing discrepancy, or a patient safety edge case.
If you are not certain your current HL7 interface architecture can meet the January 2027 FHIR R4 requirement, the $0 Modernization Assessment maps exactly that. It starts with your full HL7 interface inventory, so your compliance timeline is based on what is actually in your system, not what the documentation says.
Why Phased Modernization Is the Right Default for Healthcare ISVs
Four conditions make phased modernization work for clinical ISV teams. These are not aspirational guidelines but preconditions for the program to succeed:
- Full dependency mapping completed before the first module enters transformation
- HL7 interface inventory produced before approach selection, not during execution
- Per-module parity validation criteria defined in advance, not derived post-hoc
- Dual compliance posture modeled as a budget line item, not discovered at governance review
For a detailed breakdown of how to structure an incremental modernization strategy for enterprise legacy systems, see our execution guide.
Timeline and Cost Benchmarks for Healthcare ISV Programs
| Approach | Typical Timeline | What It Resolves |
| Rehosting | 3-6 months | Nothing architecturally — compliance cliff remains |
| Full rearchitecture (unphased) | 18-24 months | Everything, but clinical risk is high without modular isolation |
| Structured phased modernization | First module live in 90 days; full cutover in 12-18 months | Right default for ISVs on 24/7 SLAs |
On cost: for a mid-market clinical ISV with 50-200 HL7 interfaces, a phased modernization program typically ranges from $500K to $2M, depending on interface count, stack complexity, and whether on-prem LLM deployment is required for PHI isolation.
These are directional ranges. Stack-specific assessment is the only reliable basis for a program budget.
What is not directional: the HL7 revalidation workstream runs $100K-$200K annually when deferred, the 40% Java EE talent premium compounds every hiring cycle, and breach exposure runs at $10.93M per incident.
HL7 Interface Revalidation: The Workstream Most Programs Don’t Budget For
Every HL7 interface connected to the modernized application must be retested. Many must be rebuilt.
For a healthcare ISV with 50-200+ active connections, this is not a QA task appended to the core program. It is a separate revalidation workstream with its own timeline and resource requirements.
Interface count drives program cost more than almost any other variable, and it is almost never modeled accurately in the initial budget because the inventory was never produced before planning began.
The Three Clinical Parity Dimensions That Standard QA Misses
Standard QA tests whether the new system works. For clinical systems, that is not sufficient. Three parity dimensions require explicit validation as acceptance criteria for each transformation cycle:
- Clinical output parity: The modernized system must produce identical clinical decisions, billing triggers, and care protocol outputs under identical inputs.
- Regulatory audit behavior parity: Audit trail generation, access logging, and PHI handling must meet HIPAA requirements in the modernized system exactly as they did in the legacy system. Gaps cannot be introduced silently.
- Integration continuity: HL7 interface behavior, message formatting, and downstream system interactions must be validated as unchanged after each transformation cycle.
The Canonical ISV Failure Pattern
An EHR vendor portfolio modernization documented by HealthAsyst attempted backend integration and a single sign-on UI layer without first achieving full system comprehension.
The program neither reduced maintenance cost nor achieved customer migration to a single platform, and ultimately required full re-engineering at significantly higher cost [5]. Scope expanded beyond what the comprehension baseline could support, and insufficient testing allowed behavioral divergence to accumulate undetected.
A separate case documented by vFunction describes a Fortune 500 firm whose entire Java EE modernization program stalled because an Apache Struts 1 dependency (end-of-life since 2013) was not mapped before execution began [6]. The dependency was not in the documentation. It was in the system.
These are not outliers. They are the predictable consequence of beginning transformation before comprehension is complete.
The right modernization approach depends on your specific stack, interface count, and compliance timeline. The $0 Modernization Assessment produces a stack-specific recommendation with effort and timeline ranges, before any program commitment is made.
