What Is Core Banking Modernization?
Core banking modernization is the process of replacing or upgrading a bank’s legacy back-end systems, such as deposits, loans, payments, and general ledger, with modern, cloud-native, or API-first platforms.
For mid-market banks in the $500M–$10B asset range, it is the foundational infrastructure decision that determines real-time payments capability, AI readiness, and long-term competitive position.
Why Mid-Market Banks Can No Longer Defer Core Modernization
Core banking modernization is the process of replacing or upgrading a bank’s legacy back-end systems (deposits, loans, payments, and general ledger) to modern, cloud-native or API-first platforms. For mid-market banks in the $500M–$10B asset range, three signals in 2026 have made this an immediate decision, not a planning-cycle one.
| Signal | What Is Happening |
| Big Three platform consolidation | Fiserv launched CoreAdvance in early 2026, consolidating Premier, Precision, and Cleartouch. Jack Henry has its cloud-native deposit core targeting H1 2026. FIS has Affinity Edge in motion. These three vendors serve roughly 70% of US banks by institution count. Their migration timelines are moving whether client banks are ready or not. |
| Real-time payments gap | Around 62% of US banks planned to offer real-time payments in 2026, up from 49% in 2024. Legacy batch-processing cores cannot support FedNow or RTP natively. This is now a baseline infrastructure expectation, not a competitive differentiator. |
| AI readiness dependency | Modern core architecture (event-driven, API-accessible, with clean data models) is the prerequisite infrastructure for enterprise AI deployment. A bank deferring core modernization is deferring its AI strategy along with it. |
The lock-in paradox. The ABA 2024 Core Platforms Survey found that 35% of banks are dissatisfied with their current core vendor, with satisfaction declining steadily the longer a bank stays on its current platform [1]. Only 19% say they are likely to switch at their next renewal date [1]. The gap between dissatisfaction and action is migration risk, not satisfaction. The 2026 vendor consolidation cycle is changing that calculation for banks that have not yet moved.
A core banking system covers deposits and account management, loan origination and servicing, payments processing, general ledger, and customer data management. For mid-market banks, the attached integration estate typically runs 50 to 150 active third-party connections, many partially or entirely undocumented.
The True Cost of Doing Nothing: A TCO Framework
For a $2B bank spending $4M annually on core licensing and maintenance, a rigorous TCO audit typically surfaces $8M to $16M in fully-loaded legacy cost once compliance overhead, innovation tax, security exposure, and talent scarcity premium are counted.
The scale of this problem across the industry is significant: IDC Financial Insights projects global FI spending on legacy payment systems alone will reach $57.1B by 2028, up from $36.7B in 2022 [2].
A program that looks expensive in absolute terms frequently looks defensible when measured against the true cost of inaction.
For a detailed breakdown of how hidden costs compound across a modernization program, and how to structure the financial case for your board, see our ROM estimation guide for modernization programs and three-horizon ROI framework.
| Cost Category | How It Manifests | Why It Is Underestimated |
| Compliance overhead | Manual workarounds for BSA/AML, CRA, and consumer compliance reporting | Legacy cores were not designed for modern regulatory reporting. Each audit cycle requires custom reconciliation work that modern platforms handle programmatically. |
| Innovation tax | Product launches take quarters instead of weeks | Legacy cores cannot expose clean APIs. Every new integration requires custom middleware built on top of existing technical debt. |
| Security exposure | Higher breach remediation costs relative to modern infrastructure | Legacy perimeter architecture is structurally incompatible with modern threat models. Breach costs run materially higher on legacy systems than on modern equivalents. |
| Talent scarcity premium | Rising consultant rates and longer incident resolution cycles | The developer population with deep expertise in these specific platforms is shrinking as institutional knowledge retires. The cost compounds annually. |
The TCO audit is the foundational exercise before any vendor conversation or migration decision. Without it, decision-makers anchor on the licensing cost and find reasons to defer. The audit reframes inaction as a higher-risk financial position.
