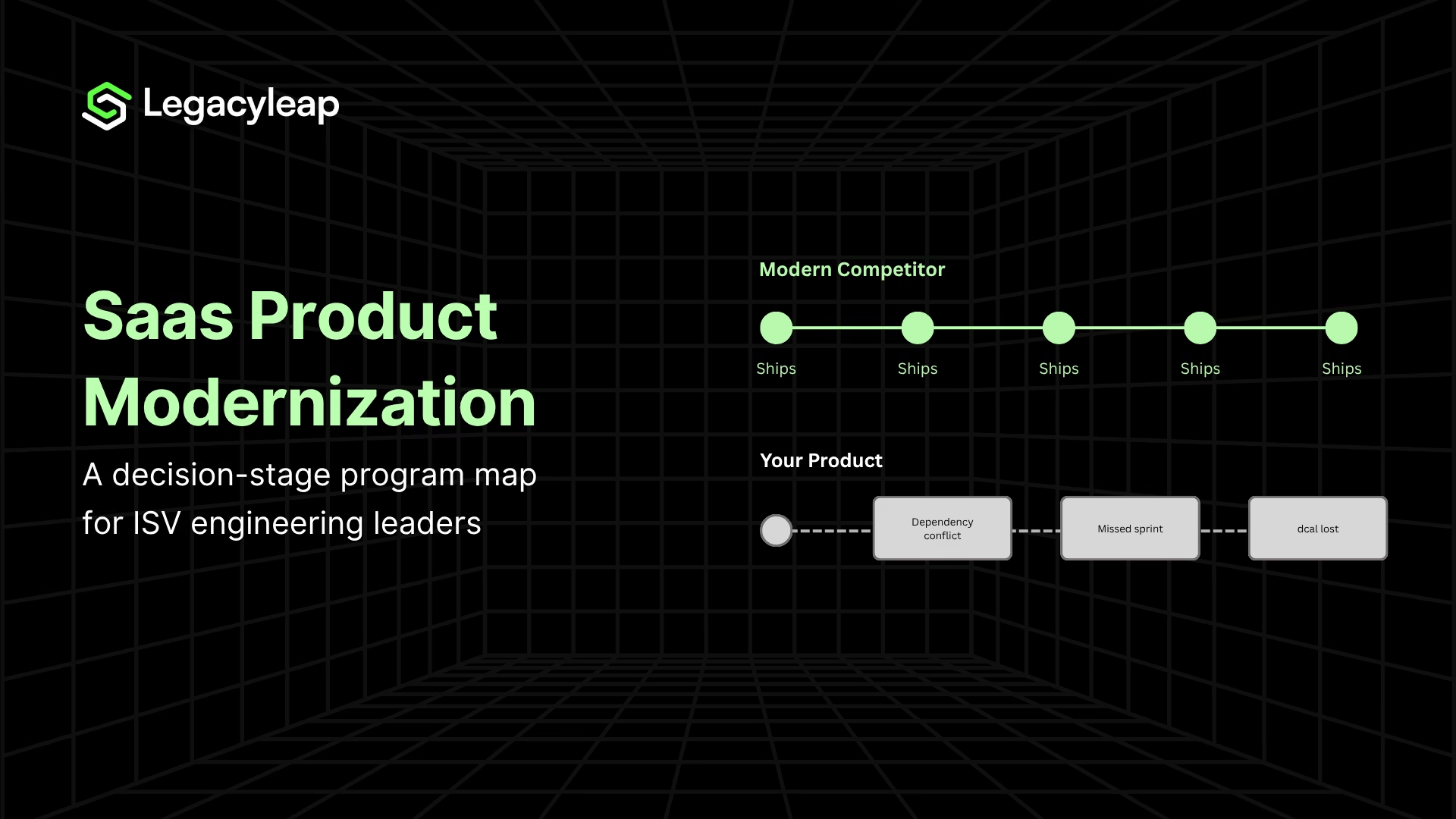
Your competitor shipped three new integrations last quarter. You spent the same sprint resolving a dependency conflict that has been in the backlog since 2021. This is not a resourcing problem or a prioritization problem. It is an architecture problem, and it is showing up in your pipeline.
Longer demo cycles, failed security questionnaires, missing native integrations, and slower onboarding all trace back to the same root cause. The architecture gap between your product and a competitor on a modern stack compounds every quarter it goes unaddressed. This is the decision-stage lifecycle map for closing it.