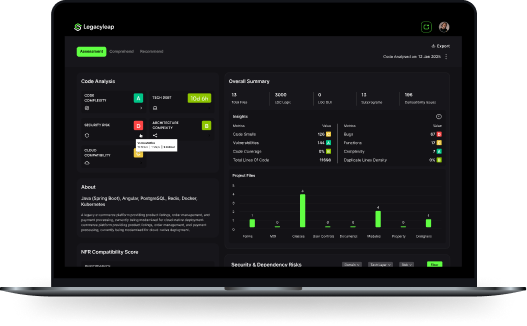
How AI-Powered Code Comprehension Reduces Healthcare Modernization Risk
In a 15-year-old clinical system, the clinical rules, billing logic, and care protocol triggers are not in the documentation. They are in the behavior of the code.
Manual documentation efforts miss them because the system has diverged from its documentation over years of undocumented patches and hotfixes. That gap is the mechanism by which most healthcare modernization programs create compliance exposure they did not anticipate.
AI-powered code analysis resolves this differently. Rather than working from documentation, it analyzes the actual codebase, reconstructing what the system does, including undocumented behavior, before a single line of code is changed.
The methodology is comprehension-first modernization: assess and document the full system behavior before any transformation decision is made.
For a healthcare ISV carrying HIPAA accountability, this matters in two specific ways:
- Audit defensibility. Every transformation in a comprehension-first program produces a reviewable, reversible, attributable diff. The ability to demonstrate that no undocumented clinical logic was altered during modernization is an audit asset, not just a technical guarantee.
- PHI-in-codebase compliance. Clinical codebases frequently contain embedded PHI in test fixtures or production-derived test data. Public cloud AI tools cannot be used for modernization analysis in these environments without triggering PHI exposure. On-prem LLM deployment is not a premium feature for security-conscious buyers. For some programs, it is a hard architectural requirement with no substitute.
How Legacyleap Governs the Full Modernization Lifecycle
A leading healthtech company modernized 300+ JSP screens and 5,000+ Struts forms to Angular using Legacyleap, Gen AI, and AWS services, in a production 24/7 clinical environment.
The outcome: a scalable Angular-based UI, reduced downtime, improved performance, and simplified maintenance, without disruption to clinical operations.
This is the stack healthcare ISVs are running today. Not a framework. A completed program.
Legacyleap’s five-agent platform addresses the failure modes this article has documented. Each capability maps to a named risk:
| Capability | Failure Mode It Addresses | Healthcare-Specific Relevance |
| Assessment Agent | Approach selected without full system visibility | HL7 interface inventory required before scope commitment |
| Documentation Agent | Undocumented clinical logic lost in refactoring | Clinical rules, billing logic, care protocols encoded in JSP/Struts |
| Modernization Agent (diff-based review) | Untraceable AI-driven changes in regulated systems | Audit trail requirement under HIPAA NPRM |
| QA Agent | Behavior divergence undetected until audit or incident | Clinical output parity, HIPAA audit behavior, HL7 continuity |
| On-prem / VPC deployment | PHI exposure through cloud AI tooling | Clinical codebases with embedded PHI in test environments |
- The Assessment Agent maps the full application before any transformation decision: JSP and Struts classes, Java EE dependencies, HL7 interface inventory, and downstream system connections.
- The Documentation Agent reconstructs clinical rules and billing logic from actual system behavior, not documentation, before a single line is changed. The Modernization Agent executes all transformations diff-by-diff, with human approval required before any diff is applied.
- The QA Agent validates each transformed module against the three clinical parity dimensions before the next cycle begins.
Legacyleap’s effort reduction across the modernization lifecycle is 40-50%, based on the platform’s production healthcare case.
On-Prem and VPC Deployment
Where PHI exists in codebase or test environments (which it frequently does in clinical systems), public cloud AI tools cannot be used for modernization analysis without triggering PHI exposure.
Legacyleap supports on-prem LLM deployment and VPC-isolated execution. For some healthcare programs, this is a hard architectural requirement, and it is not available in generic AI-assisted development tooling.