Running the real numbers on legacy cost is the work most banks skip before a board conversation. The $0 Modernization Assessment produces a dependency map, effort ranges, and a modernization readiness view without committing to a program.
The Four Migration Approaches: Choosing the Right Strategy for Your Bank
| Approach | Typical Timeline | Risk Level | Best For |
| Phased / Co-existence (Dual-Core) | 3–5 years for full migration [3] | Moderate / Managed | Banks with $2B–$10B in assets and complex integration estates |
| Sidecar Core | 18–36 months for initial component | Lowest entry risk | Banks targeting FedNow/RTP or launching new products as a first use case |
| Big Bang Replacement | 3–5+ years | Highest execution risk | Institutions with simplified portfolios or hard vendor sunset deadlines |
| Augmentation / Wrapping | 6–18 months | Lowest overall risk | Short-term bridge strategy — appropriate as a stopgap, not a modernization endpoint |
How Long Does Core Banking Modernization Take?
Core banking modernization for a mid-market bank typically takes 18 to 36 months for a targeted sidecar or phased approach focused on a single domain, and 3 to 5 years for a full-platform migration (EY, 2025) [3].
Big bang replacements are rare and higher-risk. Most banks in the $500M–$10B range now favor progressive, domain-by-domain approaches that compress risk and allow course correction between phases.
Decommissioning timelines frequently extend 12 to 24 months beyond original program estimates, directly eroding the TCO benefit of modernization.
What Is a Sidecar Core Banking Strategy?
A sidecar core banking strategy involves running a modern core banking system in parallel with an existing legacy core, handling a defined subset of customers, products, or services. The legacy core continues operating for the existing book while the modern core handles new products or a pilot customer segment.
IDC projects that 40% of global banks will pursue sidecar approaches by 2026, rising to 70–80% by 2028. For mid-market banks in the $500M–$3B range, the sidecar is the lowest-risk entry point into modernization because it avoids a full cutover event, builds team competency on the modern platform before migrating the full book, and creates an exit path from legacy infrastructure without requiring a big bang replacement.
The governance risk is specific and worth naming upfront. A sidecar becomes permanent if an explicit migration path to full replacement is not defined at the outset. Banks that skip that definition end up running two cores indefinitely, compounding integration complexity rather than resolving it.
The Abstraction Layer: What Has to Be Built First
The phased co-existence model is the dominant approach for banks in the $500M–$3B range on Fiserv Premier, Jack Henry SilverLake, or FIS Horizon. It requires an abstraction layer built before migration begins, not during it. That layer has three components:
- A Core Abstraction API that routes requests between legacy and modern systems
- A Core Banking System Connect for transaction reconciliation across environments
- An ETL Data Synchronization layer for maintaining data consistency throughout the transition
The abstraction layer is not the migration. It is the infrastructure that makes migration safe. Programs that build the abstraction layer and migrate concurrently pay for that decision through extended dual-run periods and integration failures that surface post-cutover.
According to EY’s 2025 analysis, full-platform migrations consistently run 3–5 years for institutions in this asset tier, with decommissioning timelines frequently extending beyond original projections [3].
