When Enterprises Are Forced to Migrate Application Servers
A WebLogic migration can pass staging validation and fail hours after production cutover. Under load, JTA propagation behaves differently, transaction boundaries shift, and message acknowledgements diverge from baseline behavior. Data inconsistency surfaces only after downstream systems reconcile state, at which point rollback becomes the only containment option.
For many enterprises, WebLogic, WebSphere, and JBoss still sit at the center of revenue-critical systems. These platforms have supported core transaction processing, integrations, and internal workflows for over a decade.
The question today is whether they remain viable under current cost, security, and infrastructure constraints.
Application server migration becomes inevitable when operational risk, cost pressure, and architectural constraints converge. In this context, migration means moving off WebLogic, WebSphere, or JBoss without losing functional behavior or destabilizing production workloads.
Three triggers typically force the decision:
- Support and security exposure: Oracle WebLogic Server 12.2.1.4 Premier Support is scheduled to end on December 31, 2026, with Sustaining Support thereafter, and IBM WebSphere Application Server 9.0.x extended support ends September 30, 2025. These timelines push enterprises into extended or paid support models with higher cost and audit risk as unpatched vulnerabilities mount.
- Cost and licensing inflection: Extended support can add significant recurring fees materially inflating total cost of ownership. For Oracle products, it typically increases by an additional ~10% in the first extended year and ~20% in subsequent years compared to standard support maintenance.
- Cloud and container mandates with runtime friction: In 2025, over 60% of Fortune 500 companies in North America report running Kubernetes-based container platforms, and container usage among IT professionals has reached ~92 %, reflecting how pervasive container-based infrastructure has become.
Application server migration is a risk and execution decision. It impacts uptime, transaction integrity, security posture, and regulatory exposure. The constraint is clear: preserve application behavior while replacing the runtime foundation underneath it.
How to Assess Application Server Migration Readiness (Dependencies, Config, Integrations)
Most application server migration programs slip before execution begins. The root cause is hidden runtime coupling. Estimation without a dependency baseline produces false confidence and late surprises.
Migration readiness starts with a hard inventory. Before selecting a target runtime or refactor path, capture the full dependency signature of the application.
1. Application Packaging and Runtime Coupling
- EAR vs WAR packaging structure
- Shared libraries deployed at the server level
- Classloader hierarchy assumptions
- Use of container-managed services embedded in deployment descriptors
These elements determine how tightly the application depends on WebLogic, WebSphere, or JBoss container behavior.
2. Enterprise Java Feature Usage
Map usage depth and location for:
- EJB (session, message-driven, container-managed transactions)
- JNDI bindings and resource lookups
- JMS providers and messaging patterns
- JTA transaction boundaries and propagation
Superficial presence differs from deep architectural reliance. The migration implication changes accordingly.
3. Security Model and Identity Integration
Inventory:
- Security realms and authentication providers
- JAAS configurations
- SSO integrations
- Certificate handling and trust stores
- Role mappings and container-level authorization
Authentication and authorization behavior must remain stable across runtime shifts.
4. Session State and Clustering Assumptions
Capture:
- HTTP session replication strategy
- Sticky session requirements
- Distributed caching mechanisms
- Stateful session bean usage
State management differences frequently surface only under load.
5. External Integrations
Document all external touchpoints:
- Databases and connection pool configuration
- Messaging systems and broker dependencies
- SOAP/REST integrations
- Batch schedulers and background jobs
Each integration may rely on server-specific configuration models.
6. Runtime Configuration Artifacts
Extract and analyze:
- domain.xml, standalone.xml, server.xml equivalents
- Data source definitions
- Resource adapters
- Thread pool and executor configuration
- Deployment descriptors and environment overrides
Configuration drift between environments must be identified before migration begins.
Dependency Signature → Migration Implication
| Feature Detected | Migration Implication |
| Heavy EJB usage | Refactor or framework migration likely required |
| Container-managed JMS | Externalize messaging or reconfigure provider |
| Deep JNDI bindings | Naming and resource mapping rewrite |
| Stateful session beans | Re-architecture or state management redesign |
| Custom security realms | Identity model reconfiguration |
This assessment phase determines feasibility. It defines the migration path, effort band, and execution risk. It also determines whether replatforming is viable or refactoring is unavoidable.
This is where most teams spend weeks assembling partial views of the system. Automation at this stage reduces uncertainty before execution.
Here is what this looks like in practice. Consider a WebLogic application with 40 EJBs, three JMS queues, a custom JAAS realm, and sticky session clustering across two data centers.
The dependency signature signals deep container-managed transactions, provider-specific messaging semantics, and proprietary security configuration. In this scenario, a simple replatform to another application server is unlikely to preserve runtime behavior without divergence under load.
