Aviation’s Cybersecurity Regulators Have Moved. The Legacy Stack Hasn’t.
Three regulatory instruments are now simultaneously active in aviation cybersecurity, and none of them are operating as guidance.
TSA Security Directive SD 1544.240 requires TSA-regulated airports and Part 121 carriers to maintain active Cybersecurity Implementation Plans covering network segmentation, patch management, continuous monitoring, and access controls [1]. TSA’s January 2025 Enforcement Sanction Guidance lists operating without an approved CIP as a sanctionable violation.
The FAA Reauthorization Act of 2024 gives the FAA exclusive rulemaking authority over civilian aircraft cybersecurity and directs the establishment of both a NAS Cyber Threat Management Process and a Civil Aviation Cybersecurity Rulemaking Committee.
The FAA’s August 2024 NPRM converts current directives into binding airworthiness regulations. When that rule finalizes, operator discretion ends.
Aviation is now one of the industries where 2026 enforcement is converging. That is the frame for everything that follows.
The article’s argument is not that airlines lack compliance programs. It is that the legacy systems running airline operations, such as crew tracking, dispatch, ETOPS monitoring, ops control, are structurally incapable of producing what those programs now require.
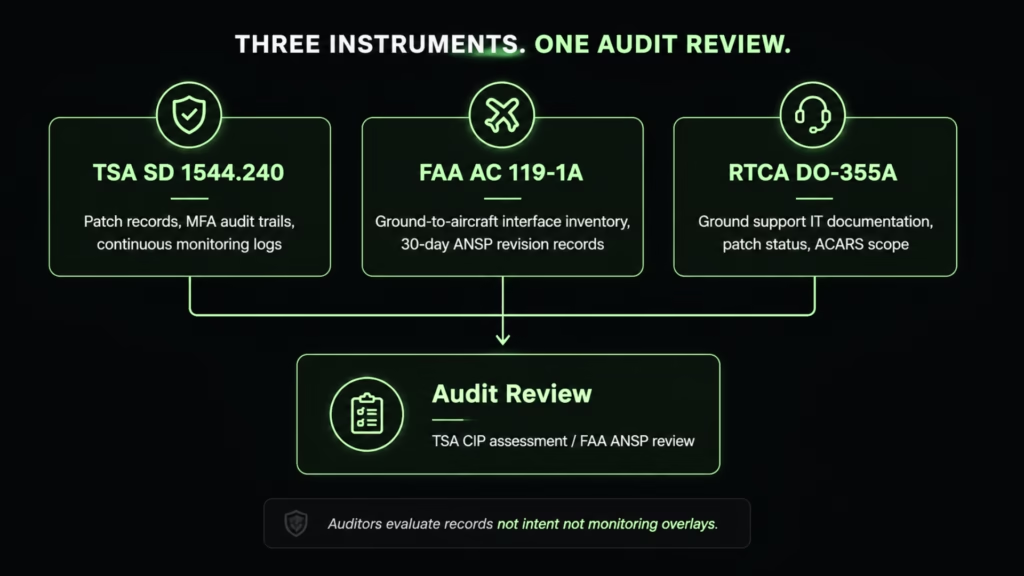
What TSA and FAA Auditors Check: Evidence Requirements by Instrument
TSA Security Directive SD 1544.240 requires TSA-regulated airports and Part 121 air carriers to maintain a Cybersecurity Implementation Plan covering network segmentation, access control, continuous monitoring, and patch management for all critical cyber systems.
Non-compliance with an approved CIP is a sanctionable violation under TSA’s January 2025 Enforcement Sanction Guidance and can result in fines, suspension, or certificate revocation.
The compliance obligation resolves to a specific set of auditable IT deliverables. Understanding what those deliverables are is the prerequisite for understanding where the legacy stack fails.
