The Enforcement Window Is Already Open
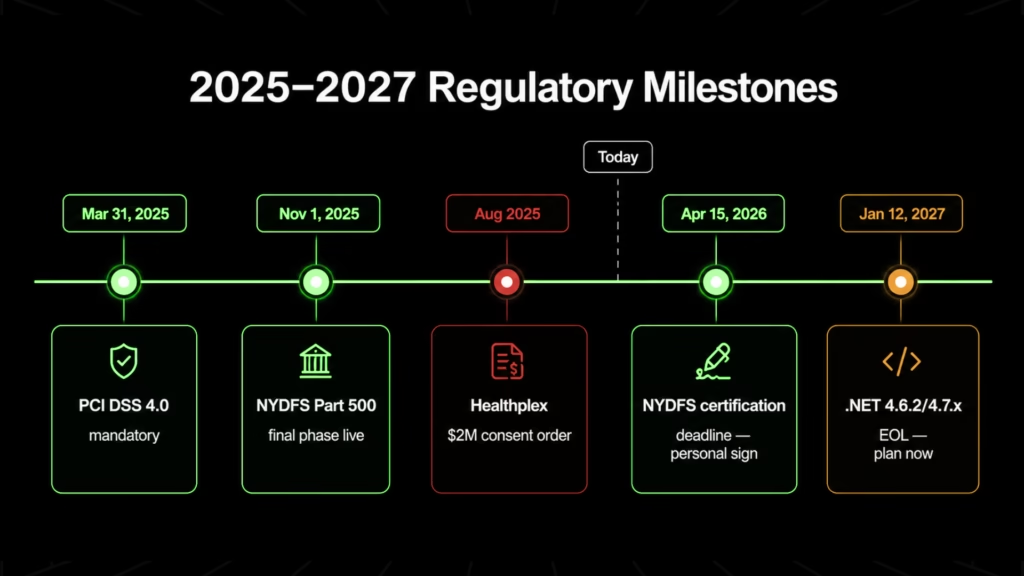
PCI DSS 4.0 became mandatory on March 31, 2025. NYDFS Part 500’s final phase went live November 1, 2025. The NYDFS annual certification, personally co-signed by the organization’s highest-ranking executive and CISO, is due April 15, 2026, for calendar year 2025 [2]. HHS OCR issued 10 HIPAA resolution agreements in the first five months of 2025, every one centered on failure to conduct an enterprise-wide risk analysis and act on known gaps [3]. These are not approaching deadlines. They are active enforcement conditions.
The financial context is not theoretical. The US average cost of a data breach reached $10.22M in 2025, the highest figure IBM has recorded [1]. That figure encompasses the regulatory penalties and emergency remediation costs that follow a compliance finding, with or without a breach.
In one illustrative scenario from the financial services sector, a legacy trading system EOL for four years failed regulatory audit logging requirements in late 2025. No breach occurred. The emergency modernization cost $6.7M over seven months. A compliance finding, in the right regulatory environment, can exceed the cost of the modernization that would have prevented it.
This is a risk brief for organizations with legacy systems already in production. It does not explain what legacy software is. It documents what regulators are finding when they examine it in 2026.
What Is Compliance Debt and Why It Starts at Vendor EOL
Compliance debt is the accumulated gap between what a system can currently do and what current regulations require it to do. Unlike technical debt, which is a trade-off developers accept for speed, compliance debt is a violation in waiting.
For legacy software, the clock starts at vendor EOL: the day patching stops is the day the gap between system capability and regulatory requirement becomes permanent.
Operational Stability Is Not a Compliance Standard
The most persistent executive misconception about legacy system risk is that a functioning system is a compliant one. It is not. The operative legal distinction: the moment a regulation mandates a control a system cannot produce, the organization is out of compliance. Not accumulating risk. Not operating in a gray area. Out of compliance. The transition moment is vendor EOL, not a breach, not an audit, not a regulatory notice.
Compliance debt is the accumulated gap between what a system can currently do and what current regulations require it to do. Unlike technical debt, which is a trade-off developers accept for speed, compliance debt is a violation in waiting. For legacy software, the clock starts at vendor EOL: the day patching stops is the day the gap between system capability and regulatory requirement becomes permanent.
