Why 2026 Is the Forced Decision Point for Every ColdFusion Deployment
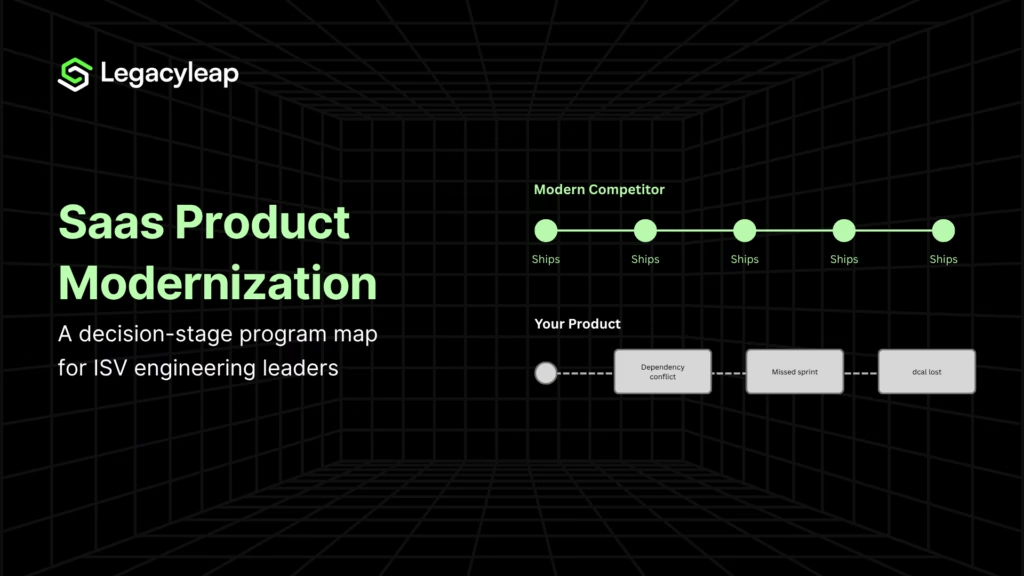
ColdFusion modernization is no longer a future-state planning exercise for most enterprise deployments. Most have been deferring the decision for years.
In 2026, four pressure vectors have converged in a way that makes further deferral untenable as a specific, verifiable condition for most production ColdFusion environments.
End of Life
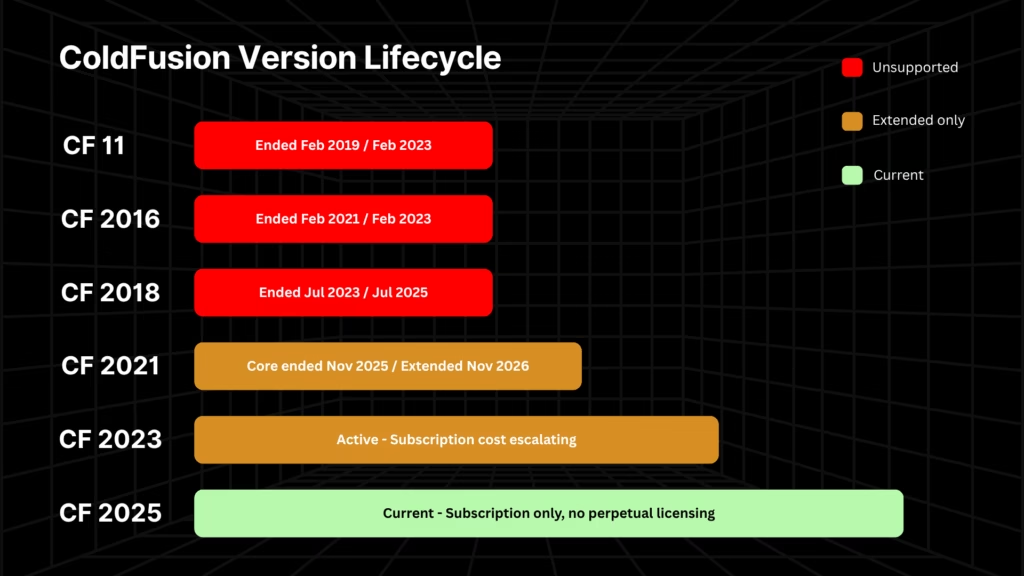
CF 2021 core support ended November 10, 2025. Adobe’s extended support through November 2026 covers migration assistance only. No security patches, no hotfixes. Organizations treating extended support as continued security coverage are operating on a false assumption.
The table below is the authoritative version-by-version EOL reference, sourced from Adobe’s official product lifecycle documentation [1].
| ColdFusion Version | Core Support End | Extended Support End | Risk Level |
| CF 11 | February 2019 | February 2023 | Critical. Fully unsupported |
| CF 2016 | February 2021 | February 2023 | Critical. Fully unsupported |
| CF 2018 | July 2023 | July 2025 | Criticalully u. Fnsupported |
| CF 2021 | November 10, 2025 | November 2026 | High. Security patches ended |
| CF 2023 | TBD (~2026) | TBD (~2028) | Moderate. Active but costly to maintain |
| CF 2025 | TBD | TBD | Current version. Subscription-only |
Subscription Pricing
CF 2025 eliminates perpetual licensing entirely for the first time in ColdFusion’s history.