TSA SD 1544.240 requires carriers to produce and maintain:
- Network segmentation documentation with enforced OT/IT boundaries
- 90-day patch records for all Tier 1 and Tier 2 systems, with documented exceptions
- Application-level event logs capable of supporting anomaly detection and forensic review
- Application-layer MFA audit trails, not just perimeter authentication records
- An annual Cybersecurity Assessment Plan with documented owners and review cadence
- Periodic third-party penetration testing, scoped and tracked to remediation
Each item is an evidence obligation. A CIP assessment does not evaluate intent; it evaluates records.
- FAA AC 119-1A (OpSpec D301) adds a continuous obligation: every Boeing or Airbus manufacturer security document update triggers a 30-day window in which the carrier must verify that all ground-interfacing IT systems remain consistent with the updated security posture and revise the Aircraft Network Security Program accordingly. That verification is evaluated against a documented, current inventory of ground-to-aircraft interface systems, not a general statement of compliance.
- RTCA DO-355A explicitly scopes the requirement to ground support information systems: software loading platforms, maintenance record systems, ACARS communications infrastructure, and security log extraction from aircraft networks. Legacy applications in any of these functions are within scope, regardless of the rest of the carrier’s compliance posture.
When the FAA’s August 2024 NPRM finalizes, RTCA DO-326B becomes binding. Current carrier discretion over which standards to apply and how to document them will be replaced by requirements with no operator opt-out.
| Evidence Required | Regulatory Instrument | Audit Trigger |
| Network segmentation documentation (OT/IT boundaries) | TSA SD 1544.240 | CIP assessment |
| 90-day patch records for Tier 1/2 systems | TSA SD 1544.240 | CIP assessment |
| Application-level event logs and anomaly detection records | TSA SD 1544.240 | CIP assessment |
| Application-layer MFA audit trails | TSA SD 1544.240 | CIP assessment |
| Ground-to-aircraft interface system inventory | FAA AC 119-1A (OpSpec D301) | ANSP review |
| ANSP revision records (30-day obligation) | FAA AC 119-1A | Each manufacturer security update |
| Ground support IT documentation and patch status | RTCA DO-355A | FAA NPRM (binding on finalization) |
What Happens If an Airline Fails a TSA Cybersecurity Audit
TSA’s January 2025 Enforcement Sanction Guidance lists operating without an approved Cybersecurity Implementation Plan as a sanctionable violation.
Consequences scale from warning letters and compliance orders to civil monetary penalties and, in severe cases, suspension or revocation of operating certificates. A failed CIP assessment does not result in an immediate shutdown, but it triggers a remediation clock with TSA oversight on every subsequent step.
The enforcement posture has changed in one specific way that matters operationally: the January 2025 guidance removes ambiguity about what constitutes a violation. Prior to that update, TSA’s enforcement language left room for carriers to argue that a partially implemented CIP represented a good-faith compliance effort.
That argument is no longer available. An incomplete or unapproved CIP is, by the current guidance, a sanctionable condition, not a finding subject to remediation before penalties attach.
For Part 121 carriers, certificate-level consequences are the operational ceiling. The more immediate exposure for most carriers is the remediation clock itself: TSA oversight on every subsequent compliance step, compressed timelines, and the documentation burden that a remediation engagement creates on top of normal operations.
Carriers that enter that process with undocumented legacy systems face it without the foundation the process requires.
Why Legacy Aviation Stacks Cannot Meet These Requirements
The relevant distinction is between operational failure and structural failure.
- Operational failure is misconfiguration, a setting correctable through process improvement.
- Structural failure is architectural: the system cannot produce the required output because it was not built to, and no configuration change, overlay, or compensating control will change that.
The legacy stacks running airline operations fail in the second category. A North American carrier flagged by FAA auditors in 2025 was running a VB6 ETOPS compliance monitor with 11,000 lines of code, four database integrations (Informix, Oracle, SQL Server, Access), zero documentation, mandatory December 2025 remediation deadline. Nobody could map what systems it touched. That is not an edge case. It is what a TSA CIP assessment finds when it hits an undocumented legacy system.
The legacy stacks running airline operations fail in the second category.