HIPAA’s standard is “appropriate administrative, physical, and technical safeguards.” When a system no longer receives security updates, it no longer meets this standard. HHS has been explicit: legacy systems receive no compliance pass regardless of operational continuity. Under PCI DSS 4.0.1, Requirement 12.3.4 states that all hardware and software in the cardholder data environment must be vendor-supported. QSA commentary on record is unambiguous: “all means all” [5]. An EOL technology in scope is an automatic finding.
The evidentiary shift compounds this. Auditors are not asking, “Is your system secure?” They are asking, “Can you prove it was, at the time of the incident?” Operational stability does not answer that question.
PCI DSS 4.0 Automatic Findings Against Legacy Systems
No single legacy system in a regulated enterprise faces one compliance framework. Most face several simultaneously. The crosswalk below maps the 2026-active regulatory requirements that legacy systems architecturally cannot satisfy.
Mandatory since March 31, 2025. Three requirements create direct legacy findings:
- Req 6.3.3: Critical security patches applied within 30 days. A system that cannot receive patches produces no patch event log. The SLA is permanently unmet by architectural design, not organizational failure.
- Req 12.3.4: All software and hardware in the cardholder data environment must be vendor-supported. Any EOL technology in scope is an automatic finding. The QSA has no discretion [7].
- Req 8.4.3: MFA for all non-console CDE access. Applications built before SAML/OAuth2/OIDC cannot produce native application-layer MFA enforcement logs.
Penalty exposure: monthly fines of $5,000–$100,000; card network processing revocation for persistent non-compliance.
| PCI DSS 4.0.1 Requirement | What It Demands | Legacy System Failure Mode |
| Req 6.3.3 | Critical patches within 30 days | No patch pipeline exists; SLA permanently unmet |
| Req 12.3.4 | All assets vendor-supported | EOL technology = automatic finding |
| Req 8.4.3 | MFA for all non-console CDE access | Pre-SAML/OIDC applications cannot produce enforcement logs |
NYDFS Part 500: What Your Stack Must Now Prove
Final phase effective November 1, 2025. November 2025 NYDFS guidance clarified the universal MFA scope: legacy logins, direct application access, and API connections that circumvent SSO controls are explicitly non-compliant, not just remote access, not just external users [2].
The asset inventory requirement is equally direct. Every asset must carry a documented support expiration date. VB6, ColdFusion 2021, .NET Framework 4.5.2, and Windows 10 running past EOL each represent an enumerable finding in that inventory, not a risk flag requiring interpretation.
The certification due April 15, 2026, is personally co-signed by the highest-ranking executive and the CISO, attesting compliance for calendar year 2025. Enforcement is active: a $2M consent order was issued against Healthplex in August 2025. A January 2026 advisory from Ropes & Gray signals intensifying scrutiny and lower enforcement tolerance through the year.
The NYDFS April 15 certification is a personal attestation covering calendar year 2025, a year that has already closed. If legacy systems were in production at any point during 2025, the compliance gap is already on record.
Request a $0 Modernization Assessment, delivered in 2–5 days, before you sign a certification that covers a period you cannot go back and remediate.
HIPAA Enforcement Has Shifted From Gap Identification to Remediation
OCR’s 2026 enforcement posture has shifted from gap identification to gap remediation. The question is no longer “did you identify gaps?” It is “Did you act on them?” [3]
Tier 4 penalties for willful neglect uncorrected beyond 30 days reach up to $1.9M per violation category per calendar year. A legacy system with known, documented vulnerabilities and no available remediation path meets the willful neglect threshold.
The HHS proposed Security Rule update from January 2025, pending and not yet in force, signals the enforcement direction: encryption of all ePHI, biannual vulnerability scans, annual pen testing, full asset inventories, and mandatory MFA are all proposed to move from “addressable” to mandatory requirements. Treat this as a directional timeline, not a deferred obligation.
SEC Cybersecurity Disclosure Rules
Fully operational for all registrants. Three requirements create direct exposure for organizations running documented legacy stacks:
- Form 8-K: Material cybersecurity incidents must be disclosed within four business days of a materiality determination.
- Form 10-K: Boards must disclose active oversight of cybersecurity risks. Running known-EOL stacks with enumerable vulnerabilities is a documented, disclosable risk.
- Regulation S-P: 30-day customer breach notification, effective December 2025 for large entities.
Flagstar Bank settled with the SEC in December 2024 for a misleading cybersecurity Form 8-K. Disclosure accuracy is an active enforcement area.