SaaS product modernization is the process of restructuring a software company’s core product architecture to remove the constraints that accumulated during its original build. This includes the codebase, data layer, integration surface, and deployment model.
For an ISV, this is not an IT initiative. It is a product and commercial initiative because the architecture is the product, and the product is the business.
5 Signs Your SaaS Architecture Is Losing You Deals
- Demo cycles are getting longer because prospects need a custom configuration that your product cannot handle natively.
- Enterprise buyers are failing you on security questionnaires due to legacy authentication patterns and undocumented data flows.
- Competitors offer native integrations to platforms your product requires a custom connector to reach.
- New customer onboarding takes significantly longer than your competitors’, affecting win rates and expansion revenue.
- Your engineering team spends more than 50% of its sprint capacity on maintenance, with little left for shipping product.
What Your Legacy SaaS Architecture Is Already Costing You
The “we’re still profitable” objection misframes the question. The right question is what staying on the current architecture is already costing, quarter over quarter.
The Operational Cost of Technical Debt
Technical debt does not manifest primarily as maintenance cost. It generally manifests as velocity loss.
Every quarter spent managing legacy dependencies is a quarter competitors spend shipping product. IBM research found that 81% of executives identify technical debt as a direct constraint on their AI adoption, and that it adds 15 to 22 percent to delivery timelines on average [2].
The compounding effect is the argument: dependency rot accumulates, documentation decays, and compliance requirements layer on top of an architecture that was never designed to accommodate them.
How Legacy Architecture Shows Up in the Pipeline
The competitive damage is specific, not abstract. Legacy SaaS architecture typically surfaces in deals through four mechanisms:
- Longer demo cycles: Prospect environments require custom configuration that a modern API-driven product handles natively.
- Failed security questionnaires: Legacy authentication patterns, shared infrastructure, and undocumented data flows create compliance gaps that enterprise buyers flag.
- Missing integrations: Competitors offer native connectors to the platforms prospects already use; your product requires a custom connector or a middleware layer.
- Slower time-to-value: Onboarding a new customer on a legacy product takes longer, which affects both win rates and expansion revenue.
There is a fifth mechanism that does not show up in the pipeline but shows up in hiring. Senior engineers do not want to work on legacy stacks. When the codebase repels the talent needed to modernize it, the program becomes progressively harder to staff.
The ISVs that delay the longest are often the ones who lost the engineers who understood the original architecture, which means the assessment phase alone costs more, because the institutional knowledge no longer exists in the building.
The Valuation Dimension
Modern SaaS architecture commands a 57% premium in revenue multiples over all software; 4.1x versus 2.6x median, across 3,183 transactions in 2024 [1].
The EBITDA premium is 88% (19.2x versus 10.2x). Technical due diligence now examines code quality, deployment frequency, test coverage, and architecture scalability as a standard process, not as a signal of concern.
The preparation window before a fundraising or exit process is 12 to 18 months. Architectural remediation cannot be started after the process opens. It needs to begin well before.
The Compounding Cost of Doing Nothing
Every quarter of deferral makes the program more expensive, not less. The mechanism is specific: undocumented dependencies accumulate as engineers build on top of existing architecture without capturing what changed and why.
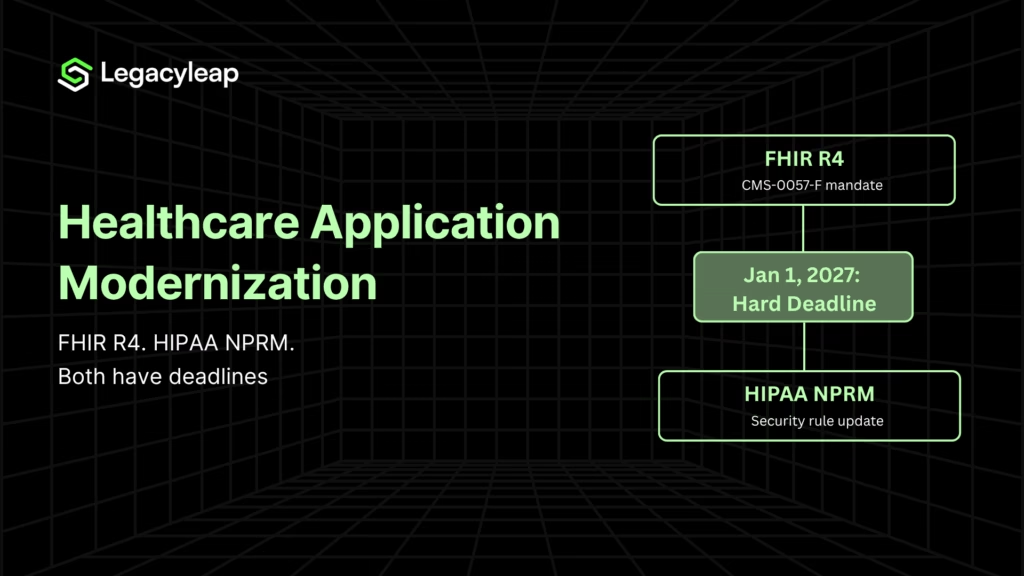
Compliance requirements such as SOC 2, HIPAA, and FedRAMP, depending on the vertical, layer onto systems that were never designed to be audited. Test coverage, already thin, erodes further as the codebase grows. And the engineers who carry institutional knowledge of the original design decisions leave or move on.