Patch Management
TSA’s 90-day patch cycle requires an active vendor patch stream. VB6, Classic ASP, Java EE (pre-8), and EJB have no such stream. The requirement is not periodically missed, but is permanently unmet. There is no patch to apply because no patch will be issued.
The CISA Known Exploited Vulnerabilities catalog documents 1,484 confirmed-exploited CVEs as of 2025, including vulnerabilities from 2007 through 2017 actively weaponized in current attacks [2]. A carrier running these stacks cannot close these exposures through patch management because the channel no longer exists.
Continuous Monitoring and Access Control
TSA CIP continuous monitoring requires application-level event streams. Systems built in the VB6 and Classic ASP era predate structured logging as a standard practice as they produce no such stream. Network-layer monitoring overlays detect perimeter activity; they do not produce the application audit trail a forensic reviewer requires. Adding a SIEM to the perimeter does not close the gap.
The same logic applies to access control. Application-layer MFA event records are a CIP audit requirement. Legacy session management in VB6 and Classic ASP cannot produce them. Proxy logs capture authentication at the network boundary; they do not close the application-layer authentication chain that an auditor will examine.
The ANSP 30-Day Revision Problem
The FAA’s 30-day revision obligation requires carriers to certify that all ground-interfacing systems remain consistent with updated manufacturer security posture. That certification requires current, documented system inventories with traceable ground-to-aircraft interface records.
The carrier from the opening of this section is the exact illustration. Zero documentation means the 30-day clock expires, and the required artifact cannot be produced because the system was never mapped.
That is the structural problem. It cannot be solved by process improvement. It requires knowing what you have.
| Stack | Aviation Function | Primary Compliance Failure |
| VB6 | Crew tracking, dispatch, ETOPS monitoring | No patch stream; no structured logging; no dependency documentation |
| Classic ASP / .NET Framework 1.x–4.x | Weight and balance, ops control | No application-level event records; no MFA audit trail |
| Java EE / EJB | OCC systems, crew scheduling | No active vendor security updates; no interface documentation |
| Undocumented ACARS middleware | Aircraft-to-ground communications | Outside scope of any compliance review; RTCA DO-355A non-compliant by omission |
Cyber insurance underwriting now flags the same legacy stacks that TSA auditors target. The convergence is not coincidental as both are evaluating the same structural exposure.
Before any compliance program can be credibly executed, you need to know exactly what you’re dealing with in which systems interface with aircraft networks, where the patch gap sits, and what is undocumented.
Legacyleap’s $0 Modernization Assessment produces that map. No modernization commitment required.
The Incidents Are Not Warnings. They Are Documentation.
| Incident | Date | Financial Impact | Stack Failure | Regulatory Consequence |
| Delta / CrowdStrike | Jul 2024 | $500M recovery cost | Crew-tracking architecture could not recover without manual intervention | DOT investigation opened |
| Southwest Airlines | Dec 2022 | $140M DOT civil penalty | Crew reassignment software failed under cascading volume | Largest DOT consumer penalty ever assessed |
| Sea-Tac / Rhysida | Aug 2024 | $6M ransom demanded | Ransomware entered through legacy employee and parking systems | 90,000 individuals affected |
The structural failures described above have already produced documented, quantified consequences. Three incidents in the past four years establish what the legacy stack costs when it encounters operational stress.
- Delta Air Lines / CrowdStrike (July 2024). The CrowdStrike update is widely described as the trigger for Delta’s collapse. It was not. It exposed an existing condition: Delta’s crew-tracking and scheduling stack could not recover from an infrastructure event without manual intervention at scale. The system required approximately 40,000 manual server reboots and could not synchronize crew state automatically. American Airlines, running a different architecture, recovered the same day [3]. The result: 7,000+ flights canceled, 1.3 million passengers affected, an estimated $500M in recovery costs.