Transaction propagation, session replication, and authentication mapping would require explicit redesign. The dependency depth points toward controlled refactoring rather than a runtime swap.
This dependency signature directly determines the target selection.
Choosing the Target for Application Server Migration (Replatform, Refactor, Containers)
Target selection in application server migration is constrained by dependency signature. The runtime you move to must align with what the application actually uses, not what the roadmap prefers.
Three target buckets dominate most WebLogic, WebSphere, and JBoss migration programs.
1. Replatform the Runtime
Examples include WebSphere traditional to Open Liberty, JBoss AS to EAP or WildFly, or WebLogic to a lighter servlet container where feasible.
What it preserves:
- Core application structure
- Packaging model
- Most business logic
- Familiar operational patterns
What it forces you to change:
- Server-specific configuration
- Non-portable JNDI bindings
- Messaging provider wiring
- Security realm mappings
Where effort is misjudged:
Teams underestimate configuration drift and integration complexity. Code may compile with minimal change while runtime behavior diverges under load or transaction pressure.
Replatforming is viable when container-managed services are limited and proprietary extensions are shallow.
2. Refactor to Framework-First (Spring Boot, Quarkus)
This path replaces the traditional application server with an embedded runtime model.
What it preserves:
- Business rules and domain logic
- API contracts
- Data model and transaction semantics
What it forces you to change:
- EJB components and container-managed services
- Deployment descriptors
- Centralized configuration assumptions
- Session management model
Where effort is misjudged:
Teams treat EJB-to-Spring migration as a mechanical translation. Deep transactional behavior, lifecycle callbacks, and cross-cutting concerns require architectural redesign.
Refactoring increases long-term flexibility but expands short-term transformation scope.
3. Containerize the Legacy Runtime
This approach packages the existing server into containers to meet infrastructure mandates.
What it preserves:
- Application code
- Runtime behavior
- Operational familiarity
What it forces you to change:
- Configuration externalization
- Deployment automation
- Scaling model
Where effort is misjudged:
Containerization does not eliminate runtime coupling. It defers architectural debt. Licensing and support exposure remain.
Containerization functions as a bridge strategy when immediate refactoring is not feasible.
Dependency Signature → Target Selection Matrix
| Dependency Signature | Viable Target Direction |
| Minimal EJB, shallow JNDI | Replatform feasible |
| Heavy EJB + container services | Refactor required |
| Extensive JMS integration | Replatform with messaging redesign |
| Deep proprietary extensions | Refactor or staged rewrite |
| Infrastructure mandate, limited change tolerance | Containerize as interim step |
Several patterns consistently hold:
- If the application depends heavily on container-managed transactions, expect refactoring.
- If JNDI bindings are embedded across modules, expect configuration rewrites.
- If messaging is tightly coupled to server-managed JMS, expect integration redesign.
- If clustering relies on proprietary session replication, expect state architecture changes.
- If proprietary vendor APIs are present, replatforming risk increases.
Incremental versus big-bang execution is a consequence of target complexity. Replatforming supports a phased rollout more easily. Deep refactoring often concentrates risk unless decomposed carefully.
Target selection defines the effort band, execution model, and risk envelope. It should follow dependency assessment, not precede it.
Replatform, Refactor, or Containerize: How to Choose
Answer these questions about your application to determine the appropriate migration path.
- Do you have more than 20 EJBs or deep container-managed transaction usage?
If yes, structural refactoring is likely required. - Are JNDI bindings embedded across multiple modules and environments?
If yes, expect significant configuration rewrites during migration. - Do you have a near-term mandate to containerize for infrastructure alignment?
If yes, containerization may function as an interim step while architectural changes are deferred. - Does your code rely on proprietary vendor APIs or server-specific extensions?
If yes, replatforming carries elevated runtime divergence risk. - Is the application loosely coupled with limited container-managed services?
If yes, replatforming to a compatible runtime may be viable.
If more than two answers point toward refactoring, treat replatforming as a risk rather than a shortcut.
What Breaks During Application Server Migration and Why
Application server migration failures rarely originate in compilation errors. They surface at runtime, under load, or during integration testing. The breakpoints are consistent across WebLogic, WebSphere, and JBoss programs.
The following components account for most production instability.
Breakage Map: Component → Failure Mode → Fix Pattern
| Component | Typical Failure Mode | Required Fix Pattern |
| EJB | Container-managed lifecycle, transactions, and injection behavior diverge from target runtime | Replace with framework-managed services or refactor to Spring/Quarkus equivalents |
| JNDI | Resource lookups fail due to naming differences and binding model changes | Re-map resources and externalize configuration |
| JMS | Message delivery semantics, acknowledgement behavior, or provider configuration changes | Redesign integration layer and reconfigure messaging provider |
| JTA | Transaction boundaries behave differently across nested calls or distributed flows | Redefine transaction demarcation and propagation rules |
| Security (authn/authz) | Realm mappings, JAAS modules, or role bindings do not align with target runtime | Reconfigure identity providers and authorization model |
| Session State / Clustering | Sticky session assumptions or replication strategies fail under new runtime or container model | Redesign session management and introduce distributed cache where required |
- EJB: Heavy EJB usage signals deep container reliance. Session beans, message-driven beans, and container-managed transactions introduce implicit behavior. When migrating to lighter runtimes or framework-first models, these boundaries become explicit and require refactoring.