By the time the modernization program is finally approved, the assessment phase alone takes longer and costs more than it would have 18 months earlier, before the codebase grew by another 30 percent and two of the three engineers who understood the billing module departed.
The board question is not “can we afford to modernize?” It is whether the company can sustain what staying on this architecture is already costing, compounding, every quarter.
The Three Reasons ISV Modernization Programs Collapse Mid-Execution
Most ISV modernization programs do not fail during execution. They fail at the points where scope is set, decisions are made without the right inputs, or architecture decisions are rushed. Three failure modes are responsible for the majority of program collapses.
Failure Mode 1: Transforming Before Understanding
Missing or outdated documentation forces reverse engineering across every module. Business logic embedded in two or three engineers’ heads is not captured in code or documentation. And when those people leave or move, the program stalls.
Undiscovered dependencies are the single largest driver of cost overruns and timeline extensions in ISV modernization.
Scope estimates made before full codebase analysis is complete are structurally unreliable. The compounding effect of undiscovered dependencies means that programs that skip a proper assessment phase routinely expand 25 to 30 percent beyond initial scope mid-execution, after the board case has been made and resources have been committed [3].
Failure Mode 2: Making the Rewrite-vs-Refactor Call Without Measurable Inputs
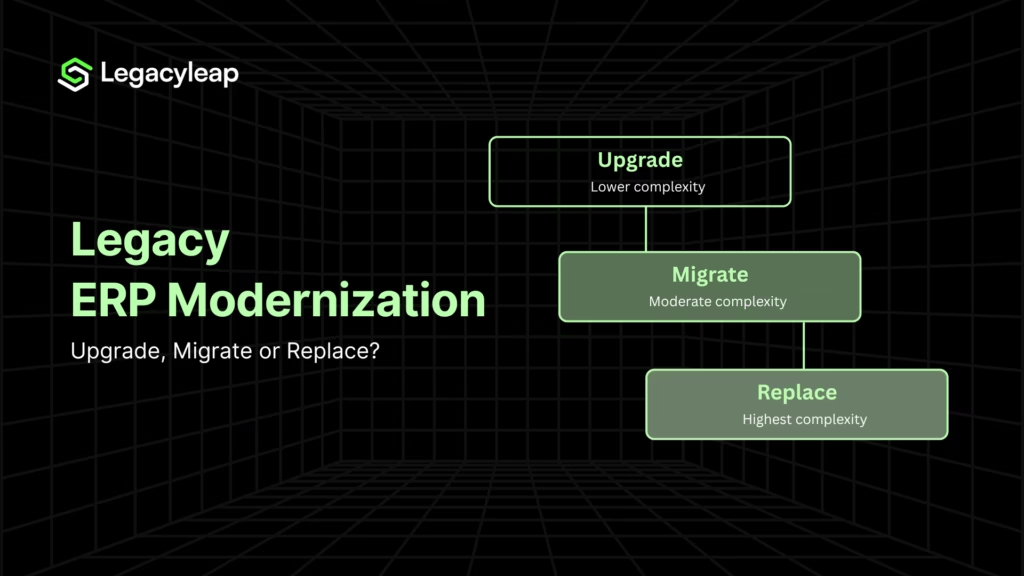
The rewrite-vs-refactor decision is not a philosophical debate. It is a diagnostic exercise requiring four specific inputs before a recommendation can be made:
- Test coverage percentage: Below approximately 20%, refactoring without a regression safety net carries high behavioral risk.