- Standard tier: $760/year per server.
- Enterprise tier: $2,930/year per server [2].
A four-server Enterprise cluster that previously required a one-time capital expenditure of approximately $38,000 now costs $11,720 annually with no asset ownership at the end. Software deactivates if the subscription lapses.
Staying on an older version indefinitely is no longer a viable strategy. CF 2025 forces the version decision while permanently converting the cost model from capital expenditure to operating expenditure with no perpetual fallback.
Active Security Exploitation
CVE-2024-20767 was added to CISA’s Known Exploited Vulnerabilities catalog in December 2024, confirmed as actively exploited in the wild [3]. CVE-2023-26360 was used to breach a federal civilian executive branch agency in 2023. Organizations on CF 2023 have managed approximately 18 security updates since July 2023.
One operational exposure is less widely understood: Adobe requires a corresponding JDK update alongside every ColdFusion security patch [4]. Applying the CF patch alone does not fully secure the server. Organizations whose patching processes stop at the CF layer are exposed even on actively maintained versions.
Developer Scarcity
Senior ColdFusion developers command $110,000–$140,000+ annually or $60–$120/hour at contract rates. The talent pipeline is effectively closed, with no meaningful volume of new CF developers is entering the market.
The compensation cost is the visible problem. The structural problem is what happens when those developers leave: the application continues to run, but the understanding of what it actually does leaves with them.
Business logic embedded in undocumented .cfm files has no other record. This is the condition that makes the mounting technical debt in ColdFusion codebases categorically more dangerous than in documented, tested systems. It is also what makes comprehension the mandatory first step of any ColdFusion modernization program.
Is ColdFusion Dead?
ColdFusion is not dead. Adobe ColdFusion 2025 is an active, commercially supported product with a current release cycle, and it still runs in production across a significant share of Fortune 500 companies, government agencies, and healthcare systems.
The product is not going away. What has changed is the cost structure, the security posture of older versions, and the talent pipeline.
The operative question for enterprise leaders is not whether ColdFusion exists. It is whether continuing to run their specific deployment is strategically defensible given its EOL status, security exposure, and integration dependencies.
For most deployments on CF 2021 or earlier, that question has a clear answer.
What Is the Latest Version of ColdFusion?
Adobe ColdFusion 2025 is the current release, available exclusively on a subscription model at $760 per server per year (Standard) or $2,930 per server per year (Enterprise).