- JNDI: JNDI bindings are frequently hard-coded or environment-specific. Differences in naming conventions and resource resolution models create runtime failures. Configuration drift between environments amplifies the risk.
- JMS: Messaging integrations depend on provider-specific semantics, acknowledgment modes, and connection factory configuration. Migration often changes these assumptions. Message ordering and delivery guarantees must be revalidated.
- JTA: Transaction managers differ in implementation details and propagation handling. Nested transactions and distributed transaction flows may behave differently across runtimes. Under load, these differences surface as data inconsistency or rollback anomalies.
- Security: Authentication and authorization failures occur when realm definitions, role mappings, or certificate handling are reinterpreted in the target environment. Identity integration requires explicit mapping and validation.
- Session State and Clustering: Legacy runtimes often rely on proprietary clustering mechanisms and session replication strategies. Containerization or runtime changes alter replication behavior. Sticky session assumptions fail in horizontally scaled environments.
These failure modes are predictable. They follow from dependency depth and configuration coupling. Predictability depends on surfacing these failure modes during assessment, not during UAT.
Migration Execution Plan: Parallel Run, Rollback Gates, and Functional Parity Proof
Application server migration risk concentrates at cutover. Code may compile, and environments may deploy cleanly. Production stability depends on execution sequencing and behavioral parity.
A migration execution plan requires two elements: a controlled cutover model and a measurable parity proof.
Cutover Models
1. Parallel Run
Both legacy and target runtimes operate simultaneously. Traffic is routed selectively. Results are compared before full switchover.
Parallel run is viable when:
- Interfaces are stable and well-defined
- Data consistency checks can be performed safely
- Infrastructure allows duplicate runtime support
It increases short-term operational overhead and reduces go-live uncertainty.
2. Phased Rollout
Modules or services migrate incrementally. Traffic shifts in controlled stages.
Phased rollout is viable when:
- Components are loosely coupled
- Clear functional boundaries exist
- Downstream impact is isolated
It reduces blast radius and requires disciplined dependency mapping.
Rollback Gates
Rollback criteria must be predefined and measurable. Generic “rollback if issues arise” is insufficient.
Define:
- API response mismatch thresholds
- Transaction failure rate limits
- Data consistency variance thresholds
- Latency and throughput baselines
- Authentication and authorization error tolerances
Rollback triggers must be automated or observable in real time. Manual judgment during outage conditions increases downtime risk.
Functional Parity Proof
Functional parity defines whether migration is complete. It must be expressed in observable behaviors.
Baseline the following before cutover:
- API contracts and response structures
- Core business workflows
- Transaction boundary behavior
- Message delivery semantics
- Security role enforcement
- Session state persistence under load
Testing must focus on black-box regression and contract validation. Unit tests alone do not capture integration drift. Load simulation exposes transaction and state anomalies.
Parity completion criteria should be explicit:
- All critical workflows execute without divergence
- Transaction commit and rollback patterns match baseline
- Messaging delivery guarantees are preserved
- No security role regression is detected
- Performance remains within defined tolerance bands
Completion is achieved when runtime behavior under production-like conditions matches the baseline within predefined thresholds.
Automation that generates documentation, test scaffolding, and validation artifacts compresses execution timelines and reduces parity risk.
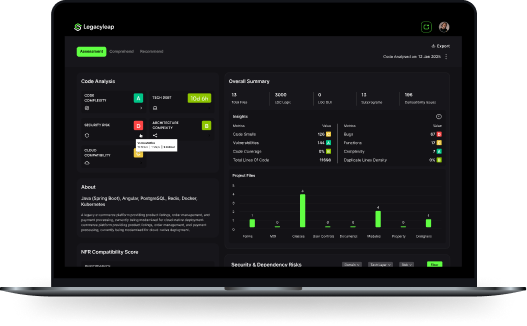
A Predictable Path for Application Server Migration with Legacyleap
Many tools assist developers with code suggestions. Application server migration requires system-level control across dependencies, configuration, runtime behavior, and validation.
Generic copilots operate at the file or snippet level. Application server migration operates at the application and runtime boundary level. The gap between those layers is where most execution risk accumulates.
Legacyleap addresses that gap through four structural capabilities.