- Sprint capacity ratio: Above 60% maintenance load, modernization needs a capacity intervention before scoping begins.
- Architecture coupling density: High coupling requires data boundary work before code work.
- Competitive timeline: Under 12 months, a full rewrite is off the table.
Full rewrites made without these inputs routinely require 36 to 48 months to reach positive ROI, a timeline most programs were never resourced or approved for.
For a deeper look at how the refactoring versus replatforming decision plays out in practice, the legacy application modernization: refactoring vs replatforming breakdown covers the tradeoffs in full.
Failure Mode 3: Extracting Services Before Understanding Boundaries
Premature microservice extraction without domain-driven boundary identification produces a distributed monolith. This includes all the operational complexity of microservices, none of the architectural benefits.
The canonical rule from Chris Richardson at microservices.io applies directly: do not extract a service before you understand its boundaries [3].
Without an Anti-Corruption Layer, new services inherit the same technical debt from the monolith, which defeats the purpose of the extraction and leaves the architecture in a worse operational state than before the program began.
The monolith vs microservices decision framework is relevant here for ISV teams working through boundary identification before committing to service extraction.
$0 Modernization Assessment. Map your dependencies and right-size scope before you commit resources. Start here.
The Five-Stage ISV Modernization Lifecycle: What a Governed Program Actually Looks Like
Each stage answers a specific decision question, produces a concrete output, and prevents a named failure mode. Skipping a stage does not compress the timeline, but transfers the cost forward, where it surfaces as scope expansion, rework, or a behavioral regression that reaches a paying customer.
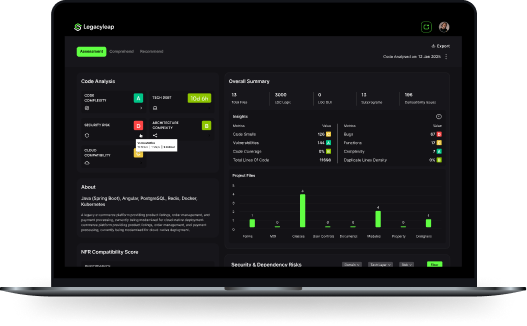
Stage 1: Assess
Dependency mapping, risk identification, and scope right-sizing. The output is a modernization blueprint with effort and timeline ranges grounded in actual codebase analysis, not estimates made from the outside.
What breaks without it: cost estimates are wrong, timelines are wrong, and the board case collapses when scope expands mid-program.
Stage 2: Comprehend
Reconstruct missing documentation, such as module responsibilities, data flows, business rules, and API inventories. Map the logic that lives in engineers’ heads rather than in code or documentation.
For ISV products that have grown organically for 10 or more years, this stage typically surfaces business rules that exist nowhere in writing. This could include:
- Logic that governs pricing tiers,
- Customer-specific configurations, or
- Edge cases in the billing or reporting layer that engineers handle from memory.
Losing that logic during transformation is how behavioral regressions reach paying customers. Comprehend exists to capture it before any code changes.
What breaks without it: Transformation decisions are made on incomplete understanding, business rules are dropped during migration, and the new architecture inherits the same structural problems as the old one.