SOX, GLBA, and the Convergence Effect
The regulatory picture compounds in financial services. The same legacy system in a regulated institution creates simultaneous findings under PCI DSS 4.0, NYDFS Part 500, SOX Section 404, and the GLBA Safeguards Rule. Each framework generates its own findings.
A financial institution running SQL Server 2008 in its reporting infrastructure faces simultaneous findings under SOX 404 audit log requirements, NYDFS Part 500 asset inventory mandates, PCI DSS 12.3.4, and the GLBA Safeguards Rule. That’s four deficiency letters from a single system.
This convergence is more acute at the industry level.
- Healthcare organizations face HIPAA enforcement alongside OCR’s 2026 remediation initiative.
- Financial institutions face PCI DSS, NYDFS, SOX, and GLBA simultaneously.
- Aviation and transportation organizations carry sector-specific mandates on top of this cross-industry baseline.
- Manufacturers and industrial OT operators face a widening compliance perimeter as IT/OT convergence creates new regulatory surfaces.
The structural legacy liability is the same across all of them; the penalty exposure multiplies.
Four Structural Failures That Compensating Controls Cannot Fix
Legacy systems fail compliance requirements for four specific reasons. Each is architectural. None can be resolved through policy overlays, identity proxies, or configuration changes. The section below documents what the failure looks like and why workarounds do not hold under forensic review.
Failure 1: No Patch Pipeline, No Patch Event Log
CISA added 245 new vulnerabilities to its Known Exploited Vulnerabilities catalog in 2025, 24 of them tied directly to active ransomware group exploitation. Cyber insurers now require patch event logs demonstrating CVE remediation within a 14-day SLA window for actively exploited vulnerabilities. Applications built on VB6, Classic ASP, legacy AngularJS, or EJB cannot produce these logs. Not because the organization failed to act, but because the vendor stopped issuing patches.
Three AngularJS 1.x CVEs were disclosed in late 2025 with no available patches: CVE-2025-59052 (CVSS 7.7), CVE-2025-66035 (CVSS 7.4), and CVE-2025-66412 (CVSS 7.1) [4].
Angular 19 and above received official patches. AngularJS 1.x received nothing. For any organization running AngularJS 1.x in a PCI or HIPAA environment, these are open vulnerabilities with no vendor remediation path available.
Failure 2: Absent Audit Log Capability
HIPAA requires audit log retention for six years. SOC 2 Type II requires 6–12 months of continuous, structured evidence. PCI DSS and NYDFS require structured log ingestion into a SIEM. Legacy applications frequently produce proprietary flat-file logs that SIEM platforms cannot ingest. Some produce no structured audit trail at all.
SOC 2 Type II certification is effectively unachievable for service providers whose core applications cannot produce the continuous, machine-readable evidence the observation window requires. The failure is not a negative audit result. It is the inability to submit required evidence, which is itself a distinct regulatory finding.
For a deeper analysis of how this gap affects coverage and claims, see our coverage of legacy system coverage under your cyber policy.
Failure 3: Native MFA Impossibility
Applications built before SAML, OAuth2, and OIDC cannot natively support modern MFA. The common workaround, an identity proxy or ZTNA gateway in front of the application, works at the operational layer but fails at the forensic layer.
In Travelers v. ICS (2022), forensic review found one server in a large estate without MFA. Travelers denied the entire claim [6]. For organizations with legacy systems in their authentication chain, this case established the operative insurance standard: partial MFA enforcement is treated as no MFA enforcement.
Cyber insurers are increasingly including EOL software clauses in renewal questionnaires, and claims tied to unpatched or unsupported systems are being denied on the same evidentiary basis.
NYDFS November 2025 guidance is equally explicit: a gateway log does not substitute for application-layer MFA enforcement records when a forensic examiner reviews the full authentication chain [2].
The gateway does not close the gap. It relocates it to a layer the examiner will reach.
Failure 4: Vendor EOL as Automatic Regulatory Finding
PCI DSS 4.0.1 Req 12.3.4 and NYDFS Part 500’s asset inventory requirement converge at one point: when the inventory shows EOL technology, the finding is already written. The assessor has no discretion. There is no remediation window within the audit itself. The organization must have already remediated or disclosed. This is the failure mode that cannot be compensated around, because the trigger is the inventory entry, not system behavior.
Which Legacy Stacks Produce Findings Today
The table below is not a risk inventory. Each row represents a finding an assessor can write today under currently enforced regulations. EOL is not a vendor advisory. It is a compliance event.