- Southwest Airlines (December 2022). Southwest’s operational failure produced a $140M DOT civil penalty, the largest ever assessed for consumer protection violations [4]. The cause was crew reassignment software that could not handle cascading volume during a weather event. 17,000 flights were canceled over 15 days. This is not the result of an external attack. It failed because its architecture could not execute the reassignment logic at the volume the event required. Elliott Management later cited the failure explicitly as an IT governance breakdown in its board overhaul campaign.
- Port of Seattle / Sea-Tac (August 2024). Rhysida ransomware entered Sea-Tac Airport through, in the Port’s own words, “primarily legacy systems used for employee, contractor and parking data” [5]. Baggage handling, check-in kiosks, and display boards went offline. Staff reverted to handwritten boarding passes. 90,000 individuals were affected; a $6M ransom was demanded. The entry point was not a sophisticated exploit against a hardened system. It was structural access through aging infrastructure.
In each case, the failure was not the external event but the software update, the weather, or the ransomware. It was the legacy stack’s inability to recover, segment, or document its state under stress.
The Agency Requiring Your Compliance Is Failing Its Own
The April 2026 DOT Office of Inspector General audit of the FAA’s 45 high-impact National Airspace System systems found 1,836 of 16,245 required security controls not fully implemented [6]. Fifteen of those 45 systems are still running NIST SP 800-53 Revision 4, the superseded standard. Every system supporting automation, communications, navigation, and weather had untracked vulnerabilities.
The GAO documented the same condition in September 2024: 51 of 138 air traffic control systems classified as unsustainable, with some modernization completions projected 10 to 13 years out.
The January 2023 NOTAM outage is the concrete proof. A corrupted database file in an aging FAA ATC system triggered the first nationwide ground stop since September 11, 2001. No external threat actor. No sophisticated intrusion. Data corruption in a system without adequate redundancy.
The executive instinct when a regulator’s own failures become public is to read that as enforcement slack. The data points the other direction. NIST SP 800-53 Rev 5 is the control framework against which TSA CIP assessments are evaluated.
The FAA’s Rev 4 gap is the same category of gap it will flag in carrier audits and an agency under Congressional scrutiny for its own infrastructure failures does not loosen its enforcement posture toward the carriers it regulates. It tightens it.
Why Network Monitoring Does Not Close the Audit Gap
TSA CIP assessments do not evaluate whether threats are being detected. They evaluate whether the evidence of compliant system behavior exists and can be produced on demand.
Network monitoring tools identify anomalous traffic at the perimeter. They do not make a VB6 system patchable. They do not generate the application-level event logs a CIP auditor requires. They do not produce the ground-to-aircraft interface inventory FAA AC 119-1A demands.
A SIEM deployed over a legacy stack produces perimeter visibility. It does not produce compliance documentation. The audit finding is written against the system, not the monitoring layer above it. Carriers that have invested in network monitoring and assume that investment closes their CIP exposure will discover the gap at the point of audit, not before it.
For carriers concerned about zero-downtime continuity during any remediation process, that question is addressed separately. The audit gap itself is not a continuity problem. It is a documentation and architecture problem, and monitoring tools are not designed to solve either.
The Stack You’re Running Is Now the Risk You Need to Quantify
Before any TSA CIP engagement or FAA ANSP revision process can proceed, three things need to be documented:
- Which systems interface with aircraft networks – the ANSP inventory requirement
- Which of those systems has no active vendor patch stream – the TSA 90-day patch gap
- Which systems produce no application-level event logs – the continuous monitoring gap
Most carriers cannot answer all three from existing documentation. That is the starting condition a structured assessment addresses.
The incident record shows what structural failure costs at an operational scale. And the April 2026 DOT OIG findings confirm that the agency responsible for setting the compliance standard is under pressure to demonstrate it can enforce one.
The immediate action is not a modernization program. It is a visibility exercise: a structured inventory of which systems interface with undocumented aircraft networks, and where the patch gap sits. That inventory is what any TSA CIP engagement or FAA ANSP revision process requires before anything else can proceed.
To understand the path forward once that picture exists, see our analysis of airline legacy system modernization.