Perpetual licensing has been discontinued across all versions. Software deactivates if the subscription lapses, which means staying on an older version indefinitely is no longer a viable fallback strategy.
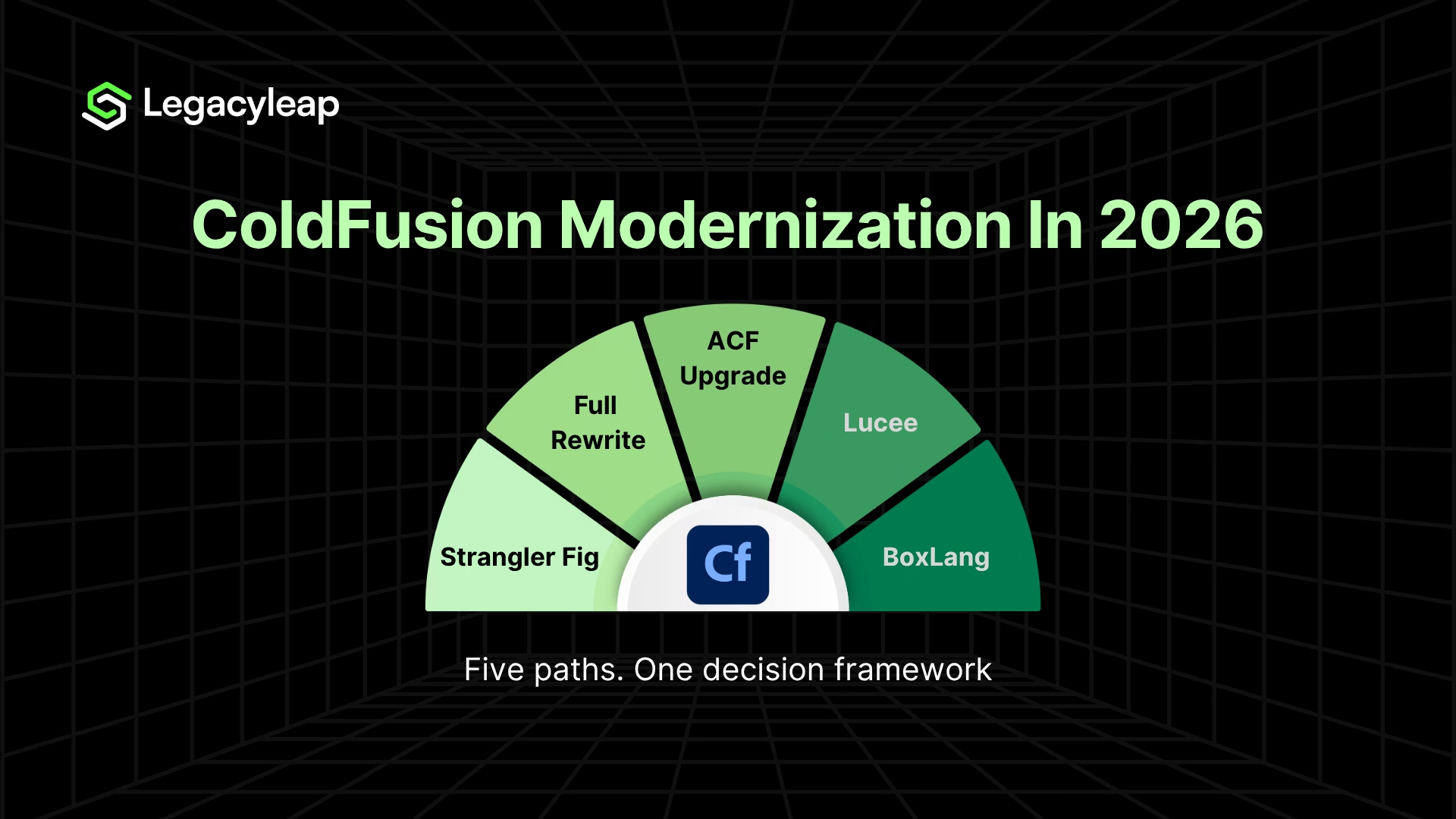
The Five ColdFusion Modernization Paths: Costs, Timelines, and Real Trade-offs
All five available paths are presented below with their honest trade-off profiles, including the failure modes that each path creates when applied to the wrong deployment.
What Are the Alternatives to Adobe ColdFusion?
Five paths exist:
- ACF version upgrade to CF 2025,
- Migration to Lucee,
- Adoption of BoxLang,
- Incremental replatforming via the Strangler Fig pattern, and
- Full application rewrite to a modern target stack.
The right choice depends on codebase size, documentation state, team capability, and regulatory environment, each assessed in the decision framework that follows this section.
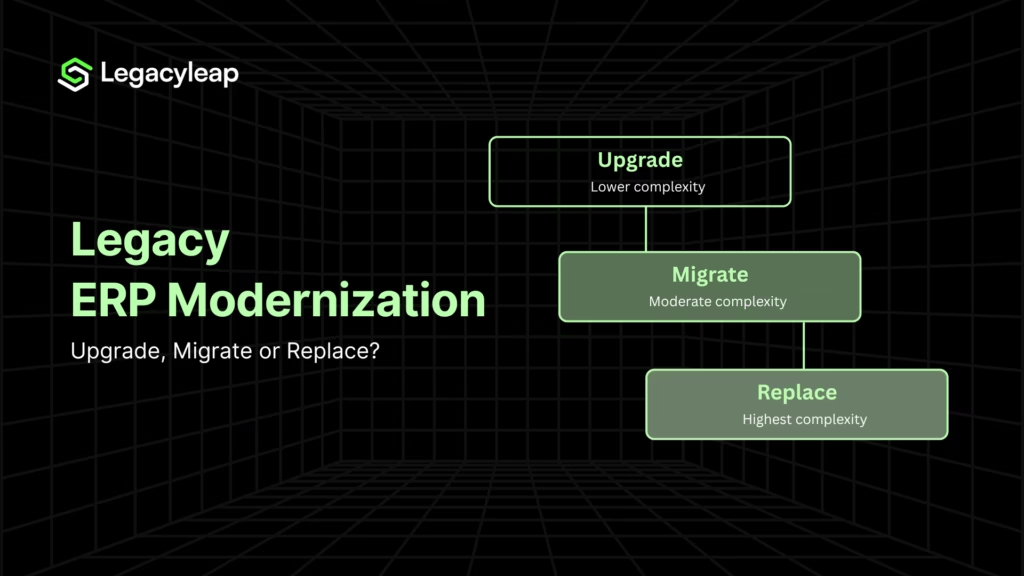
Path Comparison
| Path | Best-Fit Conditions | Timeline | Cost Range | Key Risk | Reversibility |
| Path 1 — ACF Upgrade (→ CF 2025) | Small-to-medium apps; regulated industries where Adobe’s FedRAMP/HIPAA/PCI certifications are embedded in audit frameworks | 2–8 weeks | $15K–$75K+ migration | Breaking changes compound across version hops; permanent subscription lock-in with no perpetual exit | Low — another migration required to exit Adobe CF |
| Path 2 — Switch to Lucee | Cost reduction and containerisation goals; no proprietary ACF dependencies (CFX tags, PDF generation, spreadsheet functions) | 2–12 weeks per app | $0 licensing; migration effort varies | Does not address codebase maintainability — the same undocumented logic runs on a different engine | Moderate |
| Path 3 — Adopt BoxLang | Teams already on the ColdBox ecosystem; cloud-native targets; lower regulatory burden | Fastest for ColdBox shops | $0 (Apache 2.0); BoxLang+ commercial tier for enterprise support | Early-stage enterprise adoption; limited production evidence at regulated scale | Moderate |
| Path 4 — Incremental Replatforming (Strangler Fig) | Large enterprise applications; business continuity required during migration; 200K+ LOC systems | 3–24 months | $100K–$500K | Proxy layer and parallel infrastructure complexity; seam injection required before migration begins | High — phased and reversible at each stage |
| Path 5 — Full Application Rewrite | Documented systems with a strong target-stack team in place; codebases below 100K LOC that are genuinely greenfield-ready | 12–36 months | $500K–$2M+ | Business logic loss on undocumented systems; chronic overrun at 100K+ LOC | Low — no rollback once the legacy system is decommissioned |
Path 1: ACF Version Upgrade (→ CF 2025)
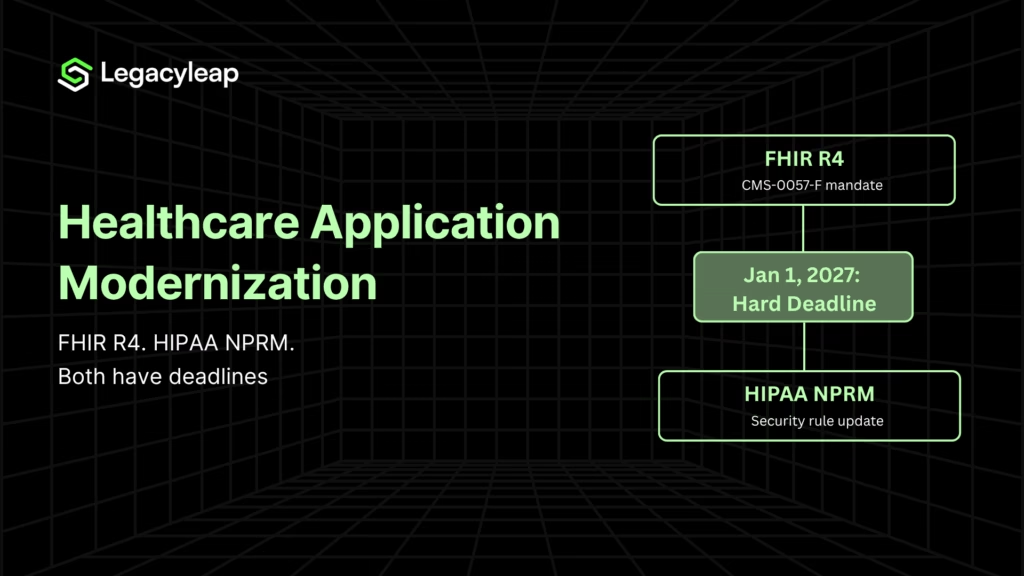