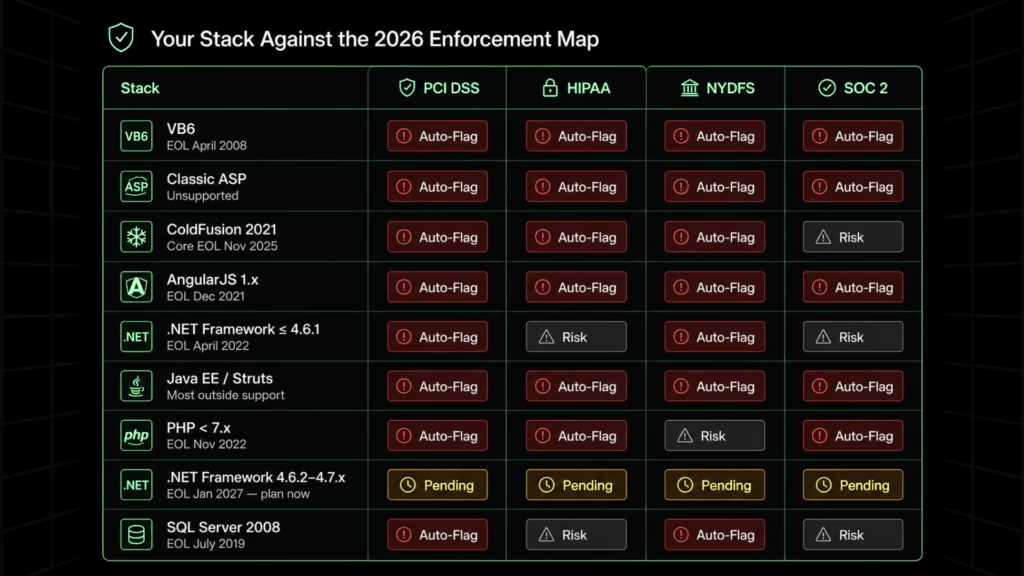
| Stack | EOL / Support Status | Primary Regulatory Finding |
| VB6 | EOL April 8, 2008 | HIPAA willful neglect risk; PCI DSS 12.3.4 automatic finding; NYDFS asset inventory flag; native MFA impossibility. See VB6 to .NET migration path |
| Classic ASP | Unsupported | Same as VB6; additionally cannot support TLS 1.2+ natively without code-level modification, creating a direct encryption mandate failure under HIPAA and PCI DSS |
| ColdFusion 2021 | Core EOL November 10, 2025; extended support to November 2026 provides no security patches | PCI DSS 12.3.4 finding; HIPAA safeguard gap; NYDFS inventory flag |
| AngularJS 1.x | EOL December 31, 2021 | SOC 2, PCI DSS, HIPAA, FedRAMP audit finding; 3 unpatched CVEs from late 2025 (CVSS 7.1–7.7). See AngularJS migration path |
| .NET Framework ≤4.6.1 | EOL April 26, 2022 | PCI DSS 12.3.4 automatic finding; NYDFS inventory flag; cannot support modern authentication natively. See .NET Framework modernization |
| .NET Framework 4.6.2/4.7.x | EOL January 12, 2027 | Active planning window; becomes a PCI DSS and NYDFS automatic finding in under two years |
| Windows 10 | EOL October 14, 2025 | PCI DSS 12.3.4 finding; HIPAA safeguard violation; NYDFS inventory flag. Healthcare migration rate at EOL: 41%. Finance: under 45% |
| Java EE / EJB 2–3 / Struts | Oracle/Jakarta varies; most enterprise deployments outside official support | PCI DSS 12.3.4 finding; cannot support modern authentication; multi-framework audit finding |
| Delphi (pre-10.3 versions) | Versions through 10.2 Tokyo confirmed outside Embarcadero’s supported versions list | HIPAA safeguard gap; PCI DSS 12.3.4 finding; NYDFS asset inventory flag. Common in manufacturing, logistics, and operations-critical applications. See Delphi legacy modernization |
| PHP ≤7.x | PHP 7.4 EOL November 28, 2022 | Direct compliance violation under PCI DSS, HIPAA, and SOC 2 |
| SQL Server 2008 and legacy SSIS | SQL Server 2008 EOL July 9, 2019 | SOX audit log and change management gaps; GLBA Safeguards data security gaps; NYDFS data lineage requirements |
ColdFusion 2021 clarification: Adobe’s extended support runs through November 2026, but it provides no security patches, only migration assistance. For compliance purposes, an organization running CF2021 on extended support is unpatched. PCI DSS 12.3.4 and HIPAA safeguard findings apply in full.