Stage 3: Plan
This is where the rewrite-vs-refactor-vs-rearchitect decision happens, grounded in the measurable inputs from Stages 1 and 2. The decision matrix below maps those inputs to a recommended approach:
| Input signal | Refactor | Rearchitect / Replatform | Rewrite |
| Test coverage | >40% | 20–40% | <20% (safety net must be built first) |
| Sprint capacity on maintenance | <40% | 40–60% | >60% (intervention required before scoping) |
| Coupling density | Low | Medium; boundary work first | High (data architecture precedes code work) |
| Competitive timeline | Flexible | 12–24 months | Off the table at <12 months |
| ROI timeline | 6–12 months | 12–18 months | 36–48 months; resource accordingly |
| Integration surface complexity | Native APIs exist | Partial, connector-dependent | No modern API layer |
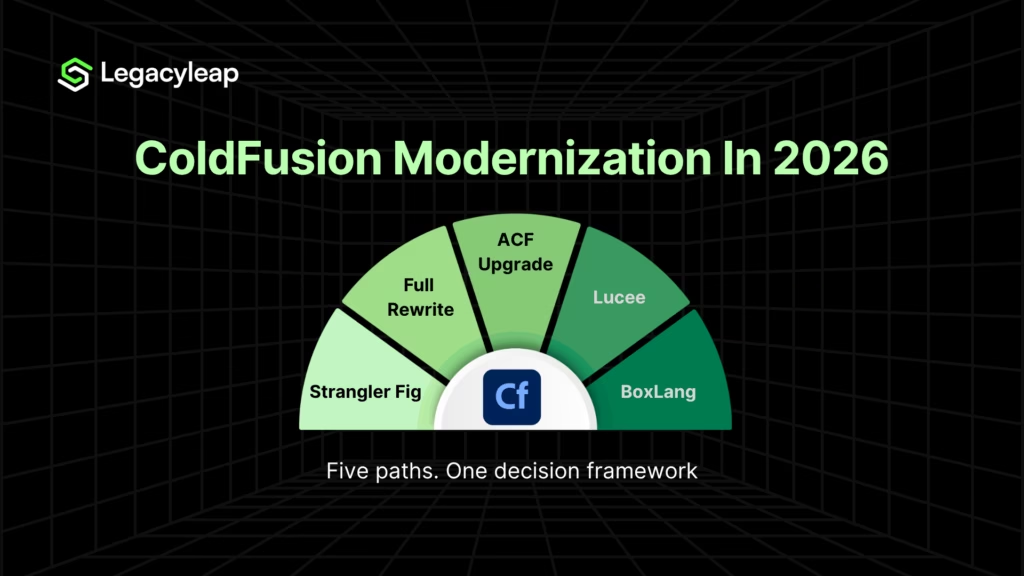
How the Strangler Fig Pattern Works for ISV Modernization
The strangler fig pattern is an incremental modernization approach where new functionality is built on a modern architecture alongside the legacy system, gradually replacing it without a full cutover.
For an ISV, this matters because it means the legacy product continues serving paying customers while the modern surface grows around it. The approach only works when service boundaries are correctly identified first.
Extracting a service before mapping its domain boundary produces a distributed monolith, which adds operational complexity without delivering architectural benefit.
Modernizing Tenancy Models Without Taking Your Product Offline
Many legacy ISV products were built with a single-tenant or shared-schema multi-tenant model, which was an architectural decision that made sense at the time but creates significant risk during modernization.
Re-architecting tenancy is a data architecture problem, not a code problem. A data isolation failure during migration reaches paying customers, not internal stakeholders, which is a materially different category of risk.
For this reason, tenancy model planning must be treated as a separate workstream, sequenced before service extraction begins rather than bundled into the general modernization roadmap.
The sequencing matters: service boundaries drawn without accounting for tenancy boundaries will need to be redrawn later, at a significantly higher cost.
Stage 4: Transform
Governed, diff-based, reversible code transformations are executed incrementally while the legacy product continues serving customers in production. Each cycle produces a reviewable diff that engineers approve before it is applied.
The AI works within the full codebase context, not in isolation against individual files, and does not merge or deploy independently.
For an ISV, a behavioral regression does not surface internally but in a customer support ticket or a churn conversation. That is the constraint the governed approach is designed to prevent.
For teams running this approach, the incremental modernization execution model covers how parallel-run structures are maintained across legacy and modern surfaces during the transition.
Stage 5: Validate
Behavior parity checks confirmed before cutover, not assumed from the absence of obvious failures.
For ISV products built before automated testing was standard practice, this stage cannot be skipped because the team knows the system. That knowledge lives in people, not in a test suite, and people leave.
Legacyleap’s QA Agent generates a regression safety net from the existing codebase before transformation begins, so parity is confirmed against a defined baseline rather than discovered post-release.
For ISVs in regulated verticals such as financial services and healthcare in particular, behavior parity validation carries compliance weight as well as product weight, and cannot be deferred to post-release.
What AI-Native Competitors Mean for Legacy ISV Products
The competitive pressure on legacy ISV products is no longer limited to modern-stack SaaS companies.
AI-native competitors are entering established verticals with products built from the ground up to support AI-first workflows such as real-time data pipelines, API-first architecture, and model integration at the product layer.
A legacy ISV cannot compete with this by adding an AI feature to an existing monolith. The architectural preconditions for AI-readiness, like a clean API layer, event-driven data flows, and modular service boundaries, are the same preconditions that a modernization program produces.
Modernizing now is not just a competitive catch-up play. It is the prerequisite for competing in the next product cycle.