The upgrade path preserves Adobe’s compliance certification history, relevant in FedRAMP, HIPAA, and PCI environments where that certification is embedded in audit frameworks, not just referenced.
The risk is that each version hop introduces breaking changes, and CF 2021 → CF 2023 → CF 2025 is not a linear progression. Beyond the migration cost, the subscription model permanently removes perpetual licensing as a fallback.
An organization that upgrades to CF 2025 today is locked into Adobe’s subscription model until they execute another migration to exit the platform entirely.
Path 2: Switch to Lucee
Lucee is an open-source CFML engine with no licensing cost and workable CFML compatibility for applications free of proprietary ACF features. It addresses the subscription cost problem and improves containerisation options.
What it does not address is the application. Migrating to Lucee and treating the project as complete trades one cost exposure for a different structural risk: the same undocumented, untested codebase now runs on a different engine.
Lucee is a cost reduction lever. It is not a modernization strategy. Compatibility gaps, such as CFX tags, PDF generation, or spreadsheet functions, require a pre-migration assessment before committing.
Path 3: Adopt BoxLang
BoxLang, developed by Ortus Solutions, is an Apache 2.0 open-source JVM language with a CFML compatibility module (per Ortus Solutions’ published documentation). For teams already invested in the ColdBox ecosystem, it provides the fastest transition path with genuine cloud-native architecture options and a commercial support tier via BoxLang+.
The constraint is enterprise adoption maturity because production evidence at a regulated scale is limited. Appropriate for forward-leaning teams with lower compliance burden and existing ColdBox investment, but not the recommended path for large regulated deployments without a clear adoption track record at comparable scale.
BoxLang is developed by the same team behind the ColdBox MVC framework, already in production use across a significant share of enterprise ColdFusion deployments. The BoxLang+ commercial tier provides the enterprise support structure that open-source adoption at regulated scale typically requires.
For organizations already running ColdBox, the transition overhead is lower than any other non-CFML path.
Path 4: Incremental Replatforming (Strangler Fig)
For large enterprise applications, incremental replatforming via the Strangler Fig pattern is the only approach that maintains business continuity while managing migration risk at scale.
Components are replaced behind a proxy layer while the legacy system and modernized services coexist, limiting blast radius at each stage and allowing validation before the next module moves.
The cost range ($100K–$500K) exceeds a version upgrade but the risk profile is substantially lower than a big-bang rewrite.