On .NET Framework 4.6.2/4.7.x: The January 12, 2027, EOL date is not a safety buffer. It is the deadline. Organizations on these versions have an active planning window, not a deferral window.
Can Executives Be Personally Liable for Legacy System Compliance Failures
Yes, under three active frameworks.
- NYDFS Part 500 requires personal co-signatures from the highest-ranking executive and CISO on annual compliance certifications.
- SEC cybersecurity disclosure rules require boards to attest to active oversight of documented risks.
- The 2022 Uber CISO conviction established that concealing known security gaps carries criminal exposure, not just civil penalties.
The NYDFS Part 500 annual certification due April 15, 2026 is not a form filed by a compliance department. It is a personal attestation, co-signed by the organization’s highest-ranking executive and CISO, affirming compliance for calendar year 2025.
That year has already closed. Legacy gaps that existed during 2025 must either be disclosed as non-compliance or attested as compliant.
The personal exposure breaks down into three categories:
- False attestation. Knowingly signing the certification while aware of undisclosed compliance gaps creates direct personal liability for both signatories. The risk is not running a legacy system. The risk is attesting that one does not exist.
- SEC disclosure obligations. Under Form 10-K, boards must demonstrate active oversight of cybersecurity risks. Running documented EOL stacks with known vulnerabilities is a disclosable risk. Flagstar Bank’s December 2024 settlement with the SEC for a misleading cybersecurity Form 8-K established that disclosure accuracy is an active enforcement area.
- The Uber CISO precedent. Joe Sullivan was convicted in 2022 of obstruction of justice for concealing a known breach, the first criminal conviction of a security executive. The conviction was for concealment, not for running legacy systems. What it established is that personal accountability for security leaders is not theoretical. Executives who actively conceal known risks face criminal exposure, not just civil penalties.
The clearest personal exposure exists for executives who falsely certify compliance, actively conceal known risks, or fail to document that known gaps were escalated and that remediation decisions were made above their level. Running a legacy system is not itself the liability. Not disclosing it is.
Mapping Exposure to Architecture
The four structural failures share a common root: the system cannot be patched, cannot produce required evidence, and cannot natively support the authentication standards regulators now treat as baseline requirements. Policy overlays address surface symptoms. The gap regulators are measuring in 2026 is architectural.
Before any modernization commitment, the necessary first step is an accurate map of what the exposure actually is.
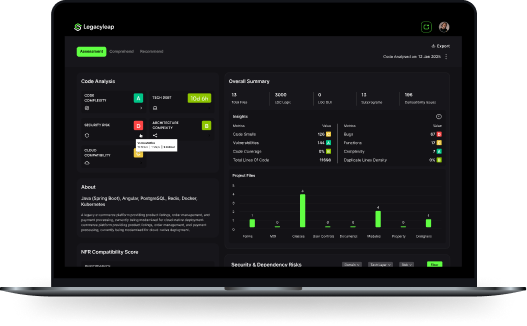
Legacyleap’s Assessment Agent produces exactly that: which stacks are running, their EOL status, where MFA gaps exist in the authentication chain, and where audit log production fails against current regulatory requirements.
The Documentation Agent reconstructs undocumented system behavior so the picture is complete. This is delivered as a $0 Modernization Assessment in 2–5 days, without requiring any commitment to modernization.
For organizations under HIPAA, NYDFS, or GLBA scrutiny, this is the finding before the fix. For HIPAA-regulated application modernization, the Assessment is typically the first deliverable before any transformation scope is defined.
Where modernization is the path forward, Legacyleap’s Security Modernization track addresses each structural failure directly.
- Authentication chain repair closes Failure 3.
- Migration to a vendor-supported stack closes Failure 1.
- Structured audit log capability in the modernized architecture closes Failure 2.
- Vendor-supported targets close Failure 4.
The supported legacy stacks map directly to the exposure table above: VB6, Classic ASP, .NET Framework, AngularJS, Java EE/EJB/Struts, and Delphi. Modern targets include .NET 6+/8, ASP.NET Core, Spring Boot, Angular, and React.
For regulated industries where source code in a Gen AI platform is itself a compliance consideration, Legacyleap deploys in VPC or on-premises environments with no outbound API calls and no code leaving client infrastructure.