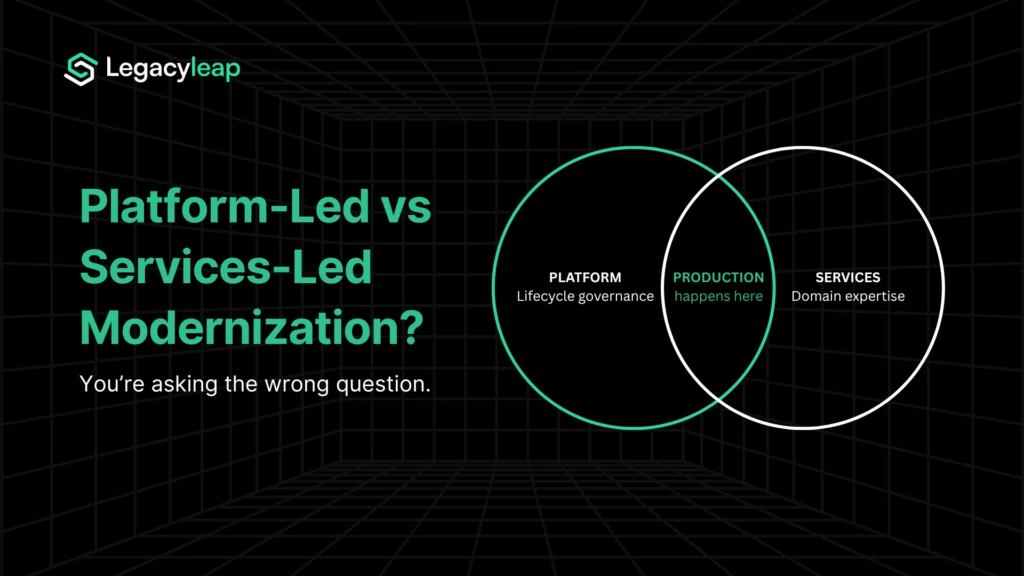
How Legacyleap Governs the Full ISV Modernization Program
A development shop will refactor code. A copilot will rewrite a function. Neither governs a modernization program. Legacyleap operates at the system level — full codebase comprehension before any transformation, governed change at every stage, validated parity before cutover. That is architecturally different from both.
Agent-to-Stage Map
| Agent | Stage | Primary function | Key outputs |
| Assessment Agent | Assess | Dependency mapping, risk identification, scope right-sizing | Modernization blueprint, effort and timeline ranges |
| Documentation Agent | Comprehend | Reconstruct missing documentation, map business logic | Architecture diagrams, module boundaries, data flow maps, business rule documentation |
| Recommendation Agent | Plan | Modernization path selection grounded in codebase analysis | Migration path options, target framework recommendations, sequenced roadmap |
| Modernization Agent | Transform | Governed code transformation.Diff-based, reversible, human-reviewed | Code diffs, refactored modules. AI does not merge or deploy independently |
| QA Agent | Validate | Behavior parity checks, automated regression coverage generation | Parity check results, test cases for systems with no legacy coverage, pre-cutover verification |
Three ISV-Specific Differentiators
The platform’s differentiation is best understood as a set of customer-facing protections, not platform features.
- Full-codebase comprehension before transformation. The agents work with grounded context of the entire codebase, not isolated files or prompts. This is what prevents the interpretation errors that propagate into a new architecture and the business logic losses that reach customers.
- Diff-based, human-reviewed, reversible transformations. For an ISV, this is a customer protection mechanism. Every change is reviewed before it touches the live product. The Modernization Agent does not merge or deploy independently. The engineering team retains full control at every decision point.
- Behavior parity is validated, not assumed. The QA Agent generates the regression safety net for ISV products with no legacy test coverage. Parity is confirmed before cutover, not discovered post-release.
What This Looks Like Across ISV Stacks
The governed lifecycle applies regardless of the underlying stack.
- A financial services ISV running a VB6-based product through Legacyleap achieved 70 to 80% acceleration in code conversion while meeting strict compliance requirements, with full audit traceability maintained throughout.
- A transport technology company modernizing a complex EJB 3 system reduced overall effort by 50% through automated code comprehension and business logic extraction, without disrupting the customers it was serving.
Different stacks, different verticals but the same governing structure: comprehension before transformation, human review at every change point, parity confirmed before cutover.