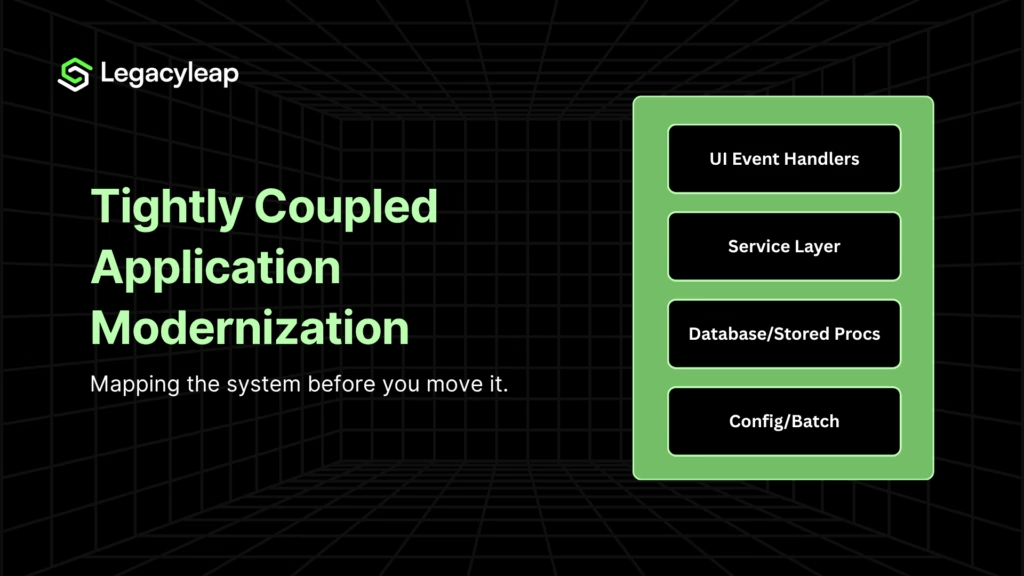
A phased, incremental modernization approach of this kind requires seam injection into the ColdFusion codebase before migration begins, which in turn requires a comprehension pass. The Strangler Fig pattern provides the structural mechanism for decoupling tightly coupled ColdFusion monoliths, but the business logic inside those modules still needs to be documented before they can be safely extracted.
Target stacks: Spring Boot for Java-capable teams, and ASP.NET Core for .NET shops. For modernizing the frontend while preserving ColdFusion backend logic, frontend decoupling toward React or Angular is typically handled as a parallel track within the same program.
Path 5: Full Application Rewrite
A full rewrite is defensible under one set of conditions: documented business logic, a strong target-stack team already in place, and a codebase below 100K LOC that is genuinely greenfield-ready. Outside those conditions, it is the highest-risk path available.
The failure mode is not technical complexity. It is business logic loss. CFML’s procedural structure embeds business rules directly in .cfm files, often without any external record.
A rewrite team working without a comprehension baseline will produce a system that compiles and passes smoke tests, then silently mishandles edge cases in production, because the rules governing those cases were never surfaced before transformation began.
At 500K+ LOC, a big-bang rewrite on an undocumented system is not an aggressive strategy. It is a program-ending risk.
How Much Does ColdFusion Modernization Cost?
The cost of modernizing a ColdFusion application depends entirely on path and codebase complexity. These are realistic ranges based on comparable enterprise engagements:
| Modernization Path | Typical Cost Range |
| ACF version upgrade to CF 2025 | $15,000–$75,000+ one-time, then $760–$2,930 per server per year with no perpetual exit |
| Switch to Lucee | $0 licensing; migration effort varies by codebase size and ACF dependency depth |
| Adopt BoxLang | $0 (Apache 2.0); BoxLang+ commercial tier for enterprise support |
| Incremental replatforming (Strangler Fig) | $100,000–$500,000 |
| Full application rewrite | $500,000–$2,000,000+; undocumented systems above 100K LOC routinely exceed the high end |
The cost gap between incremental replatforming and a full rewrite is not primarily a technology cost. It is a documentation cost. On an undocumented system, the rewrite team must first discover what the application does before they can rebuild it.
That discovery phase, when unplanned, is where full rewrite budgets collapse.
How Long Does a ColdFusion Migration Take?
Migration timelines vary by path and codebase size.
- ACF version upgrades run two to eight weeks for small-to-medium applications.
- A Lucee switch runs two to twelve weeks per application, depending on proprietary ACF dependency depth.
- Incremental replatforming runs three to twenty-four months for large enterprise systems.
- Full application rewrites run twelve to thirty-six months, and that range assumes an adequate documentation baseline exists before transformation begins.
The timeline variable most consistently underestimated across ColdFusion programs is the comprehension phase: the time required to extract, document, and verify business logic before any transformation begins.
On undocumented systems, this phase is not optional. Skipping it does not shorten the timeline. It relocates the cost to post-cutover production failures, which are significantly more expensive to resolve.
How to Choose the Right ColdFusion Modernization Path: A Decision Framework
Path selection is not a judgment call but an output of four enterprise-specific variables. The same deployment characteristics that make Path 4 the only defensible choice for a 400K LOC undocumented system make Path 1 the correct answer for a small, compliance-bound application on a documented stack.