Healthcare Data Migration Best Practices for HIPAA Compliance
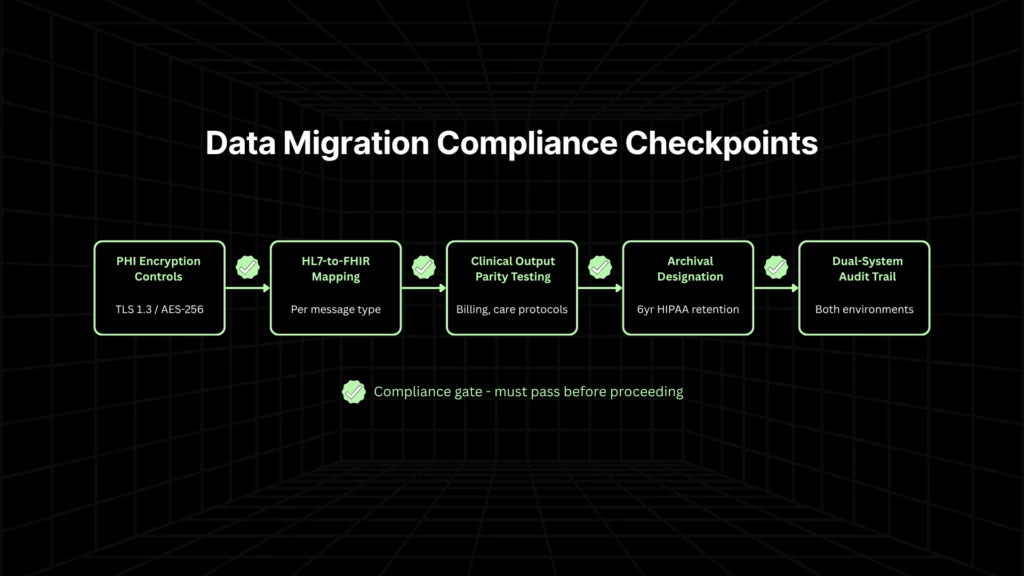
Healthcare data migration is not a standard data transfer project. PHI handling requirements, HIPAA retention obligations, and the need for audit trail continuity across both systems during a phased migration create compliance obligations that apply from the first byte moved to the last record archived.
- PHI handling during migration. PHI in transit must meet the same mandatory encryption standards as PHI at rest. Every transfer must be logged and attributable. ISV teams moving patient records, clinical histories, and billing data between systems need encryption controls applied at the migration pipeline level, not just at the destination.
- HL7-to-FHIR data standardization. The mapping burden between HL7 v2 and FHIR R4 is not automatic. HL7 message structures do not translate cleanly into FHIR resources because the mapping requires explicit specification, validation, and testing for each message type. For ISVs with 50-200+ active HL7 interfaces, this is a distinct workstream that runs parallel to the code transformation program. Treating it as a configuration task is one of the most common causes of delayed FHIR compliance timelines.
- Validation before cutover. Clinical output parity in data migration means confirming that migrated data produces the same clinical outputs in the new system as the original data produced in the legacy system. Standard data validation, such as row counts and field checksums, is necessary but not sufficient. Test scenarios must cover the clinical edge cases specific to your domain: billing triggers, care protocol flags, and prior authorization logic.
- Archival strategy for legacy data. Healthcare ISVs cannot delete legacy data at cutover. HIPAA requires retention of medical records for a minimum of six years from the date of creation or last use, and state law requirements vary. The legacy system or a compliant archive must remain accessible for the full retention period, an ongoing hosting and access cost that most modernization programs do not model.
- Dual-system data integrity. During a phased migration, the same patient record may exist in both systems simultaneously. Maintaining audit trail continuity across both environments is a compliance requirement throughout the migration window. ISV teams should designate a system of record for each data domain during the transition and document the designation explicitly.
Modernize Before the Deadline Forces the Decision
Healthcare software modernization is a governance problem with a cost structure that compounds every year it is deferred. The breach exposure is measurable. The talent premium is documented. The compliance deadlines are on the calendar.