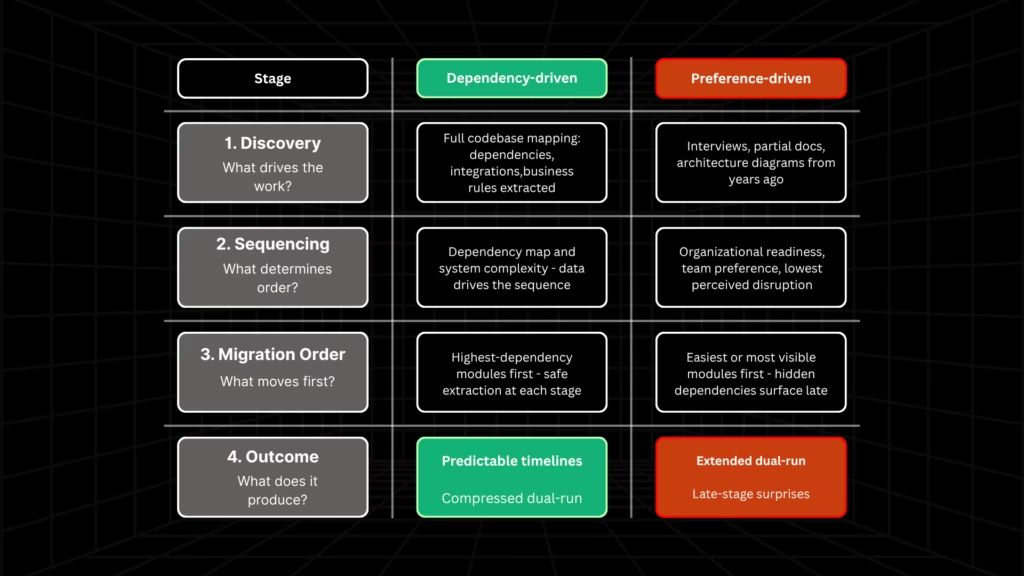
The Zions Bancorporation Sequencing Lesson
Zions Bancorporation’s transformation to TCS BaNCS is the US mid-market benchmark for what sequencing decisions actually cost.
The program ran 11 years, consolidating six operating environments onto a single platform and rationalizing approximately 500 deposit products to roughly 100.
The outcome demonstrated what modern core infrastructure enables: Zions deployed PPP loans in three days at the onset of the pandemic.
The sequencing lesson is the more applicable takeaway for programs beginning today. Zions acknowledged that deposits should have been migrated first but were migrated last due to organizational maturity constraints at the time.
Sequence should be governed by dependency mapping and system complexity, not organizational convenience. Programs that establish that sequence in the comprehension phase, before any migration work begins, are the ones that compress timelines.
Core Banking Vendors for US Mid-Market Banks in 2026
Incumbent Platforms
For US mid-market banks in the $1B–$10B asset range, three vendors serve the majority of the installed base and are each in active platform transition in 2026.
- Fiserv: CoreAdvance. Launched in early 2026, consolidating Premier, Precision, and Cleartouch. Banks currently on Premier are being migrated on Fiserv’s timeline. The question for existing clients is sequencing and readiness, not whether to migrate.
- Jack Henry: Cloud-Native Deposit Core. Targeting H1 2026, designed for the $500M–$5B range. The primary advantage is their implementation track record at comparable institution sizes and a migration model built around phased co-existence. Assess FedNow and RTP native support as the primary functional differentiator.
- FIS: Affinity Edge. Positioned at the upper mid-market tier ($3B–$10B). Banks on FIS Horizon should evaluate Affinity Edge against the full integration estate before committing. FIS’s implementation track record at the $1B–$5B tier is mixed.
Challenger Platforms
- Mambu. Best fit for banks launching new digital products or running a sidecar for a defined customer segment. Implementation timelines for a sidecar use case typically run 12 to 18 months. Not a direct full-core replacement without significant configuration work.
- Thought Machine: Vault Core. Best fit for banks in the $2B–$10B range with strong internal technology teams. Its Smart Contracts product configuration model gives banks direct control over product logic but requires engineering capability that most mid-market banks need to contract for. For a comparison of cloud-native core banking platforms and how they evaluate across the modernization lifecycle, see our platforms guide.
Six Criteria for Evaluating Any Vendor at the $1B–$5B Tier
- API readiness. Can the platform expose clean, documented APIs for all core functions, the prerequisite for FedNow, RTP, and every AI use case in the next three years?
- Cloud deployment model. Is it genuinely cloud-native or a lifted legacy system hosted on cloud infrastructure?
- Implementation track record at comparable asset size. Ask for reference clients in the $500M–$5B range specifically.