Variable 1: Codebase Size and Complexity
| Codebase Size | Path Implications |
| Sub-50K LOC | Most paths are viable. Rewrite risk is manageable with proper documentation in place. ACF upgrade or Lucee are reasonable cost levers at this scale. |
| 100K–500K LOC | Big-bang rewrite is no longer a safe option. Overrun risk compounds with scale. Incremental replatforming or a comprehension-first rewrite with a validated documentation baseline is required. |
| 500K+ LOC | Incremental replatforming via Strangler Fig is the only defensible approach. A 500K+ LOC rewrite on an undocumented system that surfaces a business logic failure in production is a program-ending event. |
LOC alone is an incomplete signal. A 200K LOC application with clear module boundaries is materially different from a 200K LOC application where business rules are distributed across template files with no separation of concerns.
Fitment scoring, which is a structured complexity assessment produced before path commitment, is the correct precursor to path selection at this scale.
Variable 2: Documentation State
Documentation state is the highest-impact variable in ColdFusion modernization planning. More program failures trace to this variable than to any other.
Documented systems like those with current system maps, API contracts, and accessible business logic records can move into assessment and transformation with confidence. The engineering team knows what it is modernizing.
Zero-documentation systems face a different problem. If the original developers are unavailable and no records exist of business logic, workflows, or API contracts, the organization does not yet know what it is modernizing.
Transformation without comprehension produces systems that behave correctly under test conditions derived from the new code, and fail in production on the edge cases that only existed in the legacy implementation.
Comprehension and documentation must precede transformation, without exception, for any system where the original implementation intent cannot be independently verified. This step is the most commonly skipped in ColdFusion programs and the most expensive to skip.
It is also what makes automated test generation possible: the documentation becomes the specification against which test cases are generated before a single line of legacy code is transformed.
The same principle extends to the data layer. For modernizing legacy databases tied to ColdFusion applications, schema dependencies and stored procedure logic require the same comprehension pass before migration can proceed safely.
For a deeper understanding of how Gen AI solves the comprehension problem, read here: How To Achieve Full Legacy System Comprehension with Gen AI.
Variable 3: Team Capability
| Team Profile | Recommended Path |
| CF-native, no modern stack capability | Spring Boot is the natural target for Path 4 or Path 5; it preserves JVM familiarity |
| Java-capable engineering team | An external modernization platform required regardless of path; the comprehension phase cannot be performed without CF knowledge |
| .NET-capable engineering team | ASP.NET Core is the natural target; ColdFusion to .NET is a well-established migration path |
| No internal CF expertise | Incremental replatforming is feasible with internal resources; the comprehension phase still requires CF expertise |
| Mixed stack (CF + Java or .NET) | Incremental replatforming is feasible with internal resources; comprehension phase still requires CF expertise |
Team capability also determines realistic timeline. A Java-capable team executing a Spring Boot replatforming delivers on a measurably different schedule than a team ramping on both the legacy stack and the target stack simultaneously.
Variable 4: Regulatory Environment
Regulatory environment affects two distinct decisions: which path carries the lowest compliance disruption, and how AI-assisted modernization must be deployed.
- On compliance continuity: organizations in FedRAMP, HIPAA, or PCI environments where Adobe’s certification history is embedded in audit frameworks should treat an ACF version upgrade as the lowest-disruption path. Switching to Lucee or BoxLang introduces re-certification exposure that can materially exceed the cost of staying on ACF.
- On AI governance: the full treatment of what AI governance policies mean for deployment architecture, and why they are a constraint on how modernization is executed rather than whether it can be, is covered in the AI acceleration section below.
Which Profile Fits Your Deployment?
| Profile | Conditions | Recommended Path |
| Profile 1: Small regulated application | Sub-50K LOC, documented, FedRAMP/HIPAA/PCI environment, CF-native team | Path 1. Lowest disruption; compliance continuity preserved within Adobe’s certification framework. |
| Profile 2: Medium application, cost-sensitive | 50K–150K LOC, moderate documentation, no proprietary ACF dependencies, limited compliance constraints | Path 2 (Lucee) for immediate cost relief, paired with a structured roadmap toward the target stack. Lucee is not the final destination — treat it as a staging position. |
| Profile 3: Modern team, ColdBox-invested | Below 200K LOC, ColdBox ecosystem in use, lower regulatory burden, forward-leaning engineering leadership | Path 3 (BoxLang). Fastest transition for this profile; confirm production readiness at your scale before committing. |
| Profile 4: Large enterprise, documented | 200K–500K LOC, adequate documentation, Java or .NET-capable team, business continuity required | Path 4 (Incremental Replatforming). Building a structured modernization roadmap before committing to a target sequence is strongly recommended at this scale. |
| Profile 5: Large enterprise, undocumented | 200K+ LOC, zero or near-zero documentation, original developers unavailable | Path 4, preceded by a mandatory comprehension and documentation phase. Transformation cannot begin until the documentation baseline is established. Path 5 is not viable in this configuration. |
| Profile 6: Regulated, strict AI governance | Any size above 100K LOC, code cannot leave client infrastructure, regulated industry | Path 4 or Path 5 with on-premise or VPC-deployed LLM execution. AI governance policy governs deployment architecture; it does not determine path viability. Confirm the platform supports air-gapped execution and audit logging before engaging. |
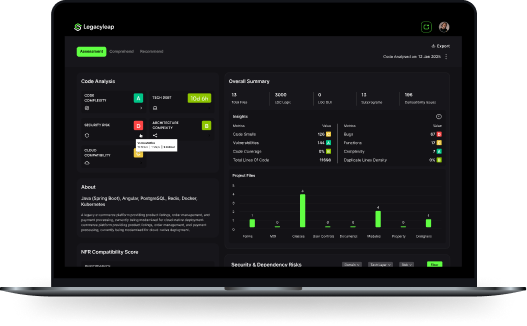
Before committing to a path, Legacyleap’s $0 Modernization Assessment maps your codebase, identifies your documentation gaps, and produces a path recommendation structured for a budget or vendor conversation. No engagement required and no cost.