January 1, 2027, is not far. Healthcare ISVs on Struts, JSP, and Java EE that begin a structured assessment now have a viable path to FHIR R4 compliance and HIPAA Security Rule alignment within that window. Those that delay face both a compliance cliff and an architecture that cannot support the API-first capabilities their customers will expect in the next product cycle.
The right first step is not selecting an approach. It is understanding what you are actually dealing with.
Healthcare ISVs that start a structured assessment now have a viable path within the January 2027 window. The $0 Modernization Assessment delivers a complete dependency map, HL7 interface inventory, and modernization blueprint at no cost. Request your assessment today.
To see Legacyleap’s five-agent workflow and governed transformation model in a live healthcare modernization context, book a Demo.
FAQs
The only reliable approach is to reconstruct the full behavioral map of the legacy system before transformation begins from the codebase itself. Clinical rules, billing triggers, and care protocol logic that were never formally documented still exist as system behavior, and that behavior can be mapped through static analysis and AI-assisted code comprehension. The resulting behavioral baseline becomes the reference against which every transformation cycle is validated. Programs that skip this step and begin refactoring against documentation alone consistently lose logic that documentation never captured.
Existing Business Associate Agreements typically bind to the covered system and its data processing scope, which means a phased migration that introduces a new modernized environment may require BAA amendments or new agreements with downstream integration partners before PHI flows through the modernized system. ISV teams should audit their full BAA inventory against the planned migration scope before the first module goes live. Running two systems in parallel without confirming that BAA coverage extends to both environments creates an unaddressed compliance gap for the duration of the migration.
They are independent requirements addressing different dimensions of clinical software compliance. HIPAA governs how PHI is secured, accessed, and reported, which is a data protection framework. FHIR R4 compliance, as mandated under CMS-0057-F, governs how clinical data is exchanged via standardized APIs. it is an interoperability requirement. A system can be HIPAA-compliant and FHIR non-compliant, or expose FHIR R4 APIs while failing the HIPAA NPRM’s mandatory encryption requirements. Healthcare ISVs carrying product-level accountability need to meet both, on overlapping but distinct timelines.
The scoping input is a complete HL7 interface inventory: every active interface, the message types it carries, the downstream systems it connects to, and the testing requirements for each. Without this inventory, any budget or timeline estimate for HL7 revalidation is a guess. The inventory itself should be produced as a precondition for approach selection, not as a discovery task during execution. For ISVs with 50-200+ active interfaces, the revalidation workstream typically represents 20-30% of total program effort and should be planned as a parallel workstream with its own resourcing, not appended to the core transformation scope.
The key is treating each module cutover as an independent release with its own rollback path, rather than a continuous migration that accumulates risk. Traffic routing between legacy and modernized modules should be explicitly controlled. New patient interactions route to the modernized module only after parity validation passes; existing in-flight clinical workflows complete on the legacy system. Monitoring must cover both environments throughout the parallel-run period. ISV teams that treat the legacy system as a passive fallback rather than an active production environment during this window tend to understaff its operational coverage, which creates SLA exposure precisely when the rollback path matters most.
References
[1] IBM Security. Cost of a Data Breach Report 2024. https://www.ibm.com/reports/data-breach
[2] IBM Security. X-Force Threat Intelligence Index 2024. https://www.ibm.com/reports/threat-intelligence
[3] Centers for Medicare & Medicaid Services. CMS-0057-F — Interoperability and Prior Authorization Final Rule. https://www.cms.gov/priorities/key-initiatives/burden-reduction/interoperability/policies-and-regulations/cms-0057-f-interoperability-and-prior-authorization
[4] U.S. Department of Health and Human Services / Federal Register. HIPAA Security Rule NPRM, December 2024. https://www.federalregister.gov/documents/2024/01/12/2024-00581/hipaa-security-rule-to-strengthen-the-cybersecurity-of-electronic-protected-health-information
[5] HealthAsyst. Legacy Modernization 101, Part 2. https://www.healthasyst.com/legacy-modernization-101-part-2/
[6] vFunction. Technical Debt Stymies Java Modernization.https://vfunction.com/blog/technical-debt-stymies-java-modernization/