The Primary ISV Proof Point: A Fuel Distribution Software Company
A UK and Ireland-based bulk fuel distribution software company built its entire business on a VB6 product. Because the software served paying customers continuously, a full rewrite was not viable on either cost or risk grounds.
The program had to move the product to a modern architecture without taking it offline.
Running the modernization through Legacyleap, the company achieved:
- 70% of code transformation and testing automated
- 80% reduction in manual effort
- 60% reduction in cost
- 40% acceleration in feature deployment speed
- Zero customer downtime throughout the program
What makes this the right reference point for ISV readers is the context. This is not an enterprise IT department migrating an internal application with a defined maintenance window.
It is a product company protecting a live commercial product and its paying customer base throughout a full architectural modernization.
For regulated ISV verticals where source code cannot leave the enterprise environment, Legacyleap supports on-prem and VPC-hosted LLM deployment, with the full modernization program running within the client’s infrastructure boundary.
Legacyleap platform data shows 40 to 50% reduction in overall modernization effort across programs, with up to 70% on specific stacks and scopes.
For a look at how VB6 to .NET modernization is handled at the code level, see VB6 to .NET Modernization.
$0 Modernization Assessment. See exactly where your program is exposed before scoping begins.
The Program You Need to Run and the No-Cost Way to Start
ISV modernization is a solvable program. It succeeds when assessment precedes transformation, comprehension precedes planning, and parity validation closes every cycle.
Skipping stages does not accelerate the program. It creates the failures Section 3 named, at the worst possible point in execution.
The architecture gap between your product and a competitor on a modern stack compounds every quarter. The preparation window before a fundraising or exit process is 12 to 18 months and it is already running.
Before the program is scoped, the $0 Modernization Assessment produces a dependency map, risk profile, modernization blueprint, and effort and timeline ranges. It is Stage 1 of the lifecycle, built to be structured and governed, at no cost and no commitment.
It gives your team the inputs required to make the rewrite-vs-refactor decision correctly, resource the program accurately, and defend the board case with credible data.
To see the full five-agent lifecycle platform before committing to the assessment, book a demo.
FAQs
Buyers examine deployment frequency, test coverage, dependency age, documentation completeness, and tenancy model, specifically whether the architecture supports clean data isolation between customers. Legacy architecture does not just suppress multiples in theory. It generates specific findings in diligence reports that buyers use to renegotiate price or walk away entirely. The 12 to 18-month preparation window exists because remediating those findings takes time, and the process will not pause while you do it.
The crossover is rarely a single threshold. It is a convergence. When maintenance exceeds 60% of sprint capacity, the engineering team stops being a product development asset. When senior engineers are declining offers because of the stack, retention risk concentrates in the two or three people who understand the core modules. When compliance gaps are losing enterprise deals, the cost starts showing up in the pipeline, not just overhead. For most ISVs, the crossover happened earlier than they recognized.
AI-native competitors are not just using newer tools. They are built on foundations that make AI integration native rather than a bolt-on. A clean API layer, event-driven data flows, and modular service boundaries allow a product to route data to a model and act on outputs at the customer layer without rebuilding each time. A legacy monolith can add an AI feature. It cannot become an AI-integrated product without the underlying architecture changing first. That gap compounds every quarter.
This is one of the most common situations ISV programs face, and it is why the Comprehend stage runs before any transformation begins. When institutional knowledge has walked out the door, the Documentation Agent reconstructs it from the codebase itself. This includes module responsibilities, data flows, and business rules derived from what the code actually does rather than what someone remembers. The program can run without the original engineers. The risk is starting transformation before that reconstruction is complete.
Three failure points are most common. Authentication and access control gaps fail SOC 2 Type II and enterprise security questionnaires. Shared-schema multi-tenant models cannot demonstrate clean data isolation, which is a hard requirement for HIPAA and most large enterprise procurement processes. Missing audit trails and observability gaps block FedRAMP and regulated-industry buyers at the questionnaire stage. Enterprise procurement teams have binary thresholds on compliance. A legacy architecture that cannot pass removes the company from consideration before the product evaluation begins.
References
[1] Software Equity Group / Pitchbook. (2024). SaaS M&A Report — 3,183 transactions. https://softwareequitygroup.com/
[2] IBM Institute for Business Value. (2025). Technical debt and AI adoption constraints. https://www.ibm.com/thought-leadership/institute-business-value/
[3] Richardson, C. microservices.io — Decomposing the monolith: service boundary extraction and the Anti-Corruption Layer. https://microservices.io/