ColdFusion to Java Migration: What It Takes
Java via Spring Boot is the most natural cross-platform migration target for ColdFusion applications.
The JVM commonality reduces the platform learning curve for teams already operating on the Java stack, and Spring Boot’s component model maps reasonably well to ColdFusion’s template-based architecture once business logic is extracted from .cfm files.
What the migration requires is a full comprehension pass to extract business logic before transformation begins, a clear module boundary map to determine phasing sequence, and a Java-capable engineering team on the receiving end.
ColdFusion’s procedural structure does not translate cleanly to Spring Boot’s component model without an intermediate architecture step. Teams that attempt a direct CFML-to-Java translation without that step produce Java code that inherits the structural problems of the original CFML.
Timeline for a documented system below 100K LOC with a Java-capable team: six to eighteen months using an incremental replatforming approach. Undocumented systems require a comprehension phase before that timeline starts.
ColdFusion to .NET Core Migration: What It Takes
ASP.NET Core is the preferred target for organizations with .NET-capable engineering teams, and ColdFusion to .NET is a well-established migration path with documented patterns.
The migration logic is structurally similar to the Java path.
- Business logic must be extracted from .cfm files and documented before transformation begins,
- Module boundaries must be defined before phasing can be planned, and
- The target team must have genuine ASP.NET Core capability rather than general .NET familiarity.
One practical advantage of the .NET path for regulated US enterprises is that ASP.NET Core’s compliance certification history in FedRAMP and HIPAA environments is mature, which reduces re-certification friction compared to moving to a newer runtime.
For organizations in financial services, defense, or federal civilian environments, this is a material factor in path selection.
Timeline and cost structure are comparable to the Java path. The determining variable is team composition, not the target stack.
How AI Accelerates ColdFusion Modernization
Every ColdFusion modernization program eventually confronts the same structural problem:
- The application has accumulated years of undocumented business logic written by developers who are no longer available, and
- No external record of what it does exists.
Static analysis tools surface dependency graphs and code quality issues. They do not surface business rule intent embedded in procedural .cfm files.
AI-assisted modernization changes this in three specific ways.
- Automated comprehension. AI agents can extract business logic, API contracts, workflow dependencies, and inter-module relationships directly from undocumented CFML source code without access to the original developers. The output is a structured documentation baseline that makes transformation safe to begin.
- Automated test generation. Once the documentation baseline exists, AI agents generate unit tests, integration tests, and API test suites from the documented specification rather than from the legacy code. This is the operative distinction. The test suite validates the behavior that the documentation says the system should produce, not the behavior inferred from code that may itself contain errors.
- Governed transformation. AI-assisted code transformation with diff-based human review at every step produces a reviewable, auditable migration record. Every change is surfaced for engineering sign-off before acceptance. No module advances without explicit approval.
For organizations with strict AI governance policies prohibiting source code from leaving client infrastructure, this does not make AI-assisted modernization unavailable.
On-premise or VPC-hosted LLM execution with air-gapped infrastructure resolves the policy requirement directly.
Organizations that have concluded AI-assisted modernization is ruled out by their governance policies have almost always reached that conclusion without evaluating the deployment architecture options available to them.
ColdFusion Modernization at Enterprise Scale: Full-Lifecycle Execution
Knowing which path to select and being able to execute it are two different problems. This section documents what full-lifecycle execution looks like under conditions that are representative of the worst-case enterprise ColdFusion deployment, and what each phase of that execution requires.
Four Ways ColdFusion Modernization Programs Fail Before Transformation Begins
Most ColdFusion modernization overruns are not caused by technical complexity in the target stack. They are caused by decisions made, or skipped, before transformation begins.
- Skipping comprehension. CFML’s procedural structure mixes business logic and presentation throughout .cfm files. Rewriting without first extracting that logic produces systems that compile and pass basic tests, then fail in production on edge cases that were never documented and never visible until a real transaction triggered them.
- Over-relying on static analysis. Tools like SonarQube surface code quality issues and dependency graphs effectively. They do not surface business rule intent embedded in procedural logic, undocumented CFX tag behavior, or implicit dependencies on ColdFusion built-ins. Static analysis is a necessary input, not a sufficient substitute for comprehension.