- Total cost of ownership over 7 years. Require a fully-loaded TCO model. Llicensing is the visible line item, not the real cost.
- Regulatory compliance support. Does the platform handle BSA/AML, CRA, and consumer compliance reporting programmatically?
- Exit and portability terms. Evaluate data portability at contract end before signing.
Why Do Core Banking Modernization Projects Fail?
According to IBM’s Institute for Business Value, 94% of core banking programs exceed their original timelines [3]. Six failure modes explain why.
1. Decision velocity collapse
Zions Bancorporation’s retrospective identified this as its primary constraint. The organization faced thousands of decisions per week across product, operations, regulatory, and customer dimensions simultaneously.
Technology was not the binding constraint. Governance was. Mid-market banks running a core transformation with a governance model designed for normal operations will encounter the same bottleneck.
2. Business rule opacity
Legacy cores accumulate business rules such as interest calculation logic, fee structures, product configurations, regulatory reporting mappings directly in application code, without separate documentation.
A rule not extracted and validated before migration is a latent defect in the new system. It may surface immediately on cutover or months later as a data integrity issue or regulatory finding.
This is the step most programs treat as a parallel workstream and most consistently fail on. Legacyleap’s Documentation Agent reconstructs business rules and embedded logic from source code before transformation begins, producing the documented specification that serves as the migration’s ground truth.
3. Data quality discovered too late
Banks typically discover the true state of their legacy data only after transformation is underway. Cross-era validation like ensuring a transaction originated in 1998 produces a correct result in a 2026 schema is a non-trivial problem that cannot be solved under program pressure.
The data quality audit must precede migration planning, not follow it.
4. Integration estate breakage
Mid-market banks operate 50–150 active third-party integrations, many partially or entirely undocumented.
Legacy point-to-point integrations do not survive a core migration intact. They require individual assessment, remediation planning, and sequenced transition. Industry analysis consistently identifies integration failures as the primary source of delay in core banking transformations.
Legacyleap’s Assessment Agent maps integration clusters and dependency chains as part of the pre-transformation comprehension phase, producing the dependency intelligence that makes sequencing decisions defensible rather than assumed.
5. Decommissioning neglect
Legacy retirement is chronically underfunded and underplanned. Dual-run periods extend 12 to 24 months beyond original projections in the majority of programs [3]. Every month of dual-run erodes the TCO benefit of modernization.
The legacy system must be actively decommissioned, with defined exit criteria and a funded plan, for the economics of modernization to work as modeled.
6. Regulatory underestimation
A bank in active core transformation operates under elevated supervisory risk. Treating regulatory engagement as an administrative step rather than a program-level risk variable is a governance failure. The OCC’s examination framework, covered in the next section, makes this explicit.
Business rule opacity and integration gaps are the two failure modes most consistently discovered too late — and both are identifiable before transformation begins if the comprehension work is done first. The $0 Modernization Assessment maps exactly this.
Regulatory Readiness During Active Transformation: What OCC and FDIC Examiners Will Assess
A bank in active core transformation is in a period of elevated operational risk. Under OCC Bulletin 2025-24, effective January 1, 2026, the OCC’s risk-based examination framework treats that elevated risk as a supervisory focus area [6]. Examiners will assess program governance quality, not just the technology outcome.
The question an OCC examiner asks is not what platform the bank is migrating to. It is whether the bank can demonstrate that the program has controls, documented decision rights, tested rollback capability, and evidence of correctness at every migration stage.
What examiners assess during an active core transformation:
| Examiner Focus Area | What It Means in Practice |
| Program governance structure | Documented decision rights across technology, operations, and risk functions, not just a project plan |
| Data migration integrity controls | Evidence that data transferred correctly at each stage, not attested at cutover only |
| Rollback capability | Documented, tested, and available at each migration phase, not theoretical |
| Customer impact mitigation | Active plans and communication governance, not reactive incident management |
| Third-party vendor management | Both core vendor and implementation partner are in scope under the interagency Third-Party Risk Management Guidance [6] |
The FDIC dimension. Lower-risk institutions may benefit from extended examination cycles under normal conditions. That flexibility does not apply during major technology events. A core migration qualifies as a major technology event and can trigger targeted examination activity regardless of a bank’s standard cycle position.