1. System Comprehension Artifacts
Legacyleap generates:
- Full dependency graphs across modules
- Mapped usage of EJB, JNDI, JMS, JTA, and security constructs
- Runtime configuration extraction and documentation
- Business and technical documentation artifacts
These outputs convert hidden coupling into observable structure. Estimation and sequencing become data-backed rather than assumption-driven.
2. Controlled Transformation
Transformation is grounded in compiler-level representations rather than prompt-only generation. Guardrails constrain changes within structural boundaries. Refactoring and replatforming actions are applied with awareness of dependency impact.
This reduces unintended behavioral drift during runtime migration.
3. Validation and Parity Layer
Legacyleap produces:
- Test scaffolding aligned to detected workflows
- API-level validation checks
- Transaction and integration verification artifacts
Validation becomes embedded in the transformation process rather than deferred to late-stage UAT.
4. Human-in-the-Loop Checkpoints
Modernization remains governed. Engineers review transformation outputs, adjust configuration mappings, and validate integration assumptions before deployment. Automation accelerates execution. Oversight preserves correctness.
Conclusion: De-Risking Application Server Migration in 2026
Application server migration is rarely blocked by lack of tooling. It is blocked by uncertainty. Uncertainty around hidden dependencies. Uncertainty around behavioral drift. Uncertainty around what happens on cutover day.
The patterns are consistent across WebLogic, WebSphere, and JBoss programs:
- Hidden container coupling inflates scope late.
- Messaging and transaction semantics shift under load.
- Configuration drift introduces environment-specific failures.
- Cutover risk concentrates when parity is assumed rather than proven.
Successful application server migration programs reverse that dynamic. They establish dependency visibility first. They select targets based on actual usage patterns. They define rollback gates before go-live. They treat functional parity as a measurable outcome.
Predictability requires coordinated assessment, transformation, and validation. Fragmented tools and manual analysis extend timelines and amplify execution risk.
Most timeline reduction comes from eliminating rework through early dependency visibility and embedded parity validation, not from faster code generation alone.
Legacyleap provides a structured entry point through a $0 assessment of a representative application.
Deliverables include:
- Dependency signature report
- Configuration and integration inventory
- Identified breakage risks
- Feasible migration path options
- Estimated effort band
These artifacts remain with the enterprise regardless of next steps. They create immediate clarity around scope, sequencing, and execution risk.
Application server migration is a foundational decision. The runtime layer underpins transaction integrity, security enforcement, and operational stability. When the assessment is rigorous and the execution model is controlled, migration becomes a governed transition rather than a high-risk rewrite.
FAQs
Shared application server instances introduce hidden coupling across classloaders, connection pools, security realms, and resource bindings. During migration, each application must first be isolated at the configuration level. This typically involves extracting shared libraries, externalizing environment-specific resources, and separating data source definitions. A phased migration strategy can then move one application at a time to the target runtime while maintaining coexistence. The key constraint is ensuring that resource reallocation for one application does not alter runtime behavior for others still running on the legacy server.
Certification differences require validation at both compatibility and behavioral levels. Start by identifying whether the dependency relies on proprietary APIs or container-managed services. Standard Java libraries often migrate cleanly, but vendor-certified connectors may depend on specific classloader hierarchies, transaction managers, or security providers. Where certification gaps exist, options include upgrading to runtime-neutral versions, replacing the connector, or isolating the integration behind an adapter layer. Legacyleap’s dependency signature analysis surfaces proprietary API usage early, allowing teams to quantify compatibility risk before selecting a target runtime.
Scheduled jobs, timers, and batch workloads often rely on container-managed schedulers or server-specific thread pools. During migration, these jobs must be mapped to equivalent scheduling mechanisms in the target environment, such as framework-level schedulers or external orchestration platforms. The migration plan should include validation of execution frequency, transaction boundaries, retry logic, and idempotency behavior. Batch workloads require special attention under load, as thread management and resource contention may behave differently in the new runtime.
Configuration migration requires parallel environment preparation and controlled cutover sequencing. Extract all runtime artifacts (data sources, JNDI bindings, JMS providers, security realms, and thread pools) into version-controlled definitions before altering production. Stand up the target runtime in parallel, validate configuration equivalence, and test behavior under simulated load. Cutover should occur behind routing controls or traffic-shaping mechanisms that allow rollback if parity thresholds are breached. Legacyleap accelerates this process by generating structured configuration inventories and mapping artifacts, reducing manual reconciliation errors during switchover.
Operating beyond Premier or extended support increases exposure to unpatched vulnerabilities, compliance audit findings, and incident response delays. Security patches may no longer be issued, and vendor escalation paths become limited. Regulatory environments that require supported software versions may classify unsupported runtimes as audit exceptions. Beyond security, infrastructure modernization becomes constrained as newer operating systems, JVM versions, and container platforms may not be certified against unsupported application server releases.