- No validation baseline. Legacy ColdFusion applications typically carry zero test coverage. Without a test baseline established before migration, there is no objective mechanism for confirming behavioral equivalence after. The resolution: documentation produced in the comprehension phase becomes the specification against which automated test cases are generated before transformation begins.
- Misreading AI governance as a blocker. Policies that prohibit source code from being sent to external LLM endpoints are a deployment architecture constraint, not a ceiling on what AI-assisted modernization can do. On-premise or VPC-hosted LLM execution with air-gapped infrastructure resolves the policy requirement directly.
What The Engagement Looked Like
The following is drawn from Legacyleap’s documented engagement with a global semiconductor manufacturer.
The starting conditions were worst-case by most measures:
- Mandatory migration sequence: ColdFusion → PHP → .NET. Three stages, no shortcuts permitted by internal policy
- Zero documentation across the application estate
- Zero test coverage
- Original developers unavailable
- Strict AI governance policy blocking four major external LLM providers; all LLM outputs required to remain on-premise
- Audit logs required at every governance gate
- SonarQube already in place and confirmed insufficient, because cognitive complexity and embedded business logic were outside its detection scope
Legacyleap’s Assessment Agent and Documentation Agent ran a full comprehension pass first, extracting business logic, APIs, and inter-module dependencies directly from the undocumented source, generating dependency maps and flowcharts, and producing a fitment score for each application.
That documentation became the specification from which the QA Agent generated the full test suite before any transformation began.
Transformation across both stages was diff-based and required engineering sign-off at every step. All LLM inference ran on-premise via AWS Bedrock with air-gapped execution to ensure no source code left the client environment.
Parity was validated against the Phase 1 documentation baseline at each phase gate, not as a post-hoc check.
Outcomes
- 60% faster than manual estimates for comparable scope
- 40–50% lower cost than a manual or SI engagement approach
- Zero sensitive data left the client’s firewall across all three phases
- Full test suite (unit, integration, API, and UI) auto-generated from Phase 1 documentation
- Parity confirmed at every phase gate through differential regression testing
If your deployment shares any of those conditions, the $0 Modernization Assessment is the right starting point as it produces a dependency map, a risk profile, and a path recommendation before any engagement begins.
Starting Your ColdFusion Modernization: The Right First Step
The question of whether to modernize is settled by the four pressure vectors above. What requires a decision is which path is right for your specific deployment, and whether your documentation state, team capability, and governance requirements are addressed before transformation begins rather than discovered partway through it.
The documentation gap is the highest-risk variable in most enterprise ColdFusion deployments. If the original developers are gone, or if the application has grown beyond what any single team fully understands, comprehension precedes everything else.
The profiles in this article identify which organizations face that constraint, and the semiconductor engagement documents what executing against it rigorously actually produces.
If your ColdFusion deployment is on an EOL version, your original developers are unavailable, or your team does not fully understand what the application does, the $0 Modernization Assessment is the right first step.
It produces a codebase dependency map, a risk profile across EOL exposure and documentation gaps, and effort and timeline ranges for the recommended path. No commitment. No engagement required before results are delivered.
Request your $0 Modernization Assessment | Book a Demo
FAQs
Lucee is the right choice for organizations prioritizing cost reduction and containerization with no proprietary ACF dependencies. BoxLang is the right choice for teams already invested in the ColdBox ecosystem with lower regulatory burden and a forward-leaning engineering culture. Neither Lucee nor BoxLang is a substitute for modernizing the application itself. Switching engines while leaving undocumented business logic in place trades one cost exposure for a different structural risk.
Yes. CF 2025 includes improved Docker and Kubernetes support. Lucee has native container support and is the more mature containerization option among CFML engines. Containerization is a deployment improvement, not a modernization strategy. It does not address the underlying application architecture or documentation state.
Organizations on EOL ColdFusion versions that cannot immediately begin a migration program should implement compensating controls: network segmentation to isolate the ColdFusion server from broader infrastructure, WAF rules targeting known ColdFusion attack vectors, monitoring for CVE-specific indicators of compromise, and access restriction to the ColdFusion Administrator interface. These controls reduce exposure but do not eliminate it. CVE-2024-20767 is actively exploited and has no patch available for EOL versions. Compensating controls are a risk reduction measure, not a risk elimination measure.
Java via Spring Boot is the most natural target due to JVM commonality. ASP.NET Core is the preferred target for .NET-capable teams and carries mature compliance certification in regulated US environments. The correct answer depends on your team’s existing capability, not on the languages themselves. A Java replatform executed by a team ramping on Spring Boot simultaneously will underperform a .NET replatform executed by a team with genuine ASP.NET Core depth.
References
[1] Adobe ColdFusion Product Lifecycle — https://helpx.adobe.com/support/programs/eol-matrix.html
[2] Adobe ColdFusion 2025 Subscription Pricing — https://www.adobe.com/products/coldfusion-family.html
[3] CISA Known Exploited Vulnerabilities Catalog — CVE-2024-20767 — https://www.cisa.gov/known-exploited-vulnerabilities-catalog
[4] Adobe Security Bulletin APSB24-14 — https://helpx.adobe.com/security/products/coldfusion/apsb24-14.html