Capital planning. The OCC, FDIC, and Federal Reserve joint proposed rulemaking on modernized regulatory capital from March 2026 is an additional timing variable. Banks should factor regulatory capital rule timelines into modernization program planning.
A program that reaches cutover during a capital requirement transition creates compounding complexity that neither the program team nor the regulator benefits from.
Practical regulatory mitigation:
- Brief the primary regulator before the program launches, not after it is underway
- Build the governance framework to be examination-ready from day one
- Document rollback procedures at every migration phase with tested verification
- Maintain an accessible audit trail across every transformation decision
How Legacyleap Is Built for This Regulatory Standard
The governance architecture that satisfies a regulator is the same architecture that makes modernization safe. Legacyleap is built around that principle.
Every transformation the platform produces is diff-based. The proposed change is generated, displayed for human review, and applied only after engineer approval. The platform cannot merge, deploy, or apply code directly.
This architectural constraint produces a complete, reviewable audit trail across every modification made to the system. An examiner asking for evidence that the bank maintained control over its transformation process can be shown that trail.
The QA Agent generates behavioral parity validation before any transformed code is integrated. Parity checks run at the transformation level, producing documented evidence that migrated components behave correctly relative to their legacy equivalents. This is the evidence-of-correctness layer the OCC’s data migration integrity assessment requires.
For banks with regulatory constraints on cloud-based AI processing, Legacyleap deploys on-premise or within a VPC. No source code leaves the bank’s infrastructure at any stage of the process.
For a deeper look at how that architecture holds up in regulated environments, see our guides on enterprise-ready Gen AI modernization and secure AI-driven application modernization.
Conclusion: What a Structured Start Looks Like
The banks that succeed in core modernization treat comprehension as the foundation of the program. They know their system boundaries, their integration estate, their business rule documentation state, and their data quality before they select a vendor, commit to a migration approach, or begin any technical work.
The banks that struggle begin executing before they know what the program needs to contain. They discover business rules in production. They find undocumented integrations during cutover. They extend dual-run periods because rollback procedures were not tested. They receive supervisory attention because governance documentation was not program-ready.
The structured entry point, regardless of which migration approach or vendor a bank ultimately chooses, is a comprehension and dependency mapping exercise conducted before any program commitment is made.
Four questions need answers before moving forward:
- What does the system boundary actually contain?
- What integrations are active and documented?
- What business rules are embedded in application code?
- What is the true state of the data?
The $0 Modernization Assessment is the mechanism for establishing that foundation. It produces a dependency and module map, risk indicators, a modernization blueprint, architecture observations, effort and timeline ranges, and a structured modernization readiness view. No program commitment is required before the bank understands what the program needs to contain.
Request a $0 Assessment and get your dependency map, risk indicators, and modernization readiness view before committing to a program.
Book a Demo to see how Legacyleap’s governed transformation model works in a live banking modernization context.
FAQs
At the $1B–$5B tier, the choice depends on the current platform and contract position. Banks on Fiserv Premier are already in Fiserv’s CoreAdvance migration orbit and should evaluate readiness and sequencing rather than alternatives. Banks on Jack Henry SilverLake should assess the cloud-native deposit core against their FedNow and RTP roadmap. Banks on FIS Horizon need a full integration estate review before committing to Affinity Edge. For institutions open to challenger platforms, Mambu fits sidecar use cases, and Thought Machine fits institutions with strong internal engineering. No vendor decision should precede a dependency and integration audit.