If you cannot confirm which ground-interfacing systems have an active patch stream, that is the gap a TSA CIP assessment will find first. Legacyleap’s $0 Assessment maps it in 2 to 5 days: dependency graph, patch status, and interface inventory. No modernization work is required to start.
Book a Demo to see how Legacyleap executes structured modernization of the stacks named in this article (VB6, Classic ASP, Java EE, and EJB) within the governance and audit requirements aviation compliance now demands.
FAQs
TSA SD 1544.240 requires TSA-regulated airports and Part 121 air carriers to develop and maintain an approved Cybersecurity Implementation Plan covering four domains: network segmentation, patch management, continuous monitoring, and access control. The CIP must be submitted to TSA for approval and kept current. Operating without an approved CIP is explicitly listed as a sanctionable violation under TSA’s January 2025 Enforcement Sanction Guidance. Carriers must also maintain annual assessment cadences and document compensating controls wherever patch exceptions are declared.
Consequences under TSA’s January 2025 Enforcement Sanction Guidance scale from formal warning letters and compliance orders to civil monetary penalties and, in severe cases, certificate suspension or revocation. A failed audit does not trigger an immediate shutdown, but it starts a remediation clock under active TSA oversight. Every subsequent compliance step is monitored, and the documentation burden intensifies precisely when operational teams are least resourced to absorb it. Carriers with undocumented legacy systems enter that process without the system inventory the remediation requires.
FAA AC 119-1A governs the Aircraft Network Security Program requirement for OpSpec D301 carriers. An ANSP is a documented set of policies, procedures, and controls covering all IT systems that interface with aircraft networks, including ground support systems, maintenance platforms, and ACARS infrastructure. The 30-day revision obligation is the most operationally demanding aspect: every manufacturer security document update requires carriers to verify that all ground-interfacing systems remain consistent with the updated posture and revise the ANSP accordingly. That verification cannot be executed without a current, documented system inventory.
TSA SD 1544.240 requires a 90-day patch cycle for all Tier 1 and Tier 2 systems. That requirement assumes an active vendor patch stream. VB6, Classic ASP, and Java EE (pre-version 8) have no active vendor support and no patch stream. There is no patch to apply. The compliance gap is not a missed cycle but a permanent structural condition. No process improvement, monitoring overlay, or compensating control substitutes for patches that do not exist. CISA’s Known Exploited Vulnerabilities catalog confirms that CVEs from these stacks dating to 2007 remain actively weaponized.
Yes, where those systems interface with aircraft networks or ground support functions covered by RTCA DO-355A. The standard explicitly covers software loading systems, maintenance record platforms, and security log extraction from aircraft networks. An MRO system that interfaces with any of these functions falls within the DO-355A scope and, once the FAA’s pending NPRM finalizes, within binding airworthiness regulations. Carriers and MRO providers that treat maintenance software as outside the cybersecurity compliance perimeter are applying a scope interpretation the forthcoming rule does not support.
References
[1] TSA Security Directive SD 1544.240 and Emergency Amendment (March 2023) + TSA Enforcement Sanction Guidance (January 2025). https://www.tsa.gov/for-industry/surface-transportation-cybersecurity
[2] CISA Known Exploited Vulnerabilities (KEV) Catalog (2025). https://www.cisa.gov/known-exploited-vulnerabilities-catalog
[3] Delta Air Lines / CrowdStrike Incident (July 2024). https://www.transportation.gov/briefing-room/us-dot-statement-delta-air-lines-cancellations
[4] Southwest Airlines DOT Civil Penalty (December 2022 / Settlement 2023). https://www.transportation.gov/briefing-room/biden-harris-administration-fines-southwest-airlines-140-million-holiday-2022-meltdown
[5] Port of Seattle / Sea-Tac Rhysida Ransomware Attack (August 2024). https://www.portseattle.org/news/port-seattle-statement-cyber-security-incident
[6] DOT Office of Inspector General Audit Report (April 1, 2026). https://www.oig.dot.gov/library-item/43100