This deployment model is designed specifically for HIPAA, NYDFS, and GLBA requirements. For organizations assessing modernization without a production outage, the phased delivery model preserves operational continuity throughout.
The Compliance Gap Is Already Open
PCI DSS 4.0 is mandatory. NYDFS Part 500 certification is due for a year that has already closed. OCR is pursuing remediation failures, not gap identification. The four structural failures that make legacy systems non-compliant cannot be resolved with compensating controls. The accountability line runs to the executive suite.
The first step is not a modernization commitment. It is an exposure map.
The four structural failures documented here cannot be fixed with compensating controls, policy overlays, or identity proxies. The April 15 certification is a personal attestation. Signing it without an accurate exposure map is the documented risk.
Request the $0 Modernization Assessment and know exactly what you are attesting to before the deadline. No modernization commitment required.
Book a Demo: See the assessment workflow and platform architecture before committing.
FAQs
Under PCI DSS 4.0.1 Req 12.3.4, the finding is categorical: the assessed component is vendor-unsupported and therefore non-compliant. The QSA documents the specific system, its EOL date, and the requirement it violates. There is no qualitative judgment about risk level or exploitability. The deficiency exists by definition. The organization receives a non-compliant finding on its Report on Compliance, which affects card brand standing, acquirer relationships, and any contractual compliance attestations the organization has made to partners or customers.
Disclosure means reporting the gap as a non-compliance item in the annual certification, which triggers a defined remediation timeline and regulatory engagement. Concealment means signing the certification as compliant while knowingly omitting the gap, which converts a compliance deficiency into a false attestation. The legal exposure shifts materially: a disclosed gap creates remediation obligations; a concealed one creates personal liability for the signatories. NYDFS enforcement treats the two differently, and the distinction matters for how the organization’s board and legal counsel should frame the decision before April 15.
If the certification attests full compliance and legacy systems were running during 2025 with documented gaps, the organization has submitted a false attestation. NYDFS can pursue enforcement action against the organization and, under Part 500’s personal co-signature requirement, against the individual signatories. The Healthplex $2M consent order from August 2025 illustrates that NYDFS enforcement at the final phase is financially material. An organization that identifies a gap before signing has the option to self-report, which carries a different enforcement outcome than a false attestation discovered during examination.
Under HIPAA, willful neglect is defined as conscious, intentional failure to comply or reckless indifference to the requirement. OCR’s penalty structure places willful neglect corrected within 30 days at a lower tier than willful neglect left uncorrected beyond 30 days. The latter carries penalties up to $1.9M per violation category per calendar year. The practical implication: once a vulnerability is documented and no remediation path exists on an EOL system, the 30-day clock begins. Documentation of the gap without action is the evidentiary basis OCR uses to establish willfulness.
SOC 2 Type II requires continuous, structured evidence of control operation across a 6–12 month observation window. Specifically: timestamped access logs, change management records, authentication event trails, and incident response documentation, all in machine-readable formats that can be reviewed against stated control objectives. Legacy applications typically produce proprietary flat-file logs, incomplete event trails, or no structured output at all. The failure is not a weak control posture. It is the absence of the evidence format the auditor requires, which means the observation window cannot be satisfied regardless of how the underlying controls are described in policy documentation.
References
[1] IBM Security, Cost of a Data Breach Report 2025. https://www.ibm.com/reports/data-breach
[2] New York Department of Financial Services, 23 NYCRR Part 500 — Cybersecurity Requirements for Financial Services Companies (final phase effective November 1, 2025); NYDFS MFA Guidance, November 2025. https://www.dfs.ny.gov/industry_guidance/cybersecurity
[3] U.S. Department of Health and Human Services, Office for Civil Rights, 2025 HIPAA Enforcement Activity. https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/agreements/index.html
[4] HeroDevs Security Research, AngularJS 1.x CVE Analysis, Late 2025 (CVE-2025-59052, CVE-2025-66035, CVE-2025-66412). https://www.herodevs.com/support/angularjs-eol-support
[5] Auditwerx, QSA Commentary on PCI DSS 4.0.1 Requirement 12.3.4. https://www.auditwerx.com/pci-dss-4-0-1/
[6] Coalition, 2024 Cyber Claims Report. https://www.coalitioninc.com/reports/cyber-claims
[7] PCI Security Standards Council, PCI DSS v4.0.1, Requirements 6.3.3, 8.4.3, 12.3.4. https://www.pcisecuritystandards.org/document_library/