A traditional core banking system is a monolithic platform handling all banking functions (deposits, loans, payments, general ledger) within a single, tightly coupled architecture. A composable banking platform separates those functions into independently deployable modules, each accessible via API. The practical difference is speed: a composable architecture allows a bank to replace one domain (payments processing, for example) without touching the rest of the system. Most challenger platforms are composable by design. Most incumbent platforms are moving toward it incrementally. For mid-market banks evaluating vendors, the relevant test is whether the platform can expose clean APIs for every core function independently, not whether the vendor uses the word “composable” in its marketing.
The OCC’s risk-based examination framework, effective January 1, 2026, treats an active core transformation as an elevated operational risk event. The practical requirement is governance documentation: decision rights across technology, operations, and risk functions must be documented before the program launches, not assembled for an examination. Rollback capability must be tested at every migration phase, not theoretically. Data migration integrity controls must produce evidence of correctness at each stage, not just at cutover. Banks that brief their primary regulator before the program begins, rather than after, typically experience more predictable examination outcomes during the transformation period.
Dual-core coexistence is the operational period during which a bank runs both its legacy core and its new core simultaneously. The legacy core continues serving the existing book while the modern core handles migrated products, new products, or a pilot customer segment. The intended duration is defined by the migration roadmap. The actual duration is typically longer. EY’s 2025 analysis found that decommissioning timelines extend 12 to 24 months beyond original program estimates in the majority of programs. The financial risk is direct: every month of dual-run carries the operational cost of two cores, eroding the TCO benefit of modernization until the legacy system is fully decommissioned. Defining explicit exit criteria and a funded decommissioning plan at program outset is the only reliable way to contain this.
Legacy point-to-point integrations do not survive a core migration intact. Each integration must be individually assessed, remediated, and transitioned to the new core’s API model. For mid-market banks operating 50 to 150 active third-party connections, many of which are partially or entirely undocumented, this is a discrete workstream, not an afterthought. Integrations that are not mapped and sequenced before migration begins typically fail during or after cutover. Under the OCC and FDIC interagency Third-Party Risk Management Guidance, the bank owns this risk regardless of which party, core vendor or implementation partner, is executing the transition.
Core banking modernization is infrastructure work. It replaces or upgrades the systems that process transactions, manage accounts, and produce regulatory reporting. Digital banking transformation is the customer-facing and product layer built on top of that infrastructure – mobile apps, digital onboarding, personalized product experiences. The distinction matters because many banks have invested heavily in digital transformation without modernizing the core beneath it. The result is a modern customer experience layer sitting on a legacy processing engine, which constrains real-time capabilities, limits API access, and accumulates integration debt. Core modernization is the prerequisite that makes the digital transformation investment durable.
References
[1] American Bankers Association. 2024 Core Platforms Survey.https://www.aba.com/news-research/analysis-guides/2024-core-platforms-survey
[2] IDC Financial Insights. “Future Ready Payments Platforms Enabling the Next Phase of Growth for Banks.” June 2023. Via IBS Intelligence:https://ibsintelligence.com/ibsi-news/banks-to-spend-57bn-on-legacy-paytech-by-2028-study-shows/
[3] EY. “How to Avoid Common Pitfalls When Modernizing Banking Systems.” July 2025. https://www.ey.com/en_gl/insights/financial-services/emeia/how-to-avoid-common-pitfalls-when-modernizing-banking-systems
[4] IBM Institute for Business Value. “The 94% Core Banking Problem.” September 22, 2025.https://www.ibm.com/thought-leadership/institute-business-value/en-us/report/core-banking-modernization
[5] OCC. Bulletin 2025-24: Examinations — Frequency and Scope for Community Banks. October 6, 2025.https://www.occ.treas.gov/news-issuances/bulletins/2025/bulletin-2025-24.html
[6] OCC, Federal Reserve, FDIC. Interagency Guidance on Third-Party Relationships: Risk Management. OCC Bulletin 2023-17, June 6, 2023.https://www.occ.gov/news-issuances/bulletins/2023/bulletin-